Washington, DC (Eastern Region)
Wednesday, May 5, 2021
Virtual
Keynote Speaker
““How technology innovation is increasing the complexity of the CISO’s security responsibilities””
Alicia Lynch
Senior Vice President, Chief Information Security Officer Cognizant
CISO/Industry Leader Panel
“The New (& Ongoing) Challenges of Third Party Risk"
Janalyn Schreiber
Partner Data Privacy & Security Advisors LLC
Vicky Ames
Director, Information Security, Risk and Compliance United Therapeutics Corporation
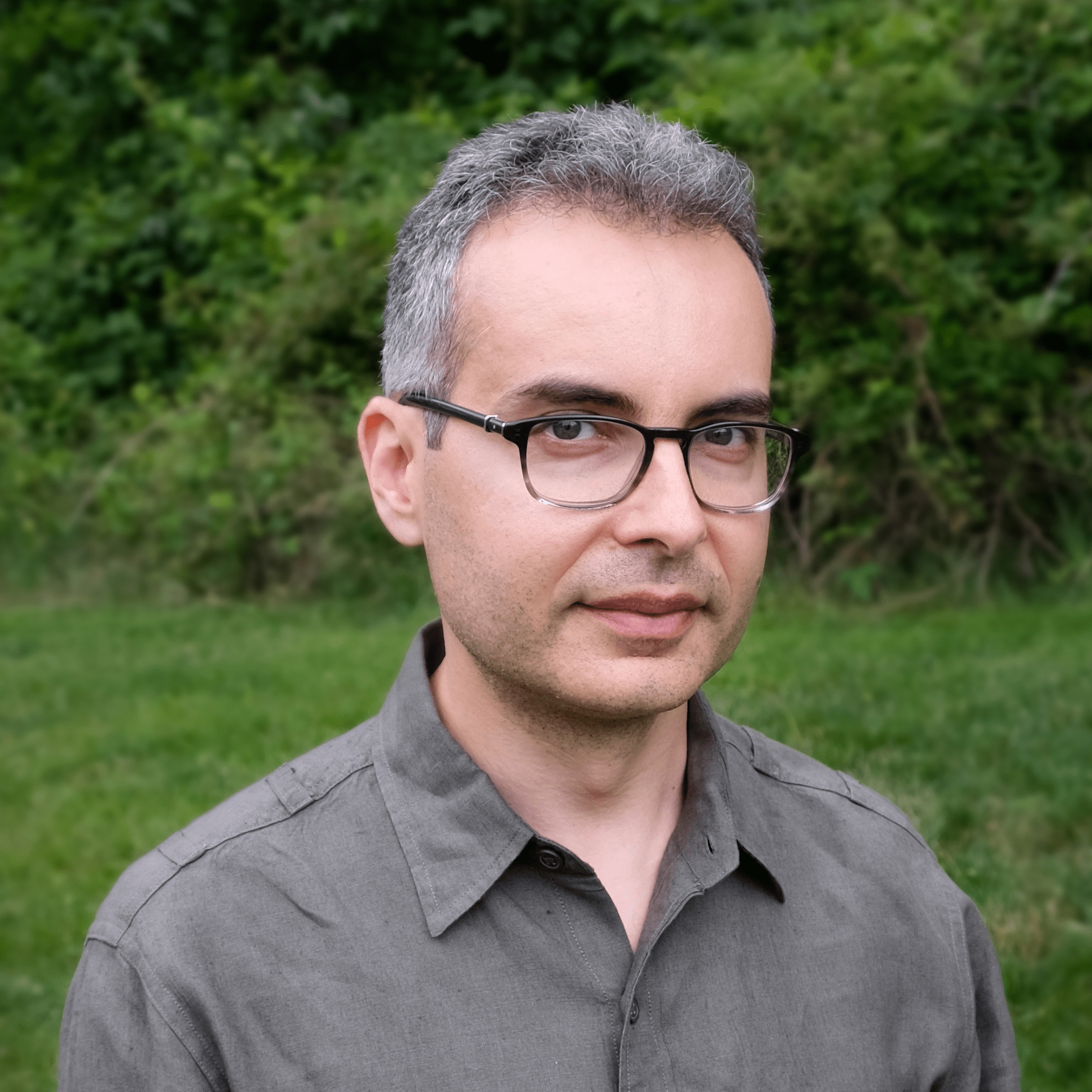
Dr. Andrea Little Limbago
Vice President, Research and Analysis Interos Inc.
Deb Briggs
CSO - Chief Security Officer Netscout Systems
Monica Keeneth
Chief Information Security Officer Inovalon
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions
Presentation
Reflections of a New CISO: 5 Lessons Learned
Sponsored by

Presentation
7 habits of highly successful cybersecurity operators
The unpredictable nature of the cybersecurity analyst’s job makes the day-to-day challenging to say the least. Too many alerts, too many tools to keep up with, and too much pressure to get it all right. There are powerful lessons that can make the daily job of the operator more beneficial to the organization and can lead to personal change. This session presents a holistic, integrated approach for solving the pressing problems, adapting a growing attack surface and taking advantage of opportunities created by change.
Sponsored by

Live Keynote
“How technology innovation is increasing the complexity of the CISO’s security responsibilities”
Presentation
Stay Ahead – Prep and Protect Your Enterprise for a Post-Pandemic World
Organizations worldwide transformed their ways of working with the onset of the COVID-19 pandemic. Now, we’re all forced to face new uncertainties as we transition to a post-pandemic world. Meanwhile, threat actors and cyber criminals are evolving their tactics to take advantage of these hazy times and of the pandemic’s disruption as seen by recent surges in attacks across all industry sectors. This new phase of the modern workforce threatens more disruptive change and unpredictability. Join us to better understand what organizations such as yours should be focusing on to avoid being the next victim and stay a step ahead of the world’s leading cybercriminals.
Sponsored by

Live Panel Discussion
“The New (& Ongoing) Challenges of Third Party Risk"
Presentation
Employees are not the Enemy: Insider Risk and Employee Trust in the Enterprise
Sponsored by
Presentation
Come to the Dark Side: Exploiting the Criminal Underground for CTI
Sponsored by

Presentation
The Malware Lab: Rethinking Enterprise File Analysis
Cyberthreats represent one of the most significant risks to modern businesses. Malware is pervasive; embedded in videos, hidden in software updates, and uploaded by unsuspecting customers. Yet the tools to investigate these threats are often manual and burdensome to maintain. Organizations recognize these challenges, but simply don’t know how to get started.
This session is a great opportunity to hear about a growing trend from one of ReversingLabs experts, Chip Epps. Chip will discuss centralizing the challenging tasks of investigating files and providing actionable intelligence to the entire organization. Some other areas of focus include:
- Streamlining file analysis and making security more responsive and proactive
- Why centralizing malware research into an enterprise “Malware Lab” is both efficient and effective
- How to benefit all lines of business and reduce cyber risks
Sponsored by

Presentation
Active XDR --- Changing the Game in Favor of the Defender
Active XDR solutions integrate deception technologies with traditional XDR capabilities to help SOC teams proactively find, deceive, and defeat advanced cyber threats earlier in the attack lifecycle. It changes your defense posture from passive alert monitoring to active engagement by unifying endpoint, network, cloud and deception technologies to enabling SOC analysts to find, assess, and remediate known and unknown threats before they cause business damage. Active XDR solution help organizations emerge stronger and more secure. This presentation discusses how to apply both MITRE ATT&CK and MITRE Shield frameworks to optimize the set of technologies in your organizations security stack to counter an adversary and ultimately help change the game in favor of the defender.
Sponsored by

Identity Cloud Checklist
Sponsored by

Presentation
Creating a Future-Ready, Passwordless Organization Today
The world of work has changed dramatically and perhaps permanently. With remote work being the new norm, users must access services and data from outside the corporate firewall. How does IT support your widely disbursed workforce while at the same time following advanced Zero Trust best practices?
When it comes to user authentication technology, striking this balance to protect access to physical systems and cloud-based applications in a seamless way is an increasingly important consideration for IT and cybersecurity professionals. In this webinar, HID Global’s Identity and Access Management Product Director Yves Massard takes a deep dive into creating a future-ready passwordless organization today.
Sponsored by
Presentation
2021 State of Malware
Over the past year, the tools and tactics of cybercrime and cybersecurity adapted against a backdrop of enormous changes to our lives and businesses.Join us to learn how cybercrime evolved in 2020, and identify ways to safeguard your organization against what’s out there.We’ll explore:
- Top threats for businesses and consumers
- Emerging cybercrime trends and tactics
- Solutions you can employ to thwart future attacks
Sponsored by

Closing Remarks
CISO Bourbon Happy Hour
Sponsored by