Toronto Cybersecurity Conference
Thursday, April 23, 2026
Hybrid
370 King Street West, Toronto, ON M5V 1J9, Canada


























Join Us in Toronto for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
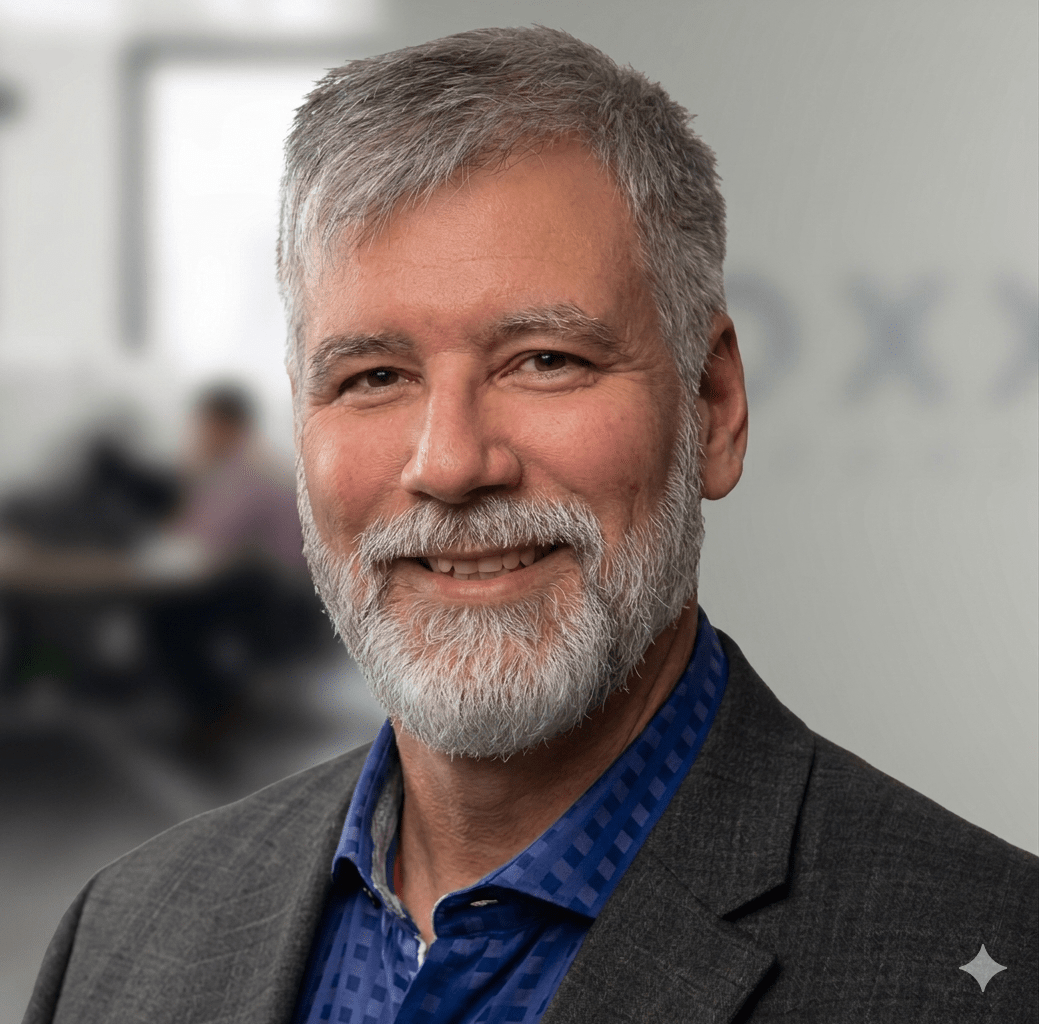
Keynote Speaker
“Cybersecurity as a Boardroom Conversation: What Leaders Get Wrong”
Kalyan Chakravarthy
Chief Information Officer Electrical Safety Authority
I’m a business and technology leader who thrives on turning big ideas into real results. Over the last 20+ years, I’ve worked across private, public, and non-profit sectors—leading teams, transforming organizations, and delivering strategies that stick.
Today, as VP, eSAFE & CIO at the Electrical Safety Authority, I’m focused on driving digital modernization, aligning technology with business priorities, and building high-performing teams that deliver. I believe leadership is about setting a clear vision, empowering people to succeed, and creating a culture where innovation and accountability go hand in hand.
My journey has taken me through leadership roles at GE, IBM, the Toronto International Film Festival, and the Region of Durham, tackling challenges from customer experience redesign to enterprise transformation.
Outside of my executive role, I serve on the Board of Directors at Durham College as Chair of the Nominating Committee, helping shape governance and leadership for the future.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Sponsors
Platinum Sponsors

Gold Sponsors







Silver Sponsors














Partner






“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
AI in Cybersecurity: Friend, Foe, or Both?
Sponsored by

Presentation
2026 Threat Report
Sponsored by

Presentation
The Siege You Can’t See: Why APIs Are the Internet’s Biggest Vulnerability
APIs power every click, swipe, and login. That silent, lightning-fast conversation between services is under siege, and most security leaders can’t even see the battlefield. Attackers have industrialized API attacks, yet visibility into API activity and risk remains dangerously low.
This session pulls back the curtain on the API threat landscape. You’ll see the data, understand why traditional security tools often fail to identify API risks, and learn how to discover, inventory, and protect your API ecosystem. But APIs don’t just move requests, they move sensitive data. We’ll explore how organizations can better protect PII, payment information, intellectual property, and other critical data flowing through APIs.
We will also examine real-world examples of API vulnerabilities and data exposure, including an exposed GraphQL endpoint leaking customer records and a misconfigured REST API handing out administrative credentials. You’ll learn how to identify potential data leakage and security gaps before attackers exploit them. Don’t defend blind. Come see the siege, then learn how to stop it.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
The Path to AI Nirvana is Through Unified Identity
As organizations race to deploy AI agents, training pipelines, and autonomous workflows, a critical foundation is playing catch-up: identity. Without a unified, cryptographically backed identity framework—one that extends seamlessly across humans, AI agents, CI/CD pipelines, and arbitrary workloads—every layer of the AI lifecycle is exposed to unauditable, ungovernable risk.
This talk argues that cryptographic identity is not merely a security best practice but the essential building block for trustworthy AI. From model training environments where data provenance and access control determine integrity, to production systems where autonomous agents act on behalf of users and organizations, the ability to authenticate, authorize, and audit every actor in the chain is what separates experimentation from enterprise-grade AI. We will explore how a unified identity plane eliminates the fragmented, secret-laden approaches dominating today’s infrastructure and why organizations that solve identity first will unlock AI’s full potential: securely, at scale, and with confidence.
Sponsored by

Presentation
Prediction Is Not Protection
Application security has become a forecasting exercise.
We rely on CVEs, scanners, and severity scores to predict what might go wrong. But in an AI-driven world, where code ships faster and attacks move faster, prediction is no longer enough.
Forecasts don’t tell you what’s being exploited. They don’t tell you what’s reachable. And they don’t tell you what’s under attack right now.
This talk shows why forecast-only security breaks down in the machine-speed-era, and what replaces it.
You’ll see how runtime visibility changes application security from a guessing game into an operational discipline – revealing real attack paths, reducing noise, and enabling teams to detect and stop attacks in production.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
Cybersecurity as a Boardroom Conversation: What Leaders Get Wrong
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
AI-generated code: Maximize gains, minimize risks
AI coding assistants promise massive productivity gains, but recent academic research shows they also introduce instability, security weaknesses, and developer overconfidence. In this talk, I present data from large-scale studies demonstrating how AI-generated code affects delivery performance, vulnerability rates, and developer decision-making. I then outline a practical, end-to-end approach for reducing AI-induced risk while preserving the benefits of AI-assisted development.
Sponsored by

Presentation
The AI Identity Crisis: Protecting the 2026 Perimeter
The traditional security perimeter has dissolved into a series of invisible conversations. As organizations move to autonomous AI workflows, we have entered the era of the “Agentic Web” where AI doesn’t just answer questions, it reads our emails, browses our web pages, and calls our APIs.
From “unintended leaks” where well-meaning employees accidentally feed corporate strategy into personal AI tools, to “Indirect Prompt Injection” where an AI agent is hijacked by a malicious email it was simply trying to summarize, the attack surface is now probabilistic, not just deterministic. We will explore how to regain control using a unified architecture of Zero Trust and AI Gateways that verifies the identity of the user, audits the intent of the machine, and redacts sensitive data in real-time before it ever leaves your control.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Cybersecurity Stacks Don't Fail - Accountability Gaps Do
Sponsored by

Presentation
Evolution of the Security Organization in the Era of AI - AI Maturity Model for Cybersecurity.
Sponsored by
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!