Tampa, FL (Eastern Region)
Thursday, October 7, 2021
Virtual
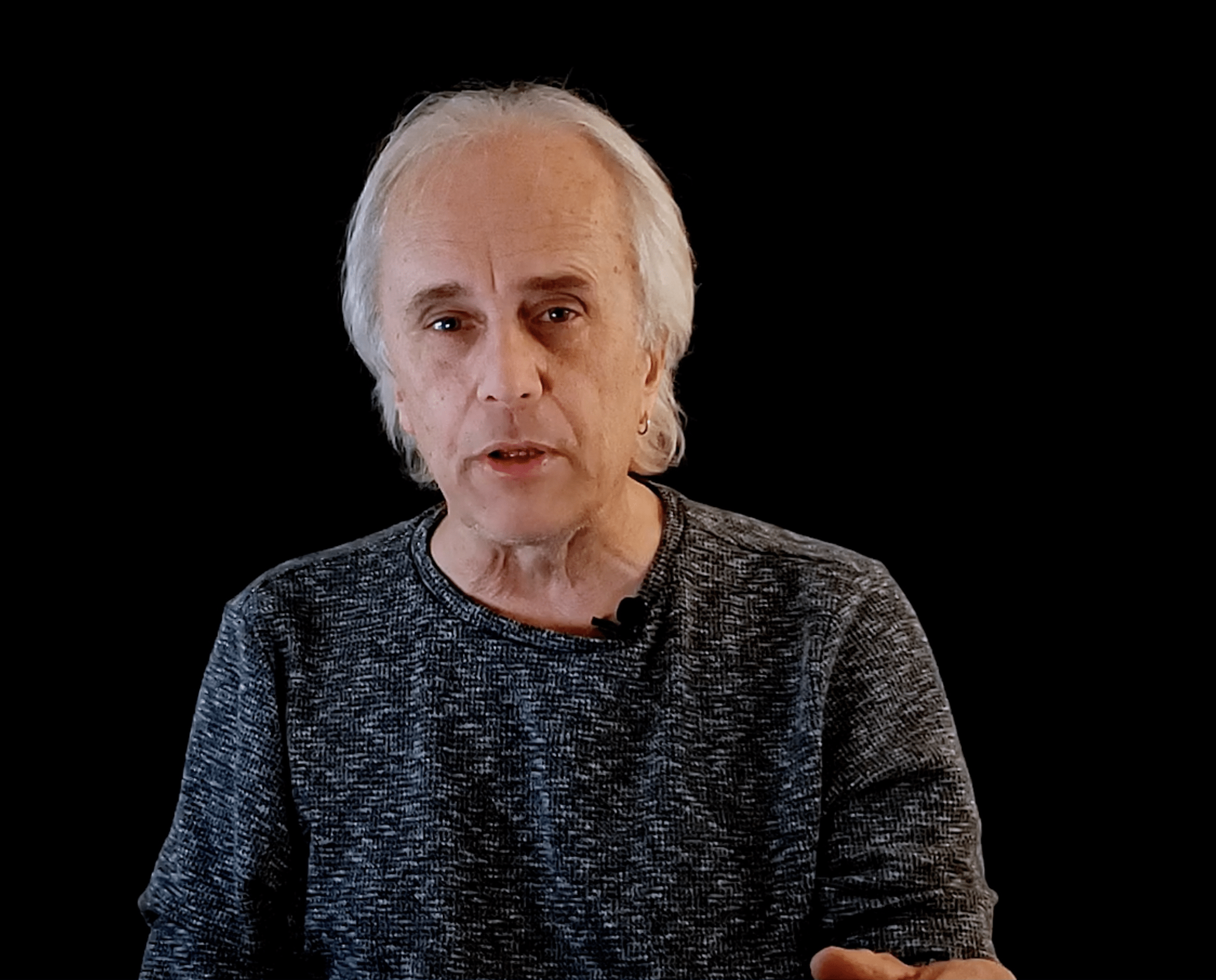
Keynote Speaker
“"Stolen Plastic"”
Scott Schober
President and CEO Berkeley Varitronics
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions
Presentation
Modern Security Programs – IT Evolution to Security Revolution
The IT Revolution we have experienced over the last few years has forced organizations to their own security revolution. The degradation of the perimeter, the growth of BYOB devices, cloud migrations and human behavior are all factors that can bring an organization to its proverbial knees.
What must an organization do to maintain its business and operational excellence? It must build a Modern Security Program based on threat intelligence, predicted outcomes, a layer of defenses and security expertise. That Security Program must be able to prevent, detect, respond AND remediate on a 24 x7 schedule.
Sponsored by

Rise of Secure Access Service Edge (SASE)
Secure access service edge has quickly emerged as a hot topic in cybersecurity, but what exactly does it mean and why should organizations care? As cloud migration, BYOD adoption, and remote work have skyrocketed in prevalence, it has become increasingly apparent that organizations need to think differently about security. While legacy tools like firewalls are no longer equipped to handle the modern IT ecosystem, SASE platforms like Bitglass are built for this exact moment. In this presentation, you will learn:
- The core components of a SASE platform like Bitglass.
- The functionality you need to secure cloud, web, and remote access use cases.
- Architectural considerations you should keep in mind when comparing SASE vendors.
Sponsored by

Presentation
Crawl, Walk, Run Your Segmentation Approach
Sponsored by

Panel Discussion
"Discussing the Future of Ransomware"
Presentation
Counter-Maneuver: Building A Security Program That Moves At The Speed Of Adversaries
Attackers must maneuver through a series of devices on your network to be successful. Your goal as a defender is to be able to observe those maneuvers and deploy defensive actions fast enough to prevent major consequences. This talk will propose a simplification of modern security architecture that will dramatically improve organizations’ ability to investigate at speed, and thus keep up with adversaries.
Sponsored by

Presentation
Securing Trust - How The Security Leader Enables Business Outcomes
What is the value of trust for a company, and what role does a security leader play to enable it? Join Advisory CISO Helen Patton in this informative session, where she will discuss the factors that make a company trustworthy, how a security team builds trust within an organization, and actionable suggestions for improving security and trust in your organization.
Sponsored by

Presentation
From Zero to Full Domain Admin: The Real-World Story Of A Ransomware Attack
Following in the footsteps of a cyber-criminal and uncovering their digital footprint. This is a journey inside the mind of an ethical hacker’s response to a ransomware incident that brought a business to a full stop, and discovering the evidence left behind to uncover their attack path and the techniques used. Malicious attackers look for the cheapest, fastest, stealthiest way to achieve their goals. Windows endpoints provide many opportunities to gain entry to IT environments and access sensitive information. This session will show you the attacker’s techniques used and how they went from zero to full domain admin compromise that resulted in a nasty CryLock ransomware incident.
Sponsored by

Presentation
The Unreserved Chris Roberts: vCISO, Hacker, Devil's Advocate
Hear from this world-class hacker about his use of communication and strategical conversations to create an impact on the cyber world!