St. Louis, MO
Wednesday, July 13, 2022
Hybrid
Keynote Speaker
““What is cyber security anymore; and how will it continue to be defined?””
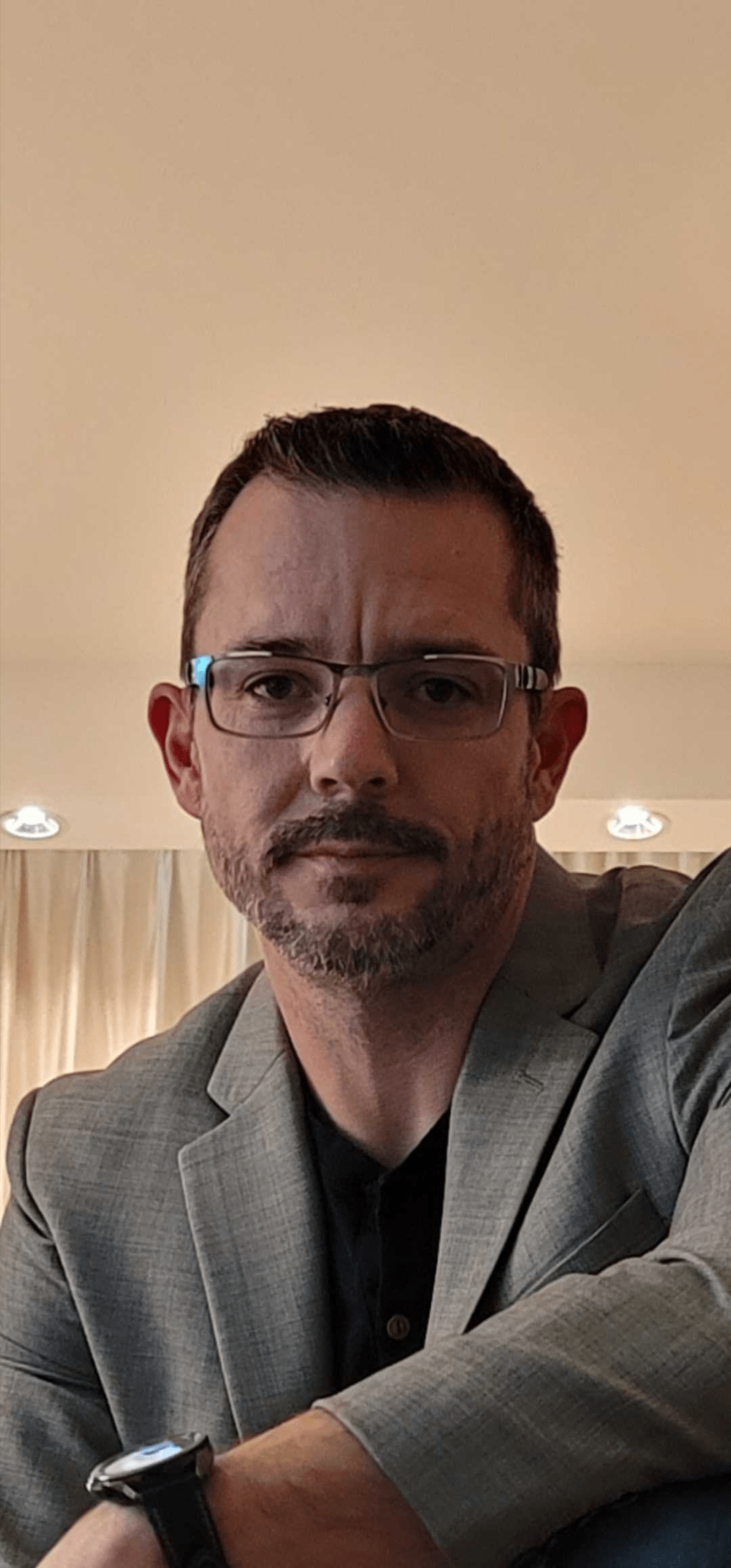
Brent Bettis
VP, Information & Operations Technology Services & CISO Peabody Energy
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Marc Ashworth
Chief Information Security Officer - Senior VP First Bank
Zachary Lewis
CIO and CISO University of Health Sciences and Pharmacy in St. Louis
Tim Marsden
Chief Information Security Officer Stifel Financial Corp.
Rebecca Harness
VP, Chief Information Security Officer Quickbase
Andrew Wilder
Adjunct Professor - Cybersecurity Washington University
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Zero Trust for Applications
Sponsored by

Presentation
Key Considerations for Choosing the Right Email Security Platform
Email is both a necessary communication medium, and the most vulnerable area for an attack. Year after year, adversaries find success in abusing email to gain a foothold into an organization—deploying malware, leaking valuable data, or stealing millions of dollars.
Unfortunately, email threats are only growing in number. Business email compromise accounts for 44% of all losses to cybercrime, and the 2021 Verizon DBIR holds that phishing remains the top entry point for breaches—a position it has held for years.
Does that mean email is doomed, and we should give up? Quite the opposite—instead, we should look to newer technologies and an integrated security strategy that provides a modernized approach to email defense.
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
It Takes More than Automated Compliance to Get Ahead of Threats
In a 2021 survey of CIOs, respondents cited limited resources, new or changing regulations and tracking and maintaining compliance as the top three challenges keeping them up at night. With teams stretched thin trying to keep up with compliance requirements and growing numbers of threats and stakeholder demands, manual processes can no longer keep up.
Automation is a strong first step in reducing manual work and freeing up your team’s workload. However, it is insufficient if it doesn’t help your InfoSec leaders clearly communicate the risk associated with the organization’s business priorities so they can make informed, data-driven investment decisions.
The ability to focus on strategic business priorities helps optimize the talents of small InfoSec teams. When you automate the more tactical and routine work, a more reliable and comprehensive approach to GRC is created while optimizing your teams’ talent by freeing them from manual work.
Join us as we discuss how taking a strategic approach to risk management combined with automation can ensure that businesses stay ahead of the threats they face every day.
Attend this webinar and learn how to:
- Focus your planning efforts around your organization’s strategic business priorities
- Be more proactive by automating evidence collection, risk scoring and monitoring
- Gain actionable insights to help you clearly communicate with key stakeholders
Sponsored by
Presentation
Stopping Attacks, Not Your Business: AI & Autonomous Response
Fast-moving cyberattacks can strike at any time, and security teams are often unable to react quickly enough. Join to learn how Autonomous Response takes targeted action to stop in-progress attacks without disrupting your business. The discussion includes real-world threat finds.
Explore today’s threats and challenges and learn how advances in AI have been leveraged to allow for very surgical actions to be taken
Sponsored by
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Break
Lunch
Keynote
“What is cyber security anymore; and how will it continue to be defined?”
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Is Your Defensive Stack Ready For A Targeted Attack?
Understanding the potential risks in a security program leads to a healthy security program. Penetration testing allows for this identification of risk, but frequent or continuous testing is not widely adopted across the industry. Automated Security Validation (ASV) allows organizations to identify and close any gaps by continually putting existing tools and controls to the test, and focusing on impact-based remediation vs. generic severity to make decisions. We will discuss in depth how taking an offensive approach, through Automated Security Validation, enhances a team’s current defensive strategies.
Sponsored by

Presentation
Cameras, CACs & Clocks: Enterprise IoT Security Sucks - A Story of Two Million Interrogated Devices
Enterprise Internet of Things (IoT) security today is analogous to IT security in the mid 1990s. It was a time when security awareness was limited, countermeasures and best practices weren’t broadly applied, and attackers explored, compromised, controlled, and exfiltrated data from systems with minimal resistance. In short, enterprise IoT security sucks as bad today as that unpatched Windows NT 3.51 server with an RS-232 connected modem that IT forgot about.
Working globally with Fortune 500 enterprises and government agencies for the past six years, we’ve interrogated over two million production IoT devices. Across these two million devices we’ve identified threats and trends, compiled statistics, summarized compelling cases, and evaluated common offenders. We’ve also assembled tactics that organizations can employ to recognize value from their IoT devices while minimizing risk and ensuring that devices that are secure today will stay secure tomorrow.
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Why do we accept gaps in our data protection practices
For years, organizations have struggled to meet the requirements of regulatory compliance, incident response, security and best practice for their critical data.
And now, with the huge upsurge and modernization of business applications and the pressure to migrate to the cloud or to manage a hybrid environment, data security and compliance requirements are evolving to the point where traditional solutions are no longer enough to provide every answer, and the demand for a modernized data security solution is growing .
Modern Data Security requires:
- Support for any location, Multi-cloud, on-prem, both.
- Coverage for any data type
- Augmenting hard to find expertise
- Building Data security into Business Processes
Join Imperva’s Terry Ray to learn what to consider when modernizing your data security solutions to meet the constantly changing security challenges of the modern enterprise.
Sponsored by
Presentation
Cyber Insurance Meets Security Operations
Cyber Insurance is critical to enterprise risk management strategies. Taking the time to understand your policy and knowing what to expect when there is an incident are equally important.
Join Us to Discuss
- Lessons learned from recent incident investigations
- What to expect when you file a cyber insurance claim
- Which security controls are the most important
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!