Seattle, WA
Thursday, February 29, 2024
Hybrid
























Join FutureCon CyberSecurity Events in Seattle!
This event is the perfect opportunity to discover cutting-edge security approaches and learn how to manage risk in the ever-changing cybersecurity world.
Keynote Speaker
“"Elevating Your Cybersecurity Program: Key Priorities for CISOs"”
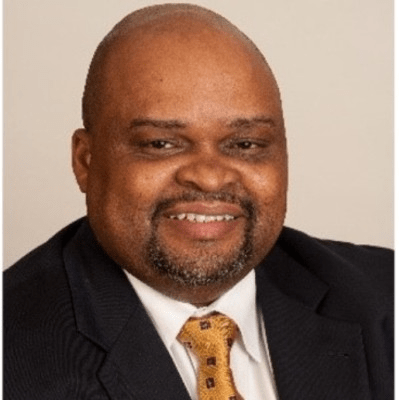
Dr. William Lidster
CISO, Senior Manager of Information Security and Compliance AAA Washington
William serves as the leader of AAA Washington’s information security and compliance efforts. He is responsible to establish a responsive, dynamic, and flexible program to meet continually changing information security, regulatory, and compliance needs in the organization. William serves on the advisory board that establishes required security standards across all of AAA’s federated clubs. William has 25 years of experience in this field, serving in similar roles for Puget Sound Energy, Providence Health and Services, Alaska USA Federal Credit Union, and the State of Alaska’s Department of Public Safety.
William has a Computer Science degree from the US Military Academy at West Point, a Masters in IT and an MBA from University of Maryland, and a PhD in Information Security and Assurance from Capella University.
Outside of his work at AAA, William is a part-time adjunct professor at the University of Washington and Penn State University teaching graduate and undergraduate courses in cybersecurity and enterprise architecture.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Eva Benn
Offensive Security Senior PM Manager @ Microsoft | Co-Founder @ Women in Tech Global | Board Director @ ISACA
Marivell Alicea-Gamlin
Cyber Security BISO Analyst | ISC2 | Cyber Security Leader CBRE
Bryce Matsuoka
vCISO Above Cloud
Andy Stewart
ISSA Board Secretary | Region Cybersecurity Officer CommonSpirit Health
Timothy Youngblood
Former CISO T-Mobile | Angel Investor | PNW Cyversity
Sponsors
Premier Platinum Sponsors

Gold Sponsors






Silver Sponsors















Partner






About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
The Future of Identity
Sponsored by

Presentation
The What, Who For, and Why of MXDR
In this talk, we will first explain what Managed Extended Detection and Response (MXDR) is – given the ‘acronym soup’ of detection and response solutions (XDR, MDR, NDR, EDR, CDR, etc). Next, we will delve into why mid-market organizations should integrate MXDR into their security strategies – focusing on the specific profiles of security teams that benefit most from its implementation. The presentation will be capped with two to three customer case studies, demonstrating MXDR’s practical impact in real-world scenarios. Attendees will gain a clear understanding of MXDR’s advantages, its applicability to various organizations, and actionable insights from successful deployments
Sponsored by
Sponsor Networking Time
Presentation
Unlock Shift Left: Right Teams, Right Tools, Fixed Problems
To match the pace of API-driven development, it’s essential to implement a proactive approach to security testing. However, organizations struggle despite a strong desire to integrate security into software delivery cycles effectively. This talk will dive into the “how” of shifting left, focusing on three key principles: people, process, and technology.
Sponsored by

Cloudflare Threat Radar - Current Trends and Recommendations
What are the current cybersecurity trends and recommendations to prevent and mitigate
Sponsored by

Sponsor Networking Time
Lunch
Keynote
"Elevating Your Cybersecurity Program: Key Priorities for CISOs"
As we truly put the pandemic behind us, we should look forward and ensure we have a new vigor to our information security program. We should be looking at how we can assure stakeholders that we have a strong and resilient program. This requires a shift in how we position ourselves in the organization and how we communicate our risk management performance.
This discussion covers five topics that cyber risk managers should consider moving forward to improve the organization’s risk posture.
Sponsor Networking Time
Presentation
Bringing DevSecOps to Cloud Security
The threat landscape is continuing to expand and diversify as organizations move to a multi-cloud environment. CISOs need to ensure that their DevSecOps capabilities are incorporated within their overall business strategy to guarantee that their cloud applications and code can remain secure.
Topics covered:
· Understanding there is no one-size-fits-all model for DevSecOps
· Best practices for integrating DevSecOps into your cloud security strategy
· Exploring the intersection between development, security and DevSecOps
Sponsored by

Presentation
DRIVING INTELLIGENCE WITH MITRE ATT&CK: LEVERAGING LIMITED RESOURCES TO BUILD AN EVOLVING THREAT REPOSITORY
Building threat intelligence is challenging, even under the most ideal circumstances. But what if you are even more limited in your resources? You are part of a small (but skilled) team, with high expectations, and people are relying on you to make business-critical decisions…all the time! What do you do in that situation? Turn a Toyota Tercel into a tank, of course. The Interpres Security threat intelligence team found itself in that exact situation. Wanting to leverage the MITRE ATT&CK catalog in creating a comprehensive and timely threat intelligence repository, the Interpres team built a series of tools, processes, and paradigms that we call Intelligence Engineering. In this talk, we’ll examine how we combined ATT&CK, STIX2, the Vertex Project’s open-source intelligence platform, Synapse, and custom code to deliver meaningful, rapid, verifiable intelligence to our customers. We’ll share lessons learned on automation, how to run multiple ATT&CK libraries side-by-side, and making programmatic intelligence delivery scalable and effective – just like building a tank out of an imported sedan.
Sponsored by

Sponsor Networking Time
Presentation
Protective DNS Unleashed: A Ransomware Defense Strategy
In today’s ever-evolving threat landscape, securing your assets and infrastructure has become a formidable challenge. Traditional defense walls have fallen with rise on-the-go workforces and the relentless onslaught of cyber adversaries. But fear not, there’s a beacon of hope—protective DNS.
In this session, we’ll break down the power of protective DNS as a pivotal element in safeguarding your business against ransomware and other insidious threats:
- Unmasking the Phishing Threat: How deceptive phishing tactics open the door to digital mayhem and how to spot them to keep your organization safe.
- Multi-Layered Defense with DNS Filtering: Discover why the DNS layer is your first line of defense and how it can safeguard your assets and infrastructure from ransomware attacks.
- DNS-Based Threat Intelligence: The importance of purpose-built intelligence can be used to better detect and prevent zero-day threats at the DNS layer before they strike.
- Compliance and Security Frameworks: Protective DNS isn’t just a nice-to-have; it’s increasingly essential for staying compliant with the big cybersecurity standards like ISO 27001, CMMC, and NIST.
Sponsored by

Sponsored by