Seattle, WA (Western Region)
Wednesday, July 7, 2021
Virtual
Keynote Speaker
“No More Kicking the Can Down the Road – Five Things We Have to Finally Grapple With”
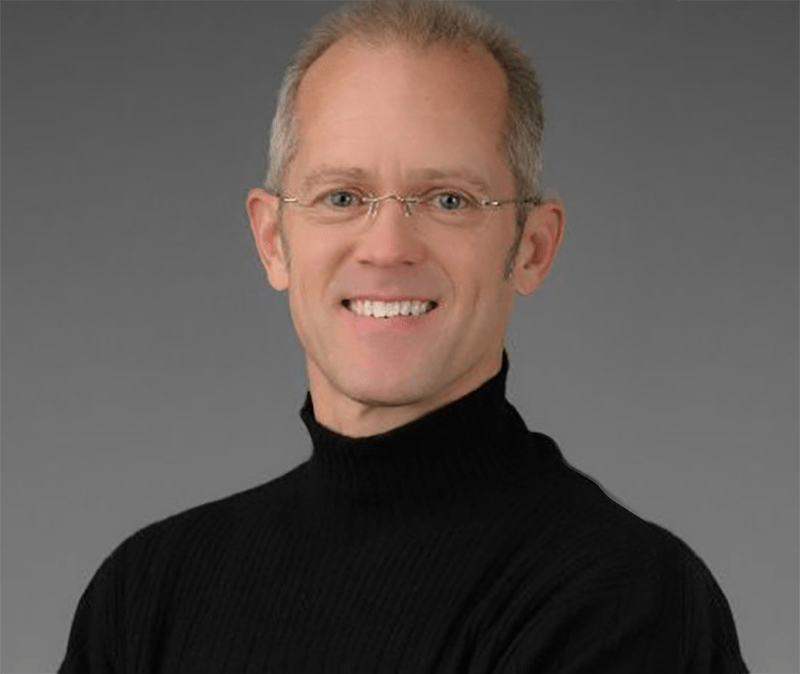
Dr. William Lidster
CISO, Senior Manager of Information Security and Compliance AAA Washington
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
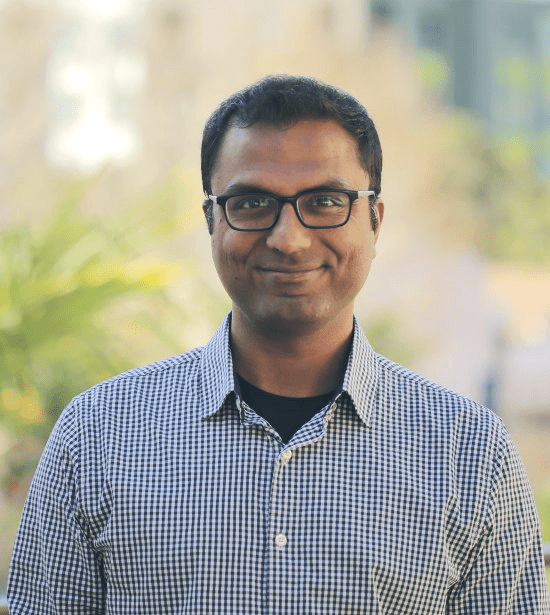
DJ Sampath
Co-founder and CEO Armorblox
Jonathan Kimmitt
Chief Information Security Officer, Alias Cybersecurity Former CISO The University of Tulsa
Brian Grayek
vCISO Cosant Cyber Security
Dr. William Lidster
CISO, Senior Manager of Information Security and Compliance AAA Washington
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Live
Opening Introductions
Presentation
5 Ways to Optimize Your SOC
As more and more businesses adopt a SOC team for managing operations, the scope of work for SOC managers and operators continually grows. More sources, more events, and higher expectations. In this session, Jamie Zajac, VP of Product at Recorded Future will speak to 5 ways you can optimize your SOC, emphasizing changes you can make that don’t require you to buy new tools promising to be a silver bullet.
Sponsored by

Presentation
The Battle of Algorithms: How AI is beating AI at its own game
Among rapidly evolving technological advancements, the emergence of AI-enhanced malware is making cyber-attacks exponentially more dangerous, and harder to identify. As AI-driven attacks evolve, they will be almost indistinguishable from genuine activity, and conducted at an unprecedented speed and scale. In the face of offensive AI, only defensive AI can fight back, detecting even the most subtle indicators of attack in real time, and respond with surgical actions to neutralize threats – wherever they strike.
In this session, discover:
- How cyber-criminals are leveraging AI tools to create sophisticated cyber weapons
- What an AI-powered spoofing threat may look like, and why humans will not be able to spot them
- Why defensive AI technologies are uniquely positioned to fight back
Sponsored by
Live Keynote
No More Kicking the Can Down the Road – Five Things We Have to Finally Grapple With
Keynote will discuss the five things security just has to get in front of.
- Breach Detection and Response Technologies – Vendor Focus
- IoT Security – Developers
- Supply Chain Security – Business (with security advising/supporting0
- Risk Management and Communication – CISOs
- Protecting Operational Technology – Everyone
Presentation
10 Key Components for A Successful 2021 PAM Strategy
2021 is here and many security and IT professionals are faced with the same question: What will the new workforce look like from a people perspective and what security implications do I need to look out for?
Join BeyondTrust to get the winning recipe of how to enable the long-term PAM success. BeyondTrust’s Deputy CTO, Chris Hills will discuss 10 key considerations for building your 2021 PAM strategy that will enable you to be more efficient and secure while effectively supporting employees in the year(s) ahead.
Join this session to learn about:
- The evolution of PAM digital security
- 3 pillars of Privileged Access Management
- 10 must-haves for a successful PAM strategy
Sponsored by

Live Panel Discussion
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Hear from cybersecurity leaders and experts on:
- Current cybersecurity threats and practices
- Post-pandemic security
Jonathan Kimmitt
Chief Information Security Officer, Alias Cybersecurity Former CISO The University of Tulsa
Presentation
MITRE ATT&CK and LogRhythm
Sponsored by

Presentation
5 Lessons Learned Fighting Ransomware
There are many threats to your data. These threats can be intentional, accidental or downright malicious. In this session, see from the eyes of a leading backup provider (Veeam) what you can learn from organizations who have dealt with Ransomware. Product Strategy team members Rick Vanover and Karinne Bessette will show you a number of learnings over the years from our role here at Veeam
Sponsored by

Presentation
Continuous Security Validation: Exercise Your Environment more than the Adversary
With Incident Response as the new normal, ensuring that our systems and processes support that effort and threat hunting are working as expected. We will discuss why and how to establish a Continuous Security Validation (CSV) program within your organization. Specifically, how such a program evolves beyond Breach and Attack Simulation (BAS) and provides teams a continuous feedback loop to understand their posture and identify gaps as they arise
Sponsored by

Insider Risk Management: The alternative to traditional data protection is here!
Sponsored by
Presentation
The Malware Lab: Rethinking Enterprise File Analysis
Cyberthreats represent one of the most significant risks to modern businesses. Malware is pervasive; embedded in videos, hidden in software updates, and uploaded by unsuspecting customers. Yet the tools to investigate these threats are often manual and burdensome to maintain. Organizations recognize these challenges, but simply don’t know how to get started.
This session is a great opportunity to hear about a growing trend from one of ReversingLabs experts, Chip Epps. Chip will discuss centralizing the challenging tasks of investigating files and providing actionable intelligence to the entire organization. Some other areas of focus include:
- Streamlining file analysis and making security more responsive and proactive
- Why centralizing malware research into an enterprise “Malware Lab” is both efficient and effective
- How to benefit all lines of business and reduce cyber risks
Sponsored by

Presentation
5 Critical Pillars of the SOC of the Future
This year has seen nearly everything change to some degree—including within the Security Operations Center (SOC). Not only are we seeing a fast-evolving and surging threat landscape with which we must keep up, but we’re also contending with the business’s shifting priorities, budgets, and headcounts—all of which impact how the SOC can operate. To ensure we can continue to stave off threats in this new world, we must make sure the foundational elements of our SOC are in place:
- Threat intelligence
- Threat research
- Detection engineering
- Investigation
- Incident handling
This session will cover considerations for CISOs and infosec leaders within each of these five critical pillars. We’ll explore how organizations can make the most of limited resources and close skills gaps by carefully balancing their internal team’s competencies with outside expertise. Learn the steps you can take to establish a modern, efficient, and ultimately successful SOC of the future.
Sponsored by

Presentation
Building and Maintaining an Effective Cyber Range
Sponsored by
Live Closing Remarks
Closing Remarks
CISO Bourbon Happy Hour
Sponsored by