San Diego, CA
Wednesday, October 18, 2023
Hybrid





























Join FutureCon CyberSecurity Events in San Diego!
This event is the perfect opportunity to discover cutting-edge security approaches and learn how to manage risk in the ever-changing cybersecurity world.
Keynote Speaker
“"Unlocking Your Cybersecurity Potential: Maximizing Value for Your Organization"”
Dr. Vimal Subramanian
Vice President and CISO Cue Health
With my proven expertise in information security, I am passionate about helping organizations mature their information security programs to effectively manage information security risk. The balance between tight controls and operational effectiveness is seldom black and white. Balancing these principles while keeping an even keel can sometimes be more of an art-form than science.
With that in mind, I have demonstrated experience in effectively developing and implementing numerous highly effective security programs with support from all levels of management. I continue to use my expertise in Information Security and Risk Management arena to help organizations achieve their business goals while remaining secure for their customers, employees and shareholders.
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Dr. Vimal Subramanian
Vice President and CISO Cue Health
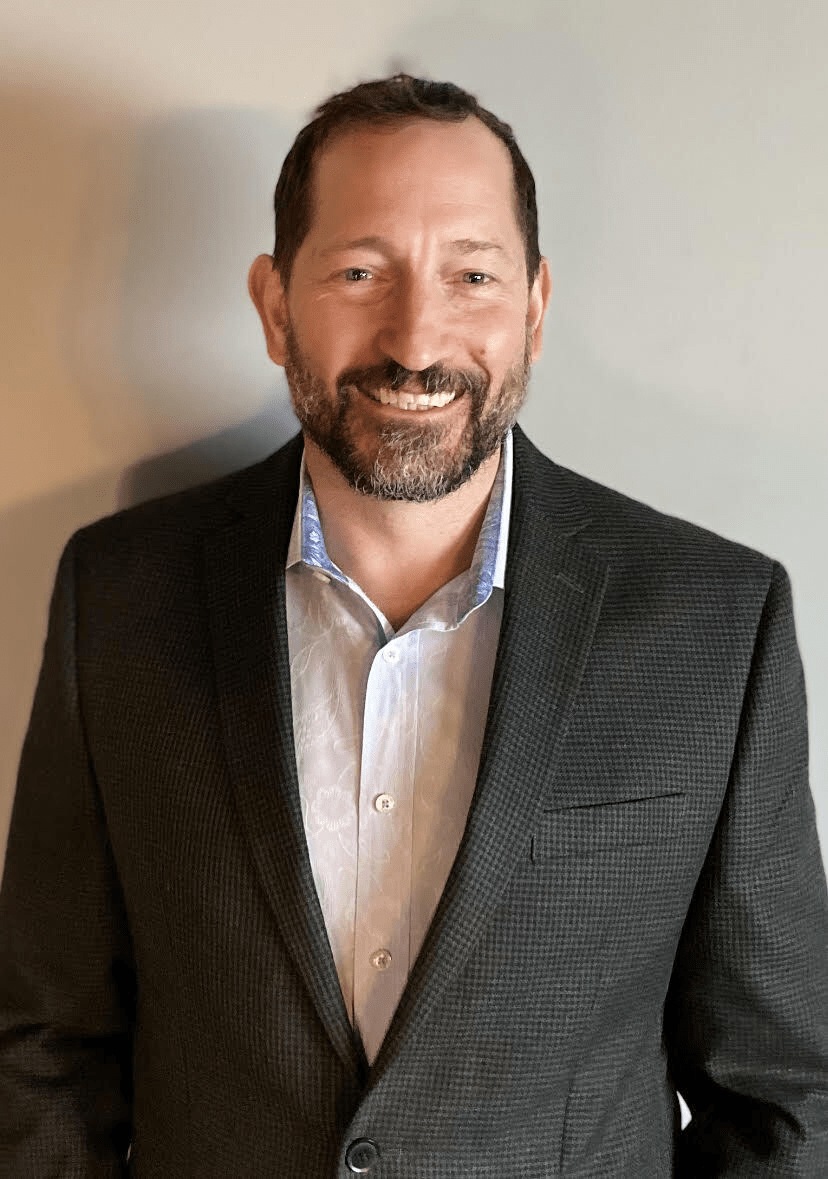
Eric Bartlett
Director of IT Operations and Compliance Officer MeBe
Irvin Velazquez, PhD S.
Compliance Officer Globant
Lisel Newton
Senior Director, Information Security, Risk and Compliance Gossamer Bio
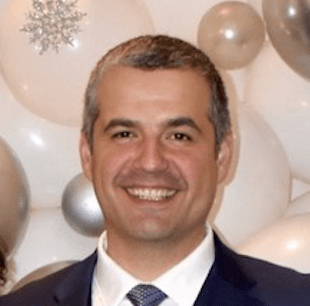
Darren Bennett
CyberSecurity Leader
Roberta French
Director of IT Operations and Security WD-40 Company
Sponsors
Gold Sponsors








Silver Sponsors


















Partner



About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Asset Management: A Strategic Approach to Risk Mitigation
This presentation emphasizes the essential role of asset management in comprehensive risk management. Covering breach prevention, insurance, reputational risk, and asset discovery and management, it highlights asset management as a primary strategy. Attendees will gain insights into proactive breach prevention measures, the relevance of insurance in risk scenarios, and the impact of asset management on brand reputation. By integrating asset management practices, organizations can optimize risk assessment, incident response, and resource allocation, fortifying their resilience in the face of evolving threats.
Sponsored by

Presentation
How (And Why) to Think Like a Threat Actor in The Cloud
Security leaders have had to choose between endpoint, container, and cloud security solutions for far too long. Your developers are a target, and if you can correlate information between their laptops and their cloud activity you can unlock a new level of security visibility and protection. In this presentation, we explain how to use one tool to secure everything, from laptop to cloud.
Sponsored by

Sponsor Networking Time
Presentation
Automation in Security Operations – Matching the speed of the attacker.
Sponsored by

Presentation
Don't Trust Your Inbox
Sponsored by

Sponsor Networking Time
Presentation
Dynamic Threat Intelligence to Determine Operational Risk
Sponsored by

Keynote
"Unlocking Your Cybersecurity Potential: Maximizing Value for Your Organization"
Sponsor Networking Time
Presentation
Identity-Focused Security for Your Zero Trust Journey
Sponsored by
Presentation
Modern Data Protection
Sponsored by

Sponsor Networking Time
Presentation
Open Source Developers Are Security’s New Front Line
Bad actors have recognized the power of open source and are now beginning to create their own attack opportunities. This new form of assault, where OSS project credentials are compromised and malicious code is intentionally injected into open source libraries, allows hackers to poison the well. In this session, Sonatype will explain how both security and developers must work together to stop this trend. Or, risk losing the entire open source ecosystem.
- Analyze, and detail, the events leading to today’s “all-out” attack on the OSS industry
- Define what the future of open source looks like in today’s new normal
- Outline how developers can step into the role of security, to protect themselves, and the millions of people depending on them
Sponsored by

Presentation
Zero-Trust: What it means and how to take a holistic approach to securing modern IT ecosystems
From web applications to email and software supply chains – every facet of an organization’s digital ecosystem requires robust protection. A zero-trust architecture can mean a lot of things and be daunting to implement, but it’s critical to prevent the pervasive risk of file-borne threats that could include malware, viruses, ransomware, and malicious scripts, often camouflaged within innocuous file formats.
The foundational steps to fortify defenses begin with asset and data identification, data flow mapping, access controls, network segmentation, and incident response planning. However, what’s next, and how do you continue to build a zero-trust security architecture? The answer lies in a layered defense strategy, incorporating true zero-trust technologies to not only drive compliance but mature your cybersecurity posture.
This layered approach should include multiscanning to significantly enhance threat detection rates, data sanitization to ensure file safety before use, country of origin detection to prevent potentially malicious code or files from infiltrating the organization, and Data Loss Prevention (DLP) to ensure the integrity of sensitive data by scrutinizing files prior to their transit. Finally, emerging technologies like adaptive threat analysis can provide actionable threat intelligence, enabling organizations to stay one step ahead of potential adversaries.
Experts at OPSWAT know first-hand what it takes to safeguard digital assets and ensure the resilience of organizations’ IT and OT infrastructure. Hear Joe Edwards, VP of Global Sales Engineering share his insights on implementing and maintaining robust zero-trust security in this evolving and complex threat landscape.
Sponsored by