San Diego, CA
Wednesday, November 16, 2022
Hybrid
Keynote Speaker
“"How the US Government is working to drive change through new programs so that they can better protect US interests and intellectual property for US companies"”
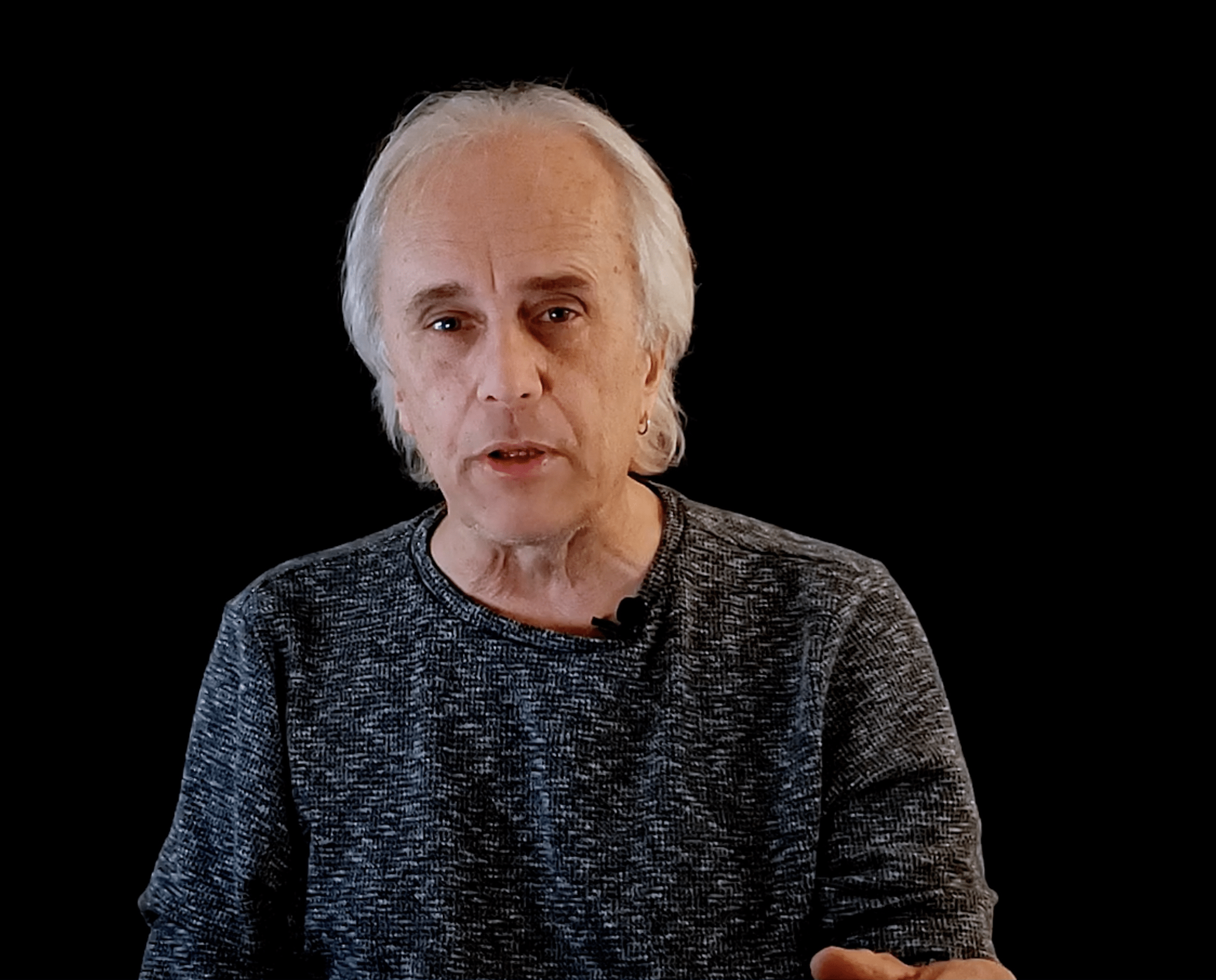
Darren Bennett
CyberSecurity Leader
Discussion on the struggle US Government Agencies struggle with sharing GFI (Government Furnished Indicators) & Intelligence with the Commercial Sector. How the US Government is working to drive change through new programs so that they can better protect US interests and intellectual property for US companies.
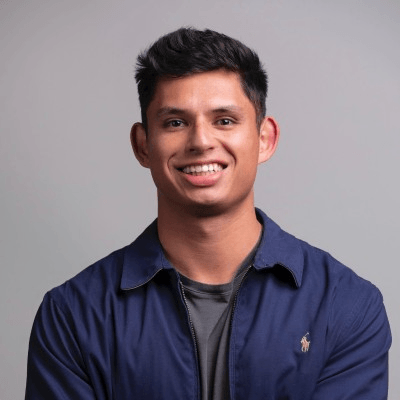
Macy Dennis
Chief Security Officer and Partner Ember River
Discussion on the struggle US Government Agencies struggle with sharing GFI (Government Furnished Indicators) & Intelligence with the Commercial Sector. How the US Government is working to drive change through new programs so that they can better protect US interests and intellectual property for US companies.
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Emily O'Carroll
Global Information Security Leader Topgolf Callaway Brands
Nick Ryan
Business Information Security Officer RSM US
Billy Norwood
Chief Information Security Officer FFF Enterprises
Kevin D. Smallen
Chief Information Security Officer PenChecks, Inc
J.J. Powell
vCISO Cyber Defense Group
Bill Higgs
Chief Information Security Officer | Cymer Regional Security Officer, US | ASML
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Business Logic Attack Definition (BLADE) framework
Sponsored by

"Cyber Intelligence" my Favorite Four Letter Word
In this 30 minute session, Justin Edgar (AVP, Security Strategy, Deepwatch) will discuss his personal experience with intelligence operations in both the physical and virtual spaces. During this discussion, Justin will describe multiple techniques for employing intelligence along with resources to enable attendees to do so more effectively. Targeted at security practitioners at all stages of their careers, attendees will leave with a different perspective on threat intelligence management and some interesting references to further their own efforts in the space.
Sponsored by

Top 10 Myths and Misconceptions about Ransomware
2021 was “the year of ransomware”. But so were 2017, 2018, 2019, and 2020 – and so far 2022 is not very different. Ransomware is no longer a problem discussed only in the cybersecurity and tech communities – it is now a regular topic in mainstream media headlines and executive board meetings.
So why is ransomware such a menace, and why can we not seem to get rid of it? One of the reasons is that we seem to miss the continued evolution of ransomware – we keep preparing for the last war. Ransomware in 2022 is very different than ransomware in 2017, yet we still treat it the same way.
Roy Correa, Enterprise Field Engineer will help you to learn more about:
- Ransomware evolution and what we need to un-learn to effectively combat it
- The most common myths, misunderstandings, and misconceptions about ransomware and the threat actors behind it
- The most effective tips to become more cyber resilient and prevent security incidents from turning into catastrophic breache
Sponsored by

Zero Trust and Microsegmentation – Easier Than You Think
Zero Trust has got to be one of the most talked about themes in cyber security. While the term means different things to different people, there are two things that can be agreed on: it’s a journey worth taking and microsegmentation is a key pillar of that journey. The next question always is how do you get started?Regardless of the sophistication of ransomware, the end goal is always the same: get in through a vulnerability and move laterally through your network. Join this presentation as we help peel back the layers to provide you simple steps to protect yourself from these threats that include:
- Gaining visibility to where you are the most vulnerable
- Closing risky ports
- Leveraging tools you already have in place without adding layers of complexity
While the journey can seem intimidating, we’ll help you realize that it doesn’t take a team of 100 or a PhD to deploy zero trust microsegmentation that will protect your organization and keep ransomware at bay.
Sponsored by

Keynote
"How the US Government is working to drive change through new programs so that they can better protect US interests and intellectual property for US companies"
Discussion on the struggle US Government Agencies struggle with sharing GFI (Government Furnished Indicators) & Intelligence with the Commercial Sector. How the US Government is working to drive change through new programs so that they can better protect US interests and intellectual property for US companies.
Presentation
Blocking and Tackling: The Fundamentals of AppSec
Application Security can be a very complex project to undertake. But is one of the most vital components in any company’s Cyber Security Framework. Of course, there will always be shifting trends and evolving technologies, but there are some very key fundamental skills and components present in every successful AppSec program. We will discuss those here in this session.
Sponsored by

Presentation
Continuous Security Validation and You: a tale as old as epoch time
With Incident Response as the new normal, ensuring that our systems and processes support that effort and threat hunting are working as expected. We will discuss why and how to establish a Continuous Security Validation (CSV) program within your organization. Specifically, how such a program evolves beyond Breach and Attack Simulation (BAS) and provides teams a continuous feedback loop to understand their posture and identify gaps as they arise
Sponsored by

Presentation
Security Blind Spots in the Era of Cloud Communication & Collaboration: Are You Protected?
In this session we’ll discuss:
- The (yet) unsolved challenges of email security – the main channel of targeted attacks
- Digitization and remote working have forged a new frontier, positioning the web browser at the front line of cyber attacks.
- The rising threat of cloud collaboration and the growing risk of content-borne attacks
- Cyber attack trends in the collaboration channel ecosystem
…And we will walk three use cases, their challenges and their deployments.
Sponsored by

Presentation
How AI Can Think Like an Attacker
In the face of skyrocketing cyber risk, detecting and responding to attacks is no longer enough. Organizations must take proactive steps to prevent threats before they happen, and to recover if compromised. In this session, Darktrace unveil an ambitious new approach to security, with core engines powering AI technologies to prevent, detect, respond, and ultimately heal from attacks. Together, these engines combine to strengthen organizations’ security posture in a virtuous AI feedback ‘loop,’ which provides powerful end-to-end, bespoke, and self-learning solutions unique to each organization.