Phoenix, AZ
Wednesday, September 21, 2022
Hybrid
Keynote Speaker
““As Technology Evolves, the More Security Stays the Same””
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Michael Manrod
Chief Information Security Officer Grand Canyon Education, Inc.
Lester Godsey
Chief Information Security Officer Arizona State University
Dr. Rebecca Wynn
Chief Cybersecurity Strategist & CISO Click Solutions Group
Bianca Lochner, Ph.D.
Chief Information Officer City of Scottsdale
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Seize the Breach: Why breaches still occur and how to mitigate them
Breaches happen and 2021 was a record-breaking year for them. According to Identity Theft Resource Center (ITRC) research, there were 1,291 breaches publicly reported in 2021 as of Sept. 2021 compared to 1,108 breaches in 2020; that’s a 17% year-over-year increase. Meanwhile, millions are spent on security operations centers that aren’t stopping the breaches from happening. Join us for a discussion on:
• Why SOC and security teams are way too limited by legacy SIEM
• How machine learning-driven analytics and automation technologies provide unmatched threat detection, investigation, and response (TDIR) capabilities so security teams can respond more quickly and accurately to seize the breach and mitigate damage.
• A simple maturity model based on outcomes and use cases that can vastly improve Security Operations
Sponsored by

Presentation
2022 Cyber Security Predictions and the Future of CSPM
Sponsored by

Presentation
Getting the most out of SOC Automation
Automation in the SOC? Panacea or pitfall? In this talk I will present some lessons learned from the journey deepwatch embarked on in automation, pitfalls and myths about automating operations, and our path moving forward. The audience will learn what tools and techniques worked as well as what failed miserably, and some tips for architecting a security stack that will plug in seamlessly to their current infrastructure.
Sponsored by

Presentation
Zero Trust and Microsegmentation – Easier Than You Think
Zero Trust has got to be one of the most talked about themes in cyber security. While the term means different things to different people, there are two things that can be agreed on: it’s a journey worth taking and microsegmentation is a key pillar of that journey. The next question always is how do you get started?Regardless of the sophistication of ransomware, the end goal is always the same: get in through a vulnerability and move laterally through your network. Join this presentation as we help peel back the layers to provide you simple steps to protect yourself from these threats that include:
- Gaining visibility to where you are the most vulnerable
- Closing risky ports
- Leveraging tools you already have in place without adding layers of complexity
While the journey can seem intimidating, we’ll help you realize that it doesn’t take a team of 100 or a PhD to deploy zero trust microsegmentation that will protect your organization and keep ransomware at bay.
Sponsored by

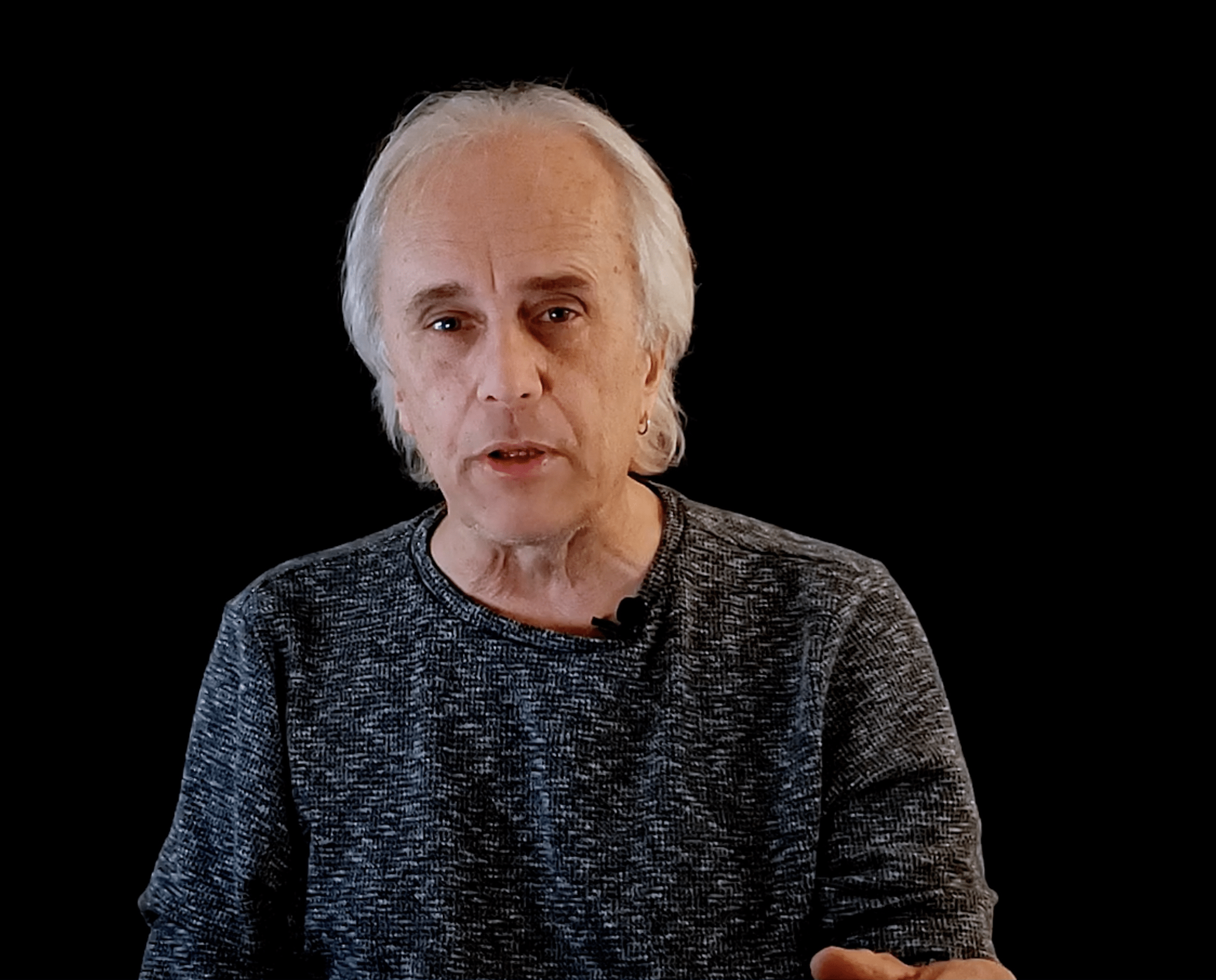
Keynote
“As Technology Evolves, the More Security Stays the Same”
With the accelerated adoption of cloud services, continued growth of IoT technologies and the continue desire to work from anywhere one would think that the security challenges would be wholly new. The truth is, while there are always exceptions, the challenges these new technologies provide are in many instances, variations on themes that have been plaguing us for years. How do we get our arms around these age-old problems and where does technology really play a role?
Presentation
PCI DSS 4.0 – The new flexibility and things you will want to know!
Can PCI implement a risk-based approach into compliance and a standard that has been around for years? Can it be done in a way that maintains solid security strategies, keeps up with the latest cyber risks and threats, and yet allows a business to function well? Come find out what PCI DSS 4.0 changes you need to be aware of and if all this is possible at the same time! Join Dan Fritsche, a former P2PE/PA/PCI QSA of over 10 years, to learn about the latest updates including key topics such as encryption, authentication, network monitoring, and application security.
Sponsored by

Presentation
Stopping Attacks, Not Your Business: AI & Autonomous Response
With cyber-attackers continuously searching for new ways to outpace security teams, it can lead to a struggle to fight back without disrupting business operations. Join Magill Bauerle, Cyber Security Account Executive, in this session where he explores the benefits of Autonomous Response as a must-have that goes beyond ‘defense’. Includes real-world threat finds and attack scenarios.
Sponsored by
Presentation
Simple is better. OneLogin is the leader in Unified Access Management
Sponsored by