Phoenix, AZ (Western Region)
Wednesday, June 9, 2021
Virtual
Keynote Speaker
“"Cognitive Malware - A Convergence Between Thought, Information Processing and Manipulation."”
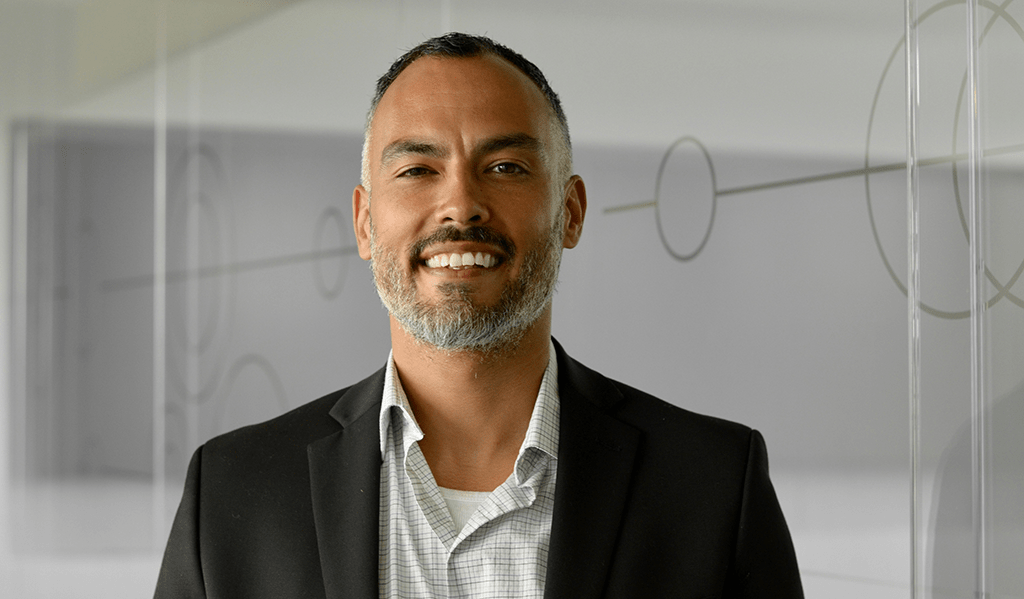
Michael Manrod
Chief Information Security Officer Grand Canyon Education, Inc.
CISO/Industry Leader Panel
“CISO Transforming the Risk Agenda, and What’s Ahead”
Debbie Christofferson
Senior IT Security Manager and Consultant ISSA
Alex Wood
Director of Enterprise Information Security The Anschutz Corporation
Kim Jones
Director of Security Operations Intuit
Lanita Collette
Deputy CIO, CISO University of Arizona
Richard Greenberg
Influencer | Advisor | CISO | CEO | Speaker | ISSA Distinguished Fellow and Honor Roll | Founder, Women in Security Forum
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions
Presentation
Insider Risk Management: The alternative to traditional data protection is here!
We live in a world where employees are almost twice as likely to expose corporate data than they were prior to the pandemic. As a result, organizations have been struggling to solve this problem with legacy solutions such as DLP and need a dedicated Insider Risk Program instead. By attending this session, you will learn how an Insider Risk Management approach can provide the visibility you need to quickly mitigate data exposure risks without the obstacles commonly associated with blocking and tackling.
Sponsored by
Presentation
How to use your vulnerabilities to train your developers on security
The idea of secure coding training that covers just what you need, right when you need it, seems too good to be true. But it’s not. This webinar will reveal the most common vulnerabilities developers cause, and guide you on how to set up a secure coding training program that uses your vulnerabilities to improve your application security.
Sponsored by

Keynote
"Cognitive Malware - A Convergence Between Thought, Information Processing and Manipulation."
For some time, humans were studied to conceptualize how to induce the inception of thinking machines. Now that there are thinking machines, some insights from information systems may actually inform aspects of how we think as humans. As the flow of information eventually reverses itself, what can we learn about ourselves when we gaze into the machines we have created in our image?
Presentation
5 Critical Pillars of the SOC of the Future
This year has seen nearly everything change to some degree—including within the Security Operations Center (SOC). Not only are we seeing a fast-evolving and surging threat landscape with which we must keep up, but we’re also contending with the business’s shifting priorities, budgets, and headcounts—all of which impact how the SOC can operate. To ensure we can continue to stave off threats in this new world, we must make sure the foundational elements of our SOC are in place:
- Threat intelligence
- Threat research
- Detection engineering
- Investigation
- Incident handling
This session will cover considerations for CISOs and infosec leaders within each of these five critical pillars. We’ll explore how organizations can make the most of limited resources and close skills gaps by carefully balancing their internal team’s competencies with outside expertise. Learn the steps you can take to establish a modern, efficient, and ultimately successful SOC of the future.
Sponsored by

Live Panel Discussion
“CISO Transforming the Risk Agenda, and What’s Ahead”
The digital frontier, cybercrime, and global business dependency on having a protected infrastructure, means CISOs need to get it right. Defining what that means, in a complex, evolving technology environment with endless challenges takes the measure of a security leader and their team. These executive leaders will share their success strategies to support the business in a high stress field: How the role evolves in security threats, support to address them, plus career evolution, succession and planning.
- Addressing current risks
- Separating the wheat and the chaff on security tools and solutions
- Finding the best security partners
- Sourcing and managing the talent
- Career paths beyond the CISO
- What’s ahead
Richard Greenberg
Influencer | Advisor | CISO | CEO | Speaker | ISSA Distinguished Fellow and Honor Roll | Founder, Women in Security Forum
Presentation
Extortionware: Your Privacy Problems Made Public
Sponsored by

Presentation
5 Lessons Learned Fighting Ransomware
There are many threats to your data. These threats can be intentional, accidental or downright malicious. In this session, see from the eyes of a leading backup provider (Veeam) what you can learn from organizations who have dealt with Ransomware. Product Strategy team members Rick Vanover and Karinne Bessette will show you a number of learnings over the years from our role here at Veeam
Sponsored by

Presentation
Ransomware
As the threat landscape continues to grow Ransomware has evolved to become a formidable weapon. Despite its evolution Ransomware attack methods remain largely unchanged. Today we’ll look at how ransomware has grown in recent history and discuss a few ways to help you mitigate risk.
Sponsored by

Presentation
2021 State of Malware
- Top threats for businesses and consumers
- Emerging cybercrime trends and tactics
- Solutions you can employ to thwart future attacks
Sponsored by

Presentation
Faking It: Stopping Impersonation Attacks with Cyber AI
Today, 94% of cyber-threats still originate in the inbox. ‘Impersonation attacks’ are on the rise, as artificial intelligence is increasingly being used to automatically generate spear-phishing emails, or ‘digital fakes’, that expertly mimic the writing style of trusted contacts and colleagues.
Humans can no longer distinguish real from fake on their own – businesses are increasingly turning to AI to distinguish friend from foe and fight back with autonomous response.
In an era when thousands of documents can be encrypted in minutes, ‘immune system’ technology takes action in seconds – stopping cyber-threats before damage is done.
Find out how in this session.
Sponsored by
Presentation
Identity Cloud Checklist
Sponsored by

Presentation
Stay Ahead of the Hacker with Continuous Security Testing
Join Sion Retzkin, CISO & Head of Knowledge & Practice, Pcysys to learn how to:
-
Build up your cyber resilience with continuous risk validation
-
Prioritize remediation efforts with a threat-facing perspective
-
Increase the productivity of your security teams
Sponsored by