Philadelphia Cybersecurity Conference
Thursday, March 19, 2026
Hybrid
480 North Gulph Road, King of Prussia, Pennsylvania, USA, 19406






































Join Us in Philadelphia for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
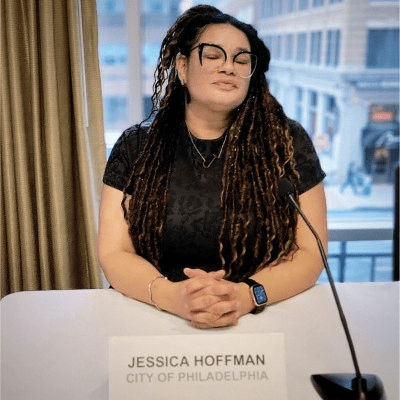
Jessica Hoffman
Deputy Chief Information Security Officer & HIPAA Security Officer City of Philadelphia
Hazel Cerra
National Security & Risk Governance Executive U.S. Secret Service
Dr. Jamaine Mungo
Chief Information Security Officer Philadelphia International Airport
Melina Scotto
Executive VP and Founder | Mastin and Associates Former CISO and VP CyberSecurity | Fortune 500 Hospitality Org
Mike Elkins
Chief Information Security Officer Humanis Technologies
Sponsors
Premier Platinum Sponsors


Gold Sponsors








Silver Sponsors


























Bronze Sponsors

Partner





“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Rolling for Resilience: Turning Tabletop Exercises into Strategic Readiness Campaigns
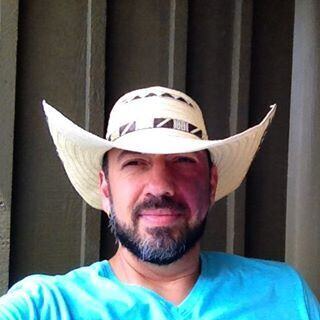
In many organizations, tabletop exercises are treated as annual compliance events… predictable scenarios, scripted discussions, and binders opened only when auditors are watching. Rolling for Resilience challenges this approach, arguing that true incident readiness is not built through checklist theater but through intentional design, engagement, and cross-functional alignment. Drawing from experience in security leadership, penetration testing, and incident response strategy, Giovanni Cofré explores how immersive, well-structured tabletop exercises can reveal communication gaps, decision bottlenecks, and leadership misalignment long before a real breach occurs. Using a narrative framework inspired by campaign-based strategy and gamification, this session examines how engagement fosters psychological safety, how communication pathways shape incident outcomes, and how departmental playbooks must translate into actionable field guides when pressure rises. Rather than focusing solely on preventing every possible attack, this talk emphasizes building disciplined response capability. Ensuring that when the horn sounds, teams know who moves first, who decides, and how action unfolds in real time. Attendees will gain practical insight into transforming tabletop exercises into measurable readiness programs that strengthen coordination, clarify executive roles, and build resilience before the first breach occurs.
Sponsored by

Presentation
AI Cybersecurity’s Double Edge Sword
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Deception Tactics: Extending the Cat-and-Mouse Game
Every day, websites face a myriad of attacks. Traditionally, the instinct is to identify and block these threats with standard HTTP error codes. However, this often leads attackers to become more sophisticated in their evasion tactics. Studies show defenders spend 98% of their time identifying attackers and only 2% on response strategies. This talk will delve into the importance of alternative blocking strategies, with a focus on deception, and how it can be effectively used to slow down and frustrate attackers.
Sponsored by

Presentation
Browser Threat Prevention in the World of AI
Artificial Intelligence has revolutionized how we work, but it has also armed cybercriminals with unprecedented capabilities. From automated reconnaissance to “Clickfix” social engineering tactics that bypass reputation-based security tools—including AV, EDR/EPP, firewalls, and SWGs/CASBs—attackers are moving faster and smarter. Are your defenses ready for 2026?
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Presentation
AI Wrote It. Let’s Hack It.
AI coding assistants can generate functional applications in minutes. What they don’t generate is security.
In this live session, Contrast Security’s Head of Product Security Naomi Buckwalter will show you an application built by an AI coding tool. Then, she’ll switch roles from developer to attacker and begin breaking it, with AI-generated attacks. You’ll see real vulnerabilities emerge, watch them get exploited, and understand how quickly AI-generated code can turn into a live risk.
Then she’ll show what actually stops it. Using runtime protection, she’ll detect and block the attacks without rewriting the application – demonstrating how teams can apply a virtual patch for attacks even when insecure code is already in production.
Fast code is here. See how to protect it.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
The Risks Behind Multi-Channel Attacks
Sponsored by

Presentation
The Perfect Storm: Navigating the Latest Threat in 2026 & Beyond
Cybercrime has evolved into a highly organized, state-tolerated global enterprise capable of generating massive illicit profits. These modern threat actors have supercharged their multi-layered extortion campaigns by weaponizing artificial intelligence to execute flawless phishing, voice cloning, and deepfake attacks that easily bypass traditional human defenses. With the average business cost of an attack reaching $1.53 million, organizations face adversaries operating with speed, precision, and enterprise‑level efficiency. This session explores how AI is reshaping the modern threat landscape and why organizations must respond by deploying AI‑native cybersecurity platforms, enforcing zero‑trust network access, and maintaining aggressive vulnerability and patch management to reduce risk and improve resilience.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Guarding Tomorrow: AI’s Edge in Security Ops
This presentation dives into how AI’s transforming security operations today and shaping cybersecurity’s future. We’ll explore real-world roles like threat detection, automated responses, and predictive analytics, plus insights on booming AI stocks driving these innovations—like key players in the sector and their impact on the market.
Sponsored by

Presentation
The End of Legacy Network Security
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!