Orange County, CA
Wednesday, July 12, 2023
Hybrid





























Join FutureCon CyberSecurity Events in Orange County!
This event is the perfect opportunity to discover cutting-edge security approaches and learn how to manage risk in the ever-changing cybersecurity world.
Keynote Speaker
“"Cyberpsychology and Its Impact on Cyber Crime"”
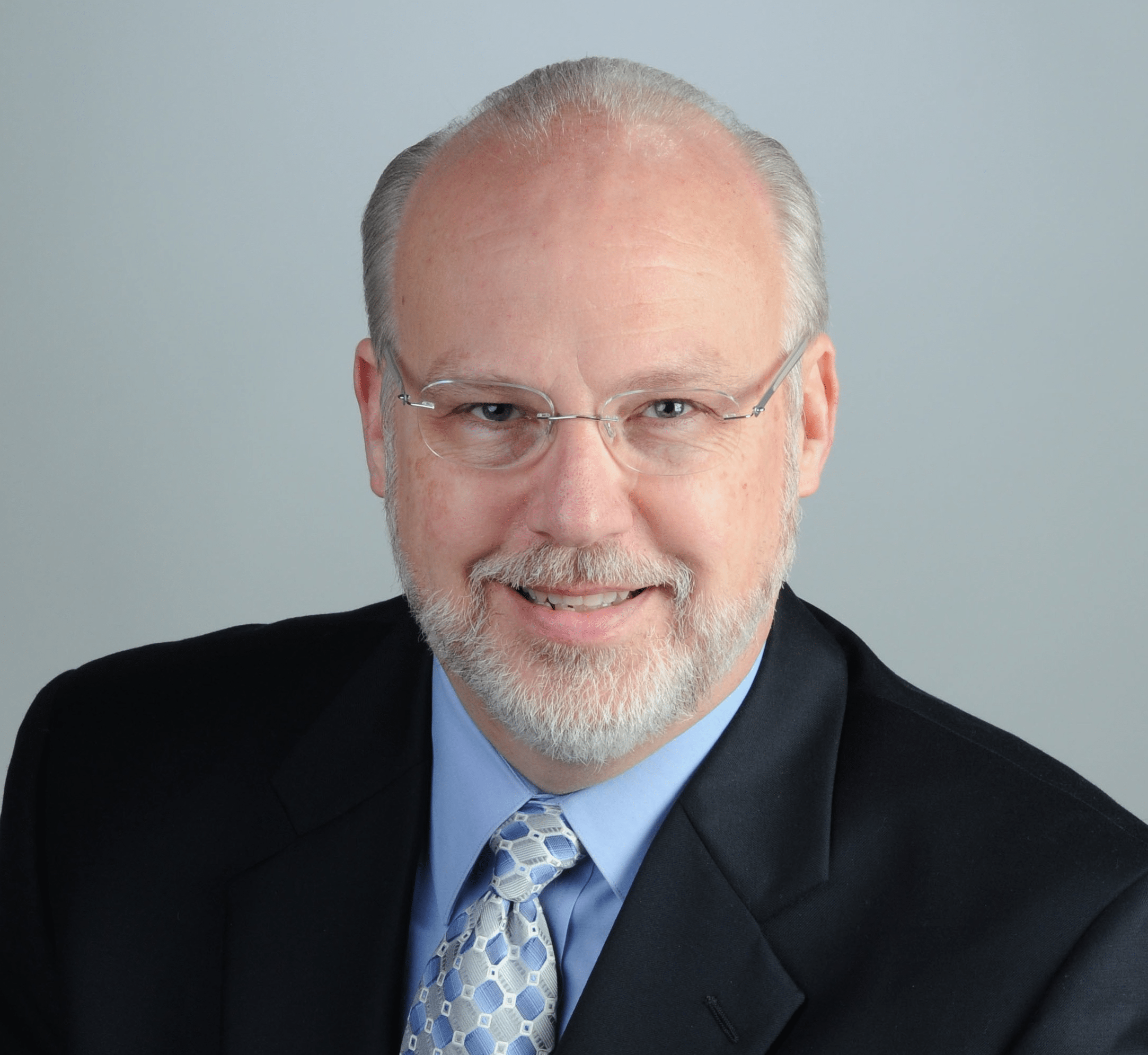
Allen Ohanian
Information Security Officer Los Angeles County Department of Children and Family Services
Mr. Ohanian is a highly accomplished and experienced Information Security Officer with 25 years of experience in information technology, cybersecurity, and defense strategies in both the private and public sectors. He currently serves as the Information Security Officer for the Los Angeles County Department of Children and Family Services (DCFS), the largest child welfare institution in the nation. At DCFS, Mr. Ohanian has successfully architected and implemented cybersecurity and privacy programs from the ground up, interwoven cybersecurity into the business culture, and created a security-conscious enterprise. He has also achieved the organization’s mission of service excellence through outstanding leadership, governance, strategic planning, business acumen, and cost-saving transformation initiatives.
Mr. Ohanian is an innovative and visionary leader who has chaired the Countywide Risk Management Cybersecurity Team responsible for developing and implementing administrative, technical, and tactical strategies to assess and reduce cybersecurity risks to County information assets. He is also an innovation advisory council member of various Cybersecurity taskforces and workgroups.
As an accomplished keynote speaker and panel member, Mr. Ohanian has participated in numerous international and national private and public sector conferences, including Interop, CISO 360 USA, Arab International Cybersecurity Summit, Los Angeles Government Summit, and National Cybersecurity Awareness seminars. In addition, he serves as a Ph.D. Dissertation Committee Member for Cybersecurity using Artificial Intelligence at Center for Information Systems & Technology Claremont Graduate University. Mr. Ohanian’s accomplishments in improving organizations’ cybersecurity posture have led to various excellence awards, including multiple Information Security Officer of the Year awards.
He holds a bachelor’s degree in computer science from Cal Poly Pomona (magna cum laude) and obtained his dual Master’s Degree in Cybersecurity and Business Administration at the University of Maryland (UMUC). He is pursuing a Ph.D. in the Industrial/Organizational Psychology program, demonstrating his passion for continuous learning and growth.
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
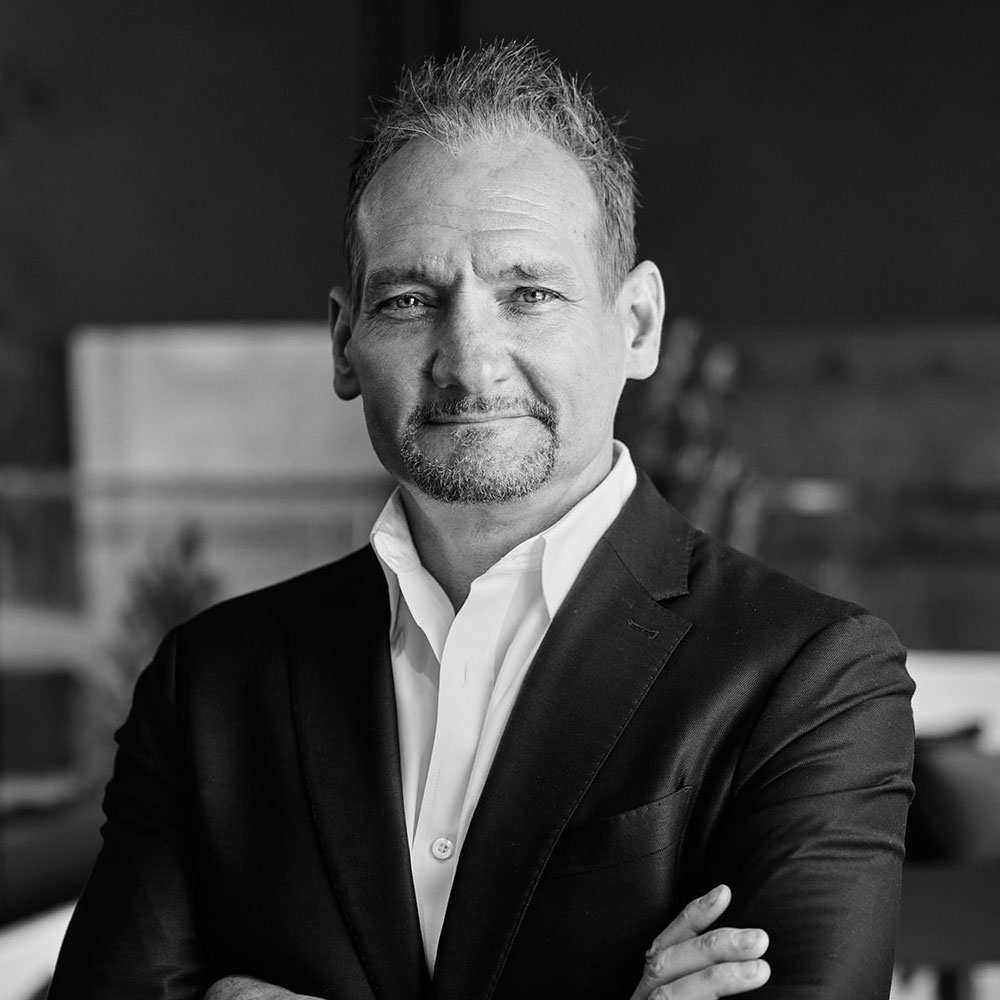
Haral Tsitsivas
Principal Product Security Engineer, Arlo Technologies Chapter President, OWASP Orange County
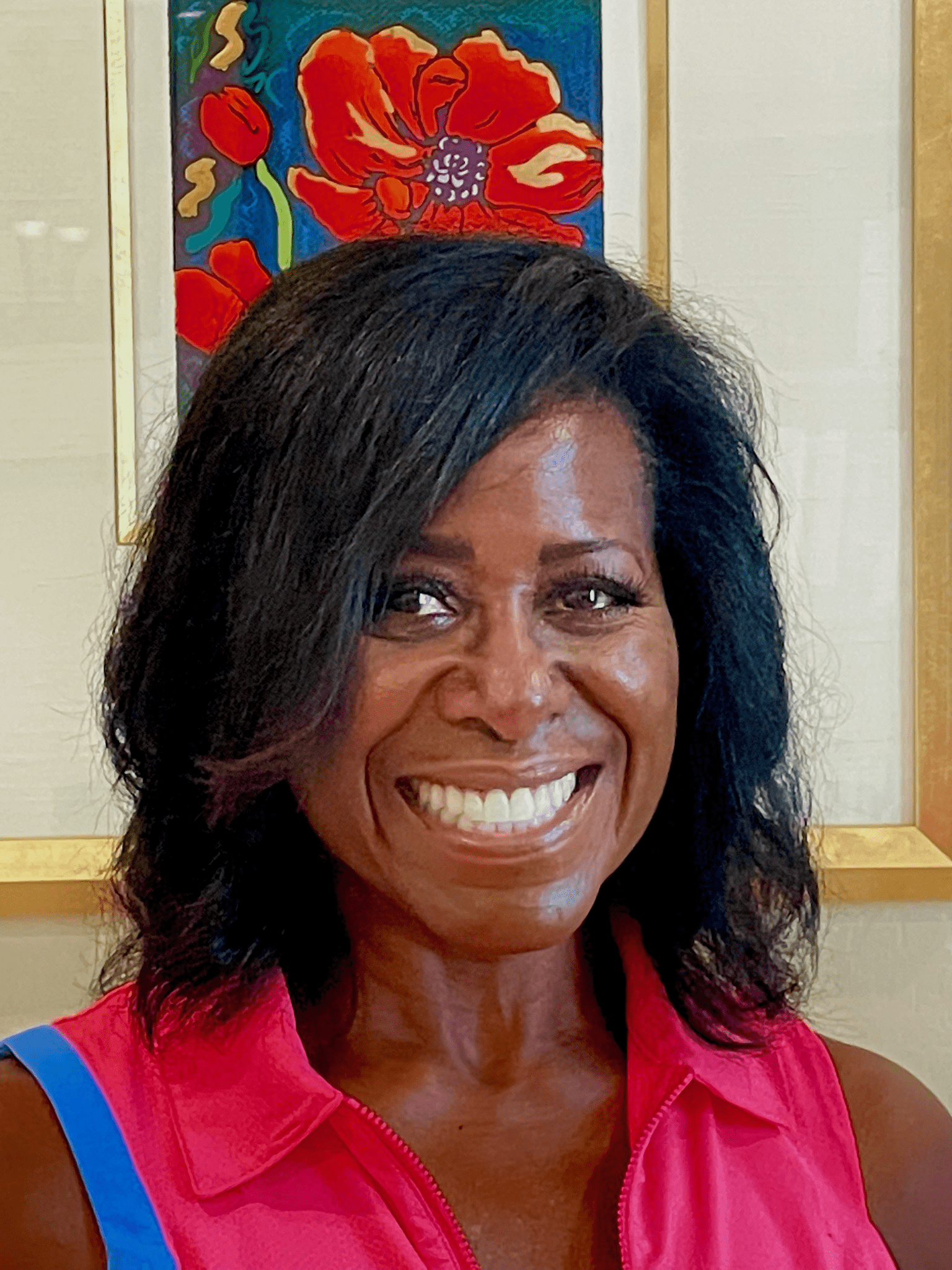
Antonella Commiato
Chief Technology Officer / Chief Information Security Officer Extend Resources
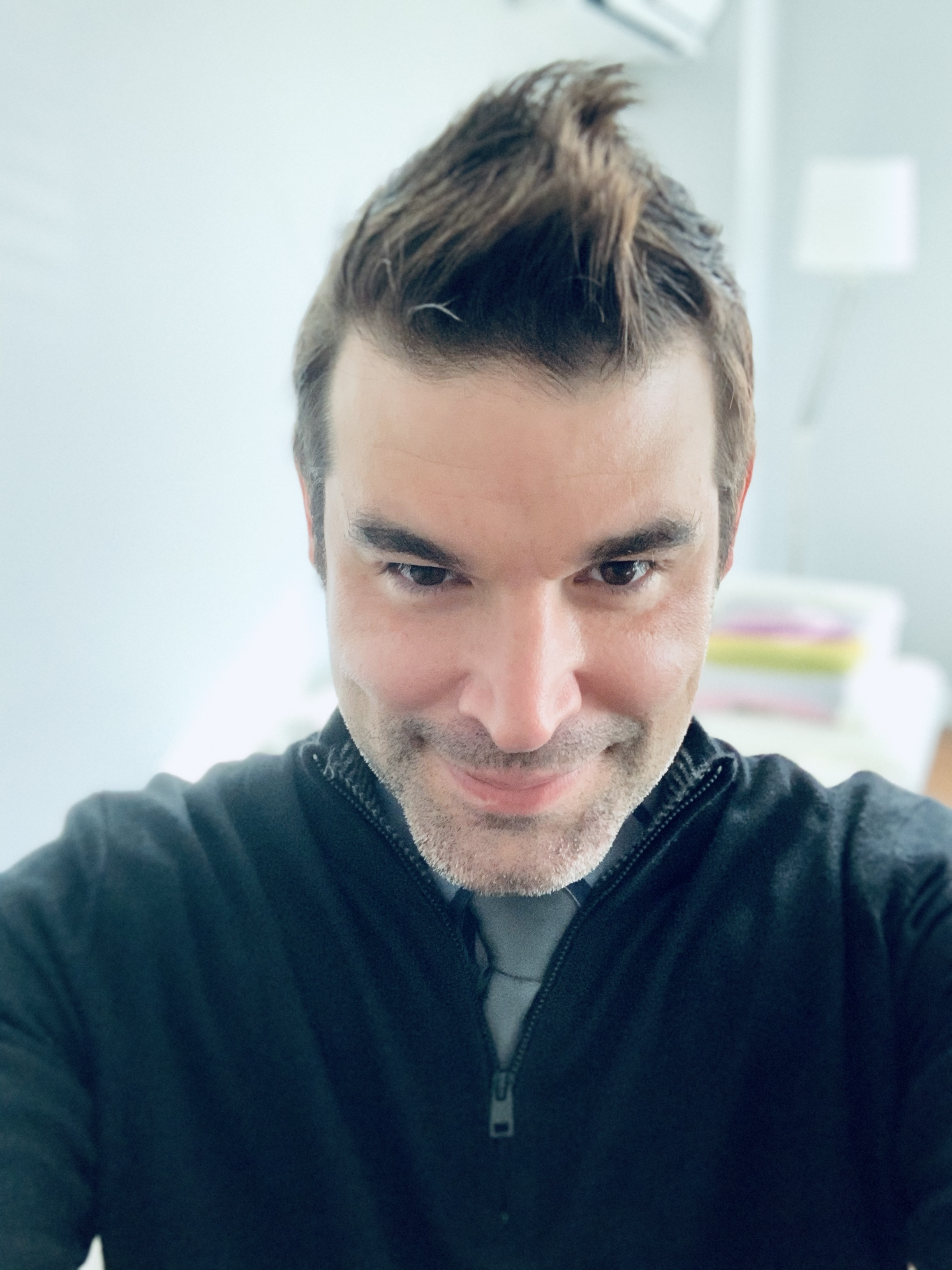
Nikolay Chernavsky
Chief Information Security Officer ISSQUARED, Inc.
Allen Ohanian
Information Security Officer Los Angeles County Department of Children and Family Services
Dale “Dr. Z” Zabriskie CISSP CCSK
Field Chief Information Security Officer Cohesity
Sponsors
Premier Platinum Sponsors

Gold Sponsors






Silver Sponsors



















Partner



About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Chicago Marriott Oak Brook
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Treat Your Data Like It’s Currency
You’ve heard that “data is the new oil”. More accurately, “data is your currency”. It gives you the ability to conduct business. Mismanage it and there can be serious consequences. Lose it and you lose your business.
With your “bills” spread across your environment, managing and protecting the “money” can be a monumental task. $100s, $50s, $20s, $10s, $5s, and lots of $1s are strewn about. Knowing where your most valuable bills are is foundational to any data security process. This session will explore the key steps in identifying the most important data in your organization. Using real-world examples, we will examine the impact of placing appropriate controls to protect your most important business asset: your data.
Sponsored by

Presentation
Cameras, CACs & Clocks: A Story of Millions of Interrogated and Hacked xIoT Devices
We’ve unleashed our dark allies from the nightmare dimension on an unholy crusade to demonstrate cyberattacks for your enlightenment. If you love seeing devices compromised as much as we do, join us for a real hacking demonstration, detailed security research findings, and threat mitigation techniques that will disappoint bad actors. Share your new knowledge around the water cooler, apply these preventative security strategies within your own organization, and become the cool person at the office party everyone wants to hang out with regardless of that cat sweater you insist on wearing.
We’ll share stories from the trenches involving cybercriminals, nation-state actors, and defenders. Our presentation will detail findings from over six years of xIoT threat research spanning millions of production devices in enterprises and government agencies around the world. We’ll identify various steps organizations can take to mitigate risk while embracing a Things-connected world. We’ll also demonstrate a hack against an xIoT, or Extended Internet of Things, device. For those who would say, “But they’re just security cameras monitoring the parking garage, wireless access points in the cafeteria, or PLCs controlling robotic welding arms; what harm can they cause?” – this will illuminate that harm.
xIoT encompasses four disparate but interrelated device groups that operate with purpose-built hardware and firmware, are typically network-connected, and disallow the installation of traditional endpoint security controls. The first group contains enterprise IoT devices such as VoIP phones, security cameras, wireless access points, network attached storage, and printers. The second group includes OT devices such as PLCs, building automation systems, and industrial control systems. The third group consists of IoMT assets such as infusion pumps, patient monitors, and wireless vital monitors. The fourth group contains IIoT devices like robotics, smart factory systems, and temperature sensors.
There are over 50 billion xIoT devices in operation worldwide. Most of these devices run well-known operating systems like Linux, Android, BSD, and various real-time operating systems like VxWorks. Additionally, many xIoT devices have open ports, protocols, storage, memory, and processing capabilities similar to your laptop. But there is a major difference. Even though most enterprises and government agencies have tens to hundreds of thousands of these devices in production, they go largely unmanaged and unmonitored. These xIoT devices typically operate with weak credentials, old, vulnerable firmware, extraneous services, and problematic certificates. This massive, vulnerable xIoT attack surface is being successfully exploited by bad actors engaging in cyber espionage, data exfiltration, sabotage, and extortion, impacting xIoT, IT, and cloud assets.
Nation-states and cybercriminals have shifted their focus to xIoT attacks. Why? Because they work. Military-grade xIoT hacking tools are in use, cybercrime for hire that’s predicated on compromised xIoT devices has been monetized, and organizations worldwide are already “pwned” without even knowing it. Bad actors are counting on you being passive by not mitigating xIoT security risks. They want you to fail so they can continue to evade detection and maintain persistence on your xIoT devices. Disappoint them! Take your xIoT devices back by understanding how to hack them, recognizing where they’re most vulnerable, and employing strategies to successfully protect them at scale.
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Solving Security's (Big) Data Problem
Security teams are struggling to manage high volume, high velocity data and threats are lost in an endless list of alerts. We’ll demonstrate how effective use of data pipelines reduces volume, amplifies signal to noise ratio, saves countless hours and dollars, and may even save the planet.
Key Takeaways:
- Most organizations ingest data inefficiently, resulting in duplicate, redundant, or useless information and false positives.
- The cost of inefficient data is far greater than monetary. it impacts security, engineering, and even the environment.
- Using data pipelines and effective data processing saves time, money, and frustration. Better data means stronger signal to noise and more effective threat detection.
Sponsored by
Presentation
Risk to Resilience: Ensuring optimum cyberhygiene with Endpoint Security
In today‘s threat landscape, digital transformation is crucial for organizations looking to stay ahead of threat actors. To achieve this, IT and Security teams must work together to ward off cyberattacks and ensure a positive employee experience. In this session, we’ll highlight the endpoint security strategies for your IT stack against known and unknown vulnerabilities.
Sponsored by
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Presentation
Security Operations: Going from InfoSec-Checklist to InfoSec-Culture
A brief overview of cyber trends and first steps towards NIST compliance
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Keynote
"Cyberpsychology and Its Impact on Cyber Crime"
Allen Ohanian
Information Security Officer Los Angeles County Department of Children and Family Services
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
How to Build an Insider Threat Program:
Sometimes just having a SOC isn’t enough to address insider threat issues. Security operations teams are managing massive amounts of data across billions of events from on premises to the cloud. Looking for specific needles like insider threats in this complex haystack has special requirements that encompass both searching historic data and seeing evolving credential behavior changes as they happen.
Whether from downsizing or expanding the business, employees, vendors, contractors, and more are moving in and out of your environment. And often, it is during turbulent times that insider threats go unobserved as everything changes so quickly. Insider threat initiatives require a new, more focused approach.
This presentation will explore:
- The common scenarios that indicate you need an insider threat team, how to build a mission statement, and tools
- Four attributes of a successful insider threat program
- How behavioral analytics baseline “normal” behavior of users and devices – showing risk faster
Sponsored by

Presentation
Great eXpeltations: cyber defense trends for 2023
A look at cybersecurity trends from 2022, how Expel caught these attacks in the wild, and how these trends can inform your security strategy in 2023.
We know that 2022 was fraught with security threats. But wrapping your head around what they were, what’s trending, and what to do about it is essential for your security strategy going into 2023.
Expel’s annual threat report, Great eXpeltations, compiles data, trends, and recommendations from the incidents our security operations center (SOC) saw in 2022, based on our full customer base: from small and midsize companies to enterprise orgs, at every phase of the security journey, across every industry Expel serves.
Join Chris Hencinski, Solutions Architect, Expel, for a deep dive into the numbers and their real-world incident counterparts, including examples of pre-ransomware, business application compromise, credential harvester phishing, SaaS compromise, and an attack against cloud infrastructure.
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
How Can WE Become Unhackable
Every business desires to be unhackable. Even air-gapped environments have data leakage, but there are proven steps that can significantly limit your exposure without causing undue irritation to your staff. In this session, we will review current security methods, discuss current flaws, and understand why a Zero Trust solution is the best solution.
Rob McBride
Head of Americas Channels, Solution Architects and Pre-Sales Engineering Versa Networks
Sponsored by

Presentation
Don’t Trust Your Inbox
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!