Nashville Cybersecurity Conference
Thursday, November 14, 2024
Franklin Marriott Cool Springs
Hybrid





























Join Us in Nashville for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
Keynote Speaker
“Breaking Bad—Mitigating Insider Threats”
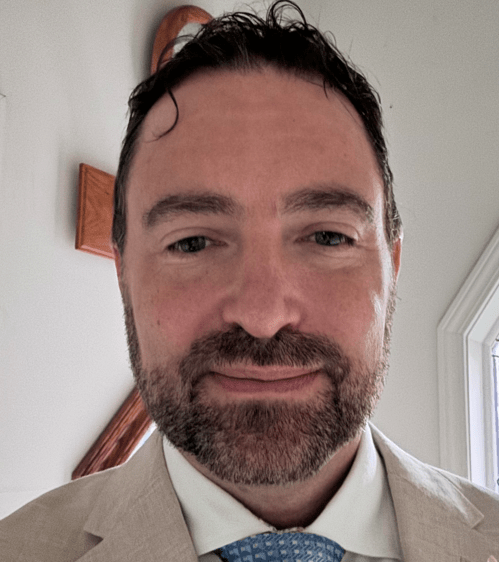
Lee M. Eaves
Special Agent--Office of Homeland Security State of Tennessee
Cybersecurity and digital forensics expert Lee M. Eaves is currently a Special Agent with the Tennessee Department of Safety and Homeland Security. With over two decades of experience, Lee has a proven track record in safeguarding the nation’s critical infrastructure and investigating cybercrime. He has served in key roles at the Williamson County Sheriff’s Office (TN), the U.S. Department of Homeland Security, Nissan North America, and the U.S. Secret Service. Lee is a respected instructor and holds multiple certifications in his field.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Marc Johnson
CISO / Director / vCISO / vCIO Impact Advisors
Roger Brotz
CISO Acadia Healthcare
Barbee Mooneyhan
VP | Security, IT, and Privacy, Woebot Health WiCyS TN Affiliate and BISO Affiliate Leader
Melissa Page
Director of Information Technology and Security Cumberland University
Sponsors
Platinum Sponsors


Gold Sponsors




Silver Sponsors






















Partner




“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Franklin Marriott Cool Springs
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Mastering Adversary Tactics: Unveiling the Power of MITRE ATT&CK Framework
Mike Sci is going to introduce you to the MITRE ATT&CK framework as a comprehensive tool for understanding adversary behavior to create defenses against these tactics and techniques.
- Definition and purpose of the MITRE ATT&CK framework.
- Explanation of how MITRE ATT&CK catalogs tactics, techniques, and procedures used by adversaries during cyber-attacks.
- Overview of the MITRE ATT&CK matrix structure
- How Adlumin uses MITRE and other frameworks to create a product and service to defend against adversaries to prevent business disruption
Sponsored by

Presentation
Securing Your Revenue Stream: Protecting Applications and APIs from Bot Threats
With automation changing the landscape, global cyber losses attributable to bot attacks now average between $68-$116B annually. We will examine data from the Imperva Threat Research team to investigate the scope of the challenge, review real-world examples and provide practical steps you can take to prepare for the inevitable security incident.
Sponsored by
Presentation
Ransomware: A Security Reference Architecture
We will dive into the increasing threat posed by ransomware and why it’s critical to address this challenge head-on. Myriad360 will explain the value of a Reference Architecture in building a strong defense against these attacks. They will also explore how ransomware tactics are continuously evolving, requiring organizations to stay agile in their security approach. Lastly, they touch on other key factors that should be considered when planning a comprehensive cybersecurity strategy to protect against ransomware and other threats.
Sponsored by

Sponsor Networking Time
Presentation
Extortion and Exfiltration: The New Age of Ransomware
- Ransomware trends and insights
- The rise of exfiltration and extortion
- The importance of integrating new technologies into cybersecurity stacks including anti data exfiltration technology
- How to build comprehensive cybersecurity defenses
Sponsored by

Presentation
Fortifying the Digital Footprint: Strategic Personal Cybersecurity for High-Visibility Executives
High-value executives face risks in their personal digital lives that cascade risk to their corporate infrastructure. In this session, we unpack the sophisticated methodologies employed by adversaries aiming to exploit personal vulnerabilities to orchestrate corporate breaches.
Sponsored by
Sponsor Networking Time
Lunch
Keynote
Breaking Bad—Mitigating Insider Threats
Sponsor Networking Time
Presentation
Can an AI-Infused MXDR lead to an Autonomous SOC?
Organizations must detect and respond to cyber-attacks before the attacker’s objective is completed. Managed XDR is central to the job. AI is poised to be the force multiplier we’ve been awaiting. But is it a near-term reality? This presentation will cover:
- Typical attack sequence and observable signals
- Why is it so hard to catch the bad guys?
- What is the detection and response process?
- Historical AI in cyber, changes with LLMs
- The next wave of AI: Agents
- Whether to be bullish or bearish on SOC AI near-term potential
Sponsored by
Presentation
The Radical Future of App and API Security Testing
Application security testing (AST) in pre-prod can be highly effective but robust regimens for doing so are shockingly rare. What you see instead are a few underutilized tools introduced mostly to check a compliance box without significantly reducing actual risk. On the other hand, current tools and techniques for doing AST in production are very limited.This talk explores technology and techniques to do it effectively in production which in turn fundamentally changes the economics of being able to do it well in pre-prod.The parallel is that over the last decade or so, application performance and load testing moved from pre-prod to production with the introduction of efficient APM agents and practices like canary deploys. The motivations are the same. Production is the REAL context, not mocked or assumed. User behavior is also REAL, not simulated with automated or manual tests.What are the equivalent technology and techniques so we can create an application vulnerability monitoring (AVM) movement? How close are we to perfecting them? What can you do to accelerate their adoption?
Sponsored by

Sponsor Networking Time
Presentation
Ransomware Prevention and Remediation
Understanding what an attack looks like and how the recovery process works for multiple ‘disaster’ situation
Sponsored by

Presentation
Accelerate AI innovation Securely
As organizations increasingly migrate to the cloud, the landscape of cybersecurity is evolving at a rapid pace. The advent of Artificial Intelligence (AI) brings both unprecedented opportunities and challenges, making it imperative for cloud security strategies to advance accordingly. Join this session to hear from Wiz why organizations are adopting AI-SPM (AI- Security Posture Management) into their CNAPP strategy and how you can effectively secure AI workloads in the cloud while accelerating AI innovation securely.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!