Nashville, TN (Eastern Region)
Wednesday, September 15, 2021
Virtual
Keynote Speaker
“Zero Trust or Bust: Build IT and they Won’t Come!”
Ron Zochalski
Chief Technology Officer & Chief Information Security Officer Lake County Government - Superior Court Juvenile Division
CISO/Industry Leader Panel
"Zero Trust is Not Enough"
Laureen Smith
Executive - Cybersecurity Advisory LJ Marketing & Communications
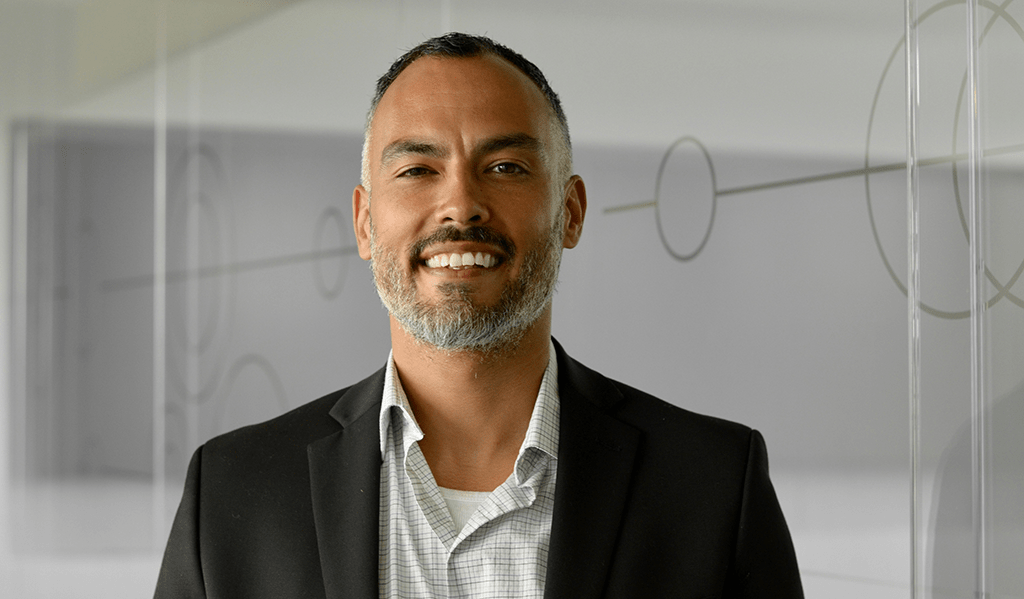
Endre Jarraux Walls
Chief Information Security Officer Customers Bank
Ron Zochalski
Chief Technology Officer & Chief Information Security Officer Lake County Government - Superior Court Juvenile Division
Thad Phillips, PhD
Chief Information Security Officer Baptist Health Care
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Live
Opening Introductions
Live Presentation
Rise of Secure Access Service Edge (SASE)
Secure access service edge has quickly emerged as a hot topic in cybersecurity, but what exactly does it mean and why should organizations care? As cloud migration, BYOD adoption, and remote work have skyrocketed in prevalence, it has become increasingly apparent that organizations need to think differently about security. While legacy tools like firewalls are no longer equipped to handle the modern IT ecosystem, SASE platforms like Bitglass are built for this exact moment. In this presentation, you will learn:
- The core components of a SASE platform like Bitglass.
- The functionality you need to secure cloud, web, and remote access use cases.
- Architectural considerations you should keep in mind when comparing SASE vendors.
Sponsored by

Presentation
A Strategy For Securing Your Everything; How Non-Integrated Solutions Challenge Overall Enterprise Security
Security practitioners understand the need to implement new controls that help their organizations’ defend against the rising number of attacks and Fifth Generation threats like the SolarWinds Orion supply chain hack. But slowed economic growth and the push to secure systems from sophisticated new threats challenges many companies.
These global market conditions underscore the importance of employing a consolidation strategy with a unified security architecture at its center that protects cloud, networks, endpoints, and mobile devices.
Join Grant Asplund, Growth Technologies Evangelist for Check Point Software Technologies, as he shares the building blocks for putting in place a consolidation strategy that:
- Increases security efficiency with a unified security architecture
• Improves your organization’s overall threat prevention profile
• Eliminates complexity caused by managing disparate systems
• Reduces total cost of ownership
Sponsored by

Keynote
Zero Trust or Bust: Build IT and they Won’t Come!
Ron Zochalski
Chief Technology Officer & Chief Information Security Officer Lake County Government - Superior Court Juvenile Division
Live Presentation
Conquering Cyber Risk in 3rd Party Communications
The Enterprise Content Firewall
To do their jobs, employees must share IP, PII, PHI, and all means of sensitive content with customers, suppliers, partners and a broad ecosystem of trusted 3rd parties. However, they put the organization at risk when they communicate across untrusted devices, networks, applications and identities. How can you prevent beaches and compliance violations from everyday 3rd party communications when you can’t even see what’s going on? This session explores the need for a next-generation “content firewall” that rises above packets and traffic to inspect content and communication, and thereby ensure confidentiality, compliance and control of risky 3rd party business processes.
Sponsored by

Live Panel Discussion
"Zero Trust is Not Enough"
The Zero Trust model is a big step forward in protecting organizations. But is it really enough to disrupt the cybercriminals? Criminals don’t care about trust. Equipped with endless time and resources, they will find a way to steal credentials, zero-day through barriers, and even attack new zero trust systems directly. Join this panel discussion on technologies and tactics that go beyond Zero Trust to protect your organization from cyberattacks.
Ron Zochalski
Chief Technology Officer & Chief Information Security Officer Lake County Government - Superior Court Juvenile Division
Sponsored by

Presentation
The Battle of Algorithms: How AI is beating AI at its own game
Among rapidly evolving technological advancements, the emergence of AI-enhanced malware is making cyber-attacks exponentially more dangerous, and harder to identify. As AI-driven attacks evolve, they will be almost indistinguishable from genuine activity, and conducted at an unprecedented speed and scale. In the face of offensive AI, only defensive AI can fight back, detecting even the most subtle indicators of attack in real time, and respond with surgical actions to neutralize threats – wherever they strike.
In this session, discover:
- How cyber-criminals are leveraging AI tools to create sophisticated cyber weapons
- What an AI-powered spoofing threat may look like, and why humans will not be able to spot them
- Why defensive AI technologies are uniquely positioned to fight back
Sponsored by
Presentation
Why Securing Email Has Changed
This webinar covers how email security has changed for organizations and how we can be better prepared for securing the cloud across multiple collaboration applications. Attackers are evolving through new entry points through platforms like Slack and Teams. Traditional approaches to email security like a SEG are no longer enough to protect organizations from insider threats and the full suite of applications. This presentation also demonstrates how emerging technologies such as AI and Machine Learning can help us with these attack types that are dynamic and ever changing.
Sponsored by

Live Presentation
Winning Against Ransomware
Sponsored by

Live Presentation
Achieving New Levels of Efficiency, Automation, & Visibility in Third-Party Risk Management
Whether a start-up or an enterprise, you are probably working with multiple vendors, using their software and reliant on their systems. Yet while these external vendors provide invaluable services, they also introduce significant risk to your company’s information security.
How do you know if your vendors are meeting required contractual, security and privacy obligations?
If you don’t have processes in place to assess the risks these third parties pose, then your answer is most likely you don’t. And this is critical: You need to know the risks of working with third parties and that you can trust them — because if they go down, your business may, too.
Assessing risk, however, can be incredibly complex. Traditional risk management approaches that rely on manual processes, spreadsheets and even survey methods don’t scale well and are not automated enough. And they certainly can’t support a third-party vendor network once it reaches a certain size: spreadsheets and email folders become overwhelming, ad hoc processes and reporting cycles create confusion, and manual reviews lead to missed issues and trends. In fact, the more successful an organization is – and the more third-party vendors they work with – the more automation and continuous monitoring are required.
Sponsored by
Live Presentation
Leveraging IAM for Effective and Efficient Threat Mitigation
There’s no question that the current cybersecurity landscape is constantly shifting and evolving as new threats and security solutions emerge. Increased cyber attacks and distributed workforces have created new challenges that require innovative solutions.
Faced with the challenge of managing identities and securing access to data and applications from a growing number of endpoints, what are the fundamental controls organizations need to maintain business continuity and secure their remote and hybrid workforce?
Hear from Lonnie Benavides – Head of Infrastructure and Application Security, Onelogin – for a discussion on practical information and advice regarding the utilization of identity and access management solutions to effectively mitigate modern cyber threats to your busines
Sponsored by

Live Presentation
Making Cybersecurity Work
Sponsored by

Presentation
Crawl, Walk, Run Your Segmentation Approach
While there are varying definitions of what zero trust actually is, there is one thing everyone can agree on – segmentation is a key pillar. Another thing everyone can agree on? Segmentation is hard. This presentation will highlight a way to begin your zero trust journey leveraging enforcement boundaries which will enable you to protect your digital crown jewels as you work through your end to end zero trust plan.
Sponsored by