Minneapolis Cybersecurity Conference
Thursday, April 9, 2026
Hybrid
5601 West 78th Street, Bloomington, Minnesota, USA, 55439



































Join Us in Minneapolis for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
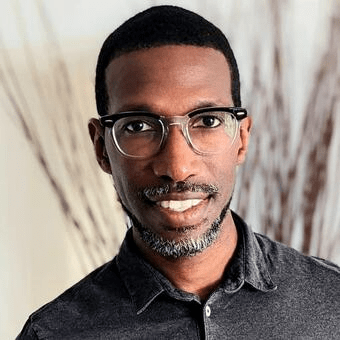
Keynote Speaker
“Making the world a little more secure - lessons learned from designing, building & running a global Product Security Program.”
Matthew Bohne
Vice President, Chief Product Security Officer Honeywell Corporate
At Honeywell, my leadership spans the full spectrum of product security, from leading the secure software development lifecycle to helping shape international cyber regulation to how to be compliant to them. My tenure has been marked by the successful deployment of a comprehensive cybersecurity program with a global team of over 290 product focused cybersecurity experts, impacting all of Honeywell’s diverse products and developers. Our team’s dedication to ‘security by design’ principles has fortified Honeywell’s cybersecurity posture on a global scale.
My 20+ years of expertise is deeply rooted in securing critical infrastructure and ensuring cybersecurity and privacy are woven into the fabric of product development. Drawing on my CISSP certification and hands-on experience in securing Nuclear, Pharmaceutical and Industrial Control Systems, I’ve established robust cybersecurity standards and cultivated a risk-informed approach, positioning Honeywell as a resilient leader in product security.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
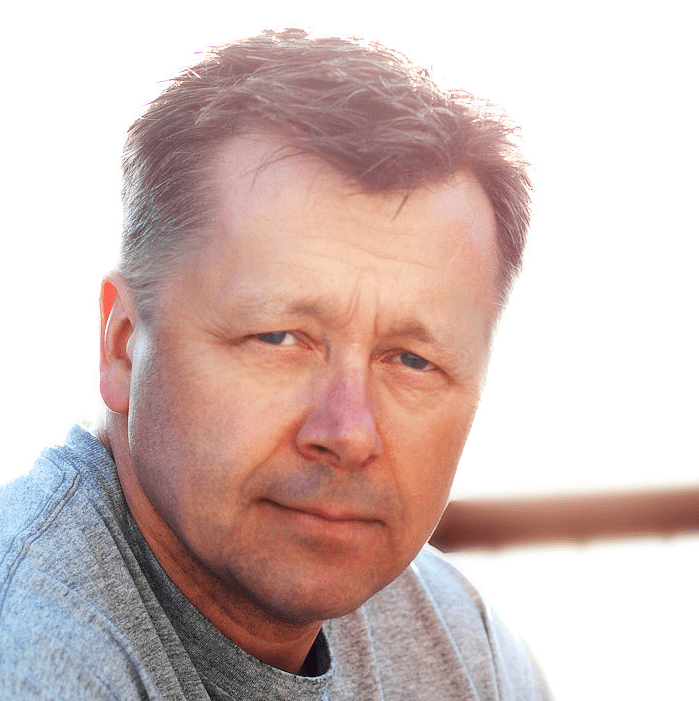
Conan Sandberg
Senior Director, Cyber Security Platform Science
Vince Aimutis
VP | Director of Information Services | CISO Federated Insurance
Matthew Bohne
Vice President, Chief Product Security Officer Honeywell Corporate
Doug Koch
FBI Cybersecurity Collaborator InfraGard Minnesota
Bindi Davé
Field Chief Information Security Officer Optiv
Sponsors
Premier Platinum Sponsors

Platinum Sponsors

Gold Sponsors







Silver Sponsors





















Bronze Sponsors

Partner





“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
But Our Identity Lives in the Cloud: Understanding Why Cloud Identity Is Easy to Run — and Hard to Recover
Sponsored by

Presentation
Stopping Cyber Threats, What Actually Works
Sponsored by

Presentation
AI: Cybersecurity’s Double Edge Sword
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
From Prompts to Permissions: The New Data Risk Model For AI
Sponsored by

Presentation
Prediction Is Not Protection
Application security has become a forecasting exercise.
We rely on CVEs, scanners, and severity scores to predict what might go wrong. But in an AI-driven world, where code ships faster and attacks move faster, prediction is no longer enough.
Forecasts don’t tell you what’s being exploited. They don’t tell you what’s reachable. And they don’t tell you what’s under attack right now.
This talk shows why forecast-only security breaks down in the machine-speed-era, and what replaces it.
You’ll see how runtime visibility changes application security from a guessing game into an operational discipline – revealing real attack paths, reducing noise, and enabling teams to detect and stop attacks in production.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
Making the world a little more secure - lessons learned from designing, building & running a global Product Security Program.
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Agentic SOC in Practice: Field Lessons on Powering and Governing AI Investigations
Sponsored by

Presentation
AI Hype vs Reality - Don't Secure the Spectacle
If AI headlines are driving your priorities, it’s time to recalibrate. This session dismantles three AI security myths, then addresses what’s more urgent: how today’s human risk scales into tomorrow’s agentic risk at machine speed. From misplaced trust in automation to behavioral blind spots, we’ll examine how psychology and prioritization shape enterprise exposure. You’ll leave ready to prioritize the risks that will define the next era.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
AI in Cybersecurity: Friend, Foe, or Both?
Sponsored by

Presentation
The End of Legacy Network Security
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!