Los Angeles, CA
Thursday, February 24, 2022
Hybrid
Keynote Speaker
“"Choosing Your Ground - Controlling Your Attack Surface"”
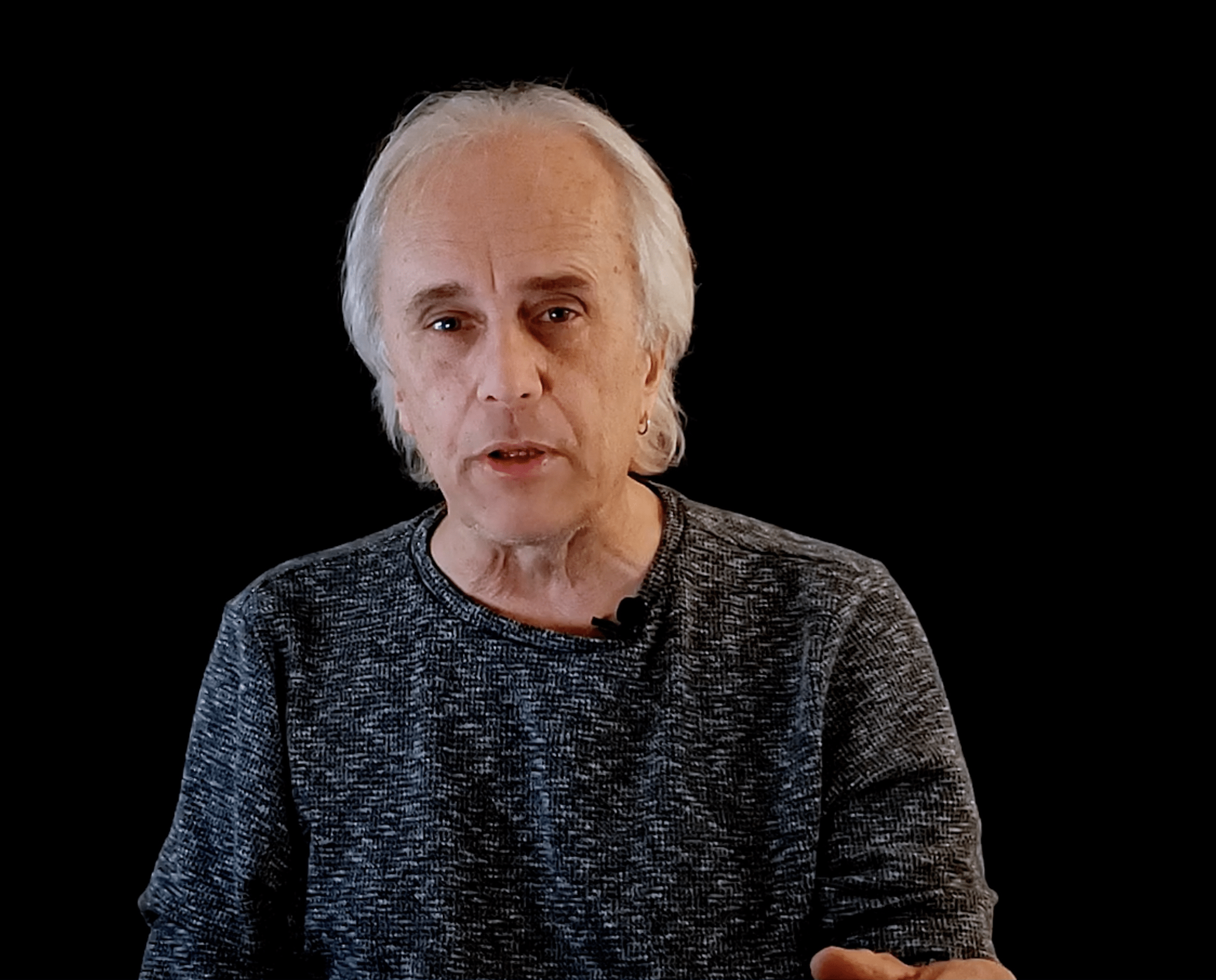
Jake Margolis
Chief Information Security Officer Metropolitan Water District of Southern California
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Marvin Cruz
Vice President, LA Metro Chief Technology Officer CGI
David Hanighen
Chief Information Security Officer Logix Federal Credit Union
Jake Margolis
Chief Information Security Officer Metropolitan Water District of Southern California
George Viegas
Chief Information Security Officer (CISO) and Privacy Champion Chapman University
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Fast and Furious Attacks: Using AI to Surgically Respond
Fast-moving cyber-attacks can strike at any time, and security teams are often unable to react quickly enough. Join Justin Fier, to learn how Autonomous Response takes targeted action to stop in-progress attacks, without disrupting your business. Includes real-world threat finds, case studies and attack scenarios.
· Topic for this session– Autonomous Response
· Explore today’s threats and challenges
· How advances in AI have been leveraged to allow for very surgical actions to be taken autonomously – where humans can no longer react fast enough.
Sponsored by
Presentation
Why Security Program’s Fail: The Maturity Model Required for Cyber Resiliency
Billions of dollars are spent annually to set up Security program’s and operation centers across every industry and yet, according to Risk Based Security, 3,932 breaches were publicly reported in 2020 alone. Why are Security program’s failing? Learn how the current operating model contributes to that failure and how a simple maturity model based on outcomes and use cases can make your organization more cyber resilient.
Key Learnings:
- Why an outcome-based approach is the only way to offer effective coverage and protection for your organization
- How the most successful Security programs use a comprehensive, strategic and end-to-end focused approach to address 95% of all operational issues at scale
- Why it is critical that Security programs become more use case-driven and full lifecycle workflow orientated
Sponsored by

Presentation
Choose Your Own” SOAR Adventure
Have you ever felt like managing your organization’s information security program is like one of the iconic “Choose Your Own Adventure” books? Choose one path, your ecosystem gets hit with ransomware, choose another technology becomes shelfware, choose another path and you get promoted to CISO.
Security is both hard and scary. Practitioners and leaders across the globe lose sleep every night wondering if they have made the right choices for their security program. Why is technology failing us? We have become increasingly reliant on technology, and for many immature organizations, it can add complexity, rather than solve for it.
This presentation will help viewers understand the need for a “back to the basics” approach, with emphasis on how repeatable, tested, and scalable processes are needed to ensure the success of automation that can demonstrate true ROI to an organization.
Together we can choose the adventure that ensures the Confidentiality, Integrity, and Availability of our organization’s ecosystem!
In this presentation, Director, Solutions Architecture, Alisa Moretto, will provide her insights from various use cases of the following points:
- How communication could be at the root of your failed launches
- How evaluating risk before and after SOAR can help prevent future failures
- How to avoid “shiny object syndrome”
- How to demonstrate your organization’s SOAR ROI
Sponsored by

Continuous Breach Attack Simulation - A Pragmatic Approach to Your Security Portfolio
This presentation examines some guiding principles that make a case for using continuous breach attack simulation as one of the best ways to test and exercise your security posture. We review the notion of abiding by the spirit of the compliance framework vs. the letter of that framework. We’ll then discuss how you can get the most benefit out of your security controls through simulating real-world scenarios without risk to your environment. We then conclude with the positive impact that performing continuous breach attack simulation can bring to your communications up to the executive and board level.
Sponsored by

Keynote
"Choosing Your Ground - Controlling Your Attack Surface"
Jake Margolis
Chief Information Security Officer Metropolitan Water District of Southern California
Presentation
Driving Zero Trust at Two Different Companies: Lessons Learned
- How to get started: Selling the strategy, people, process and technology
- How to make real progress in months, not years. Demonstrating continued business value
- Real world examples. Highlighting improvements to user experience and security posture.
- Tips and tricks, lessons learned and what to avoid
Sponsored by

Thank You, VPN – But Times Have Changed
The Journey to Zero Trust & The Top-3 Requirements Driving ZTNA Adoption
Did you know that Gartner research forecasts 60 % of enterprises will phase out most of their remote access VPNs in favor of ZTNA by 2023. Moreover, 40% of enterprises are anticipated to adopt ZTNA for other user cases by 2023. So, what’s driving the ZTNA adoption and why? We’ll discuss today’s pressing access challenges and 3 major use cases that are driving companies to implement zero trust network access, as well the business and IT requirements organizations should be aware of, when looking to adopt ZTNA.
At the end of the presentation, we’ll provide you access to a buyer’s guide checklist that you can use as a reference as you’re researching the best solution for your IT environment and requirements.
Sponsored by

Presentation
ZeroTrust Microsegmentation, Easier Than You Think
Sponsored by

Presentation
5 Considerations to Successfully Adopt Zero Trust
Zero Trust is not a new concept, but only in recent years have organizations prioritized efforts towards adopting the architecture. And in the past two years, with teams increasingly becoming distributed or remote, there is a greater need for Zero Trust than ever before. However, current tech stacks hardly offer ideal support for BYOD, let alone mass adoption of a mobile workforce.
With Zero Trust, organizations are reducing their attack surface, developing identity-first concepts in place of device IPs, building in continuous authentication, establishing a trust model that removes inherent trust, and moving towards the principle of least privilege and passwordless systems.
Join Twingate’s Product Manager Team Lead Anna Liu for a brief presentation discussing how to successfully build a foundation towards adopting and implementing a Zero Trust strategy.
After joining this session you’ll come away with:
- A path towards Zero Trust adoption
- Processes needed prior to tool evaluation
- Myths squashed and buzzwords decrypted
- Resources for building a Zero Trust architecture
Sponsored by