Kansas City, KS
Wednesday, August 10, 2022
Hybrid
Keynote Speaker
“"The Art of [cyber] War"”
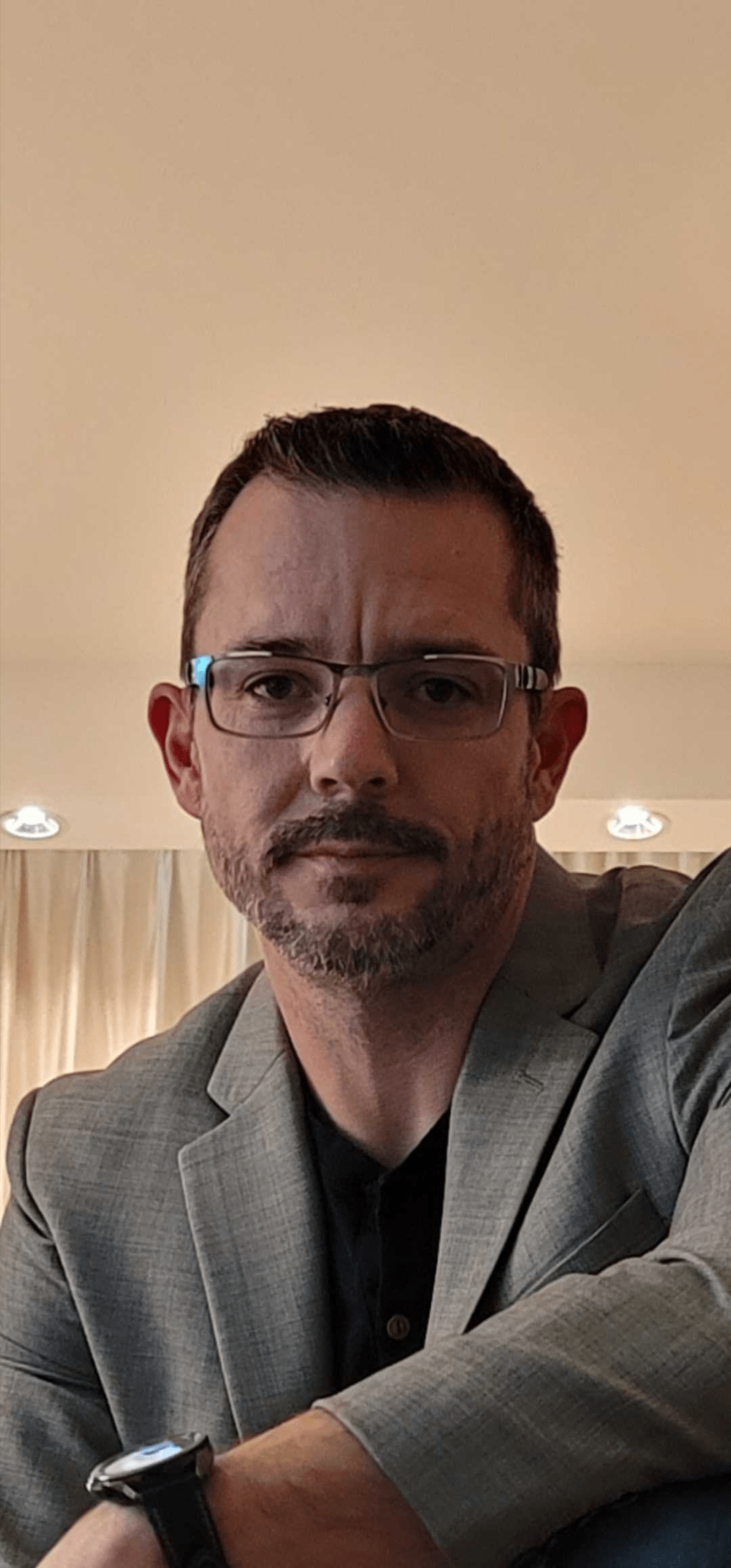
Michael Meis
Associate Chief Information Security Officer The University of Kansas Health System
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Maria Singh
President, Women in Security KC | Cybersecurity Professional & Certified Scrum Master | Leadership in DE&I T-Mobile
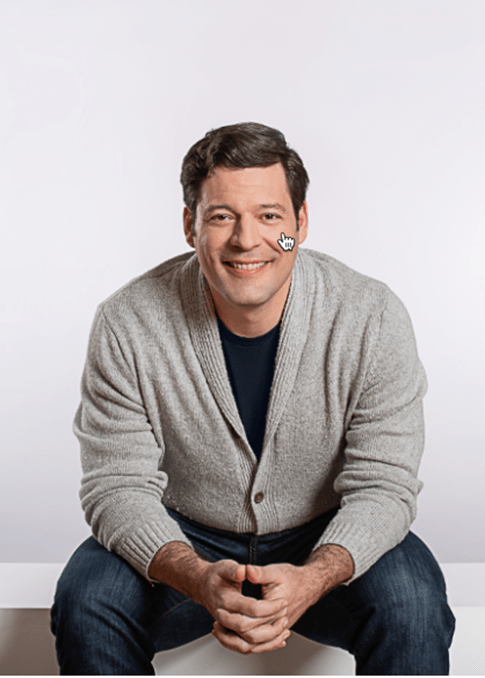
Chris Duffy
Vice President, Information Systems & Chief Information Officer ScriptPro
Sara Flores
Deputy CISO FNBO
Nathaniel Cole
Chief Information Security Officer WorkWave
Michael Meis
Associate Chief Information Security Officer The University of Kansas Health System
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Key Considerations for Choosing the Right Email Security Platform
Email is both a necessary communication medium, and the most vulnerable area for an attack. Year after year, adversaries find success in abusing email to gain a foothold into an organization—deploying malware, leaking valuable data, or stealing millions of dollars.
Unfortunately, email threats are only growing in number. Business email compromise accounts for 44% of all losses to cybercrime, and the 2021 Verizon DBIR holds that phishing remains the top entry point for breaches—a position it has held for years.
Does that mean email is doomed, and we should give up? Quite the opposite—instead, we should look to newer technologies and an integrated security strategy that provides a modernized approach to email defense.
Sponsored by

Presentation
Challenges in Detection and Response: Top 5 Threat Hunting Myths
Targeted ransomware attacks and data breaches are on the rise with increasing complexity and frequency. The pressure is on security teams to detect and respond to cyber incidents before they can affect business operations and your reputation.
Join us as we delve into the critical role proactive threat hunting plays in detection and response and learn what is required to be effective, debunking some of the common myths about SIEM, vulnerability scanning, threat intelligence, and more.
Sponsored by


Presentation
No Silver Bullets: A Programmatic Approach to Security & The Road to Zero Trust
In this session, we will discuss the need for a holistic approach to security and how de-centralization provides an opportunity to move towards zero trust.
Sponsored by

Presentation
Stopping Attacks, Not Your Business
With cyber-attackers continuously searching for new ways to outpace security teams, it can lead to a struggle to fight back without disrupting business operations. Join Darktrace in this session where we will explore the benefits of Autonomous Response as a must-have that goes beyond ‘defense’. Includes real-world threat finds and attack scenarios.
Sponsored by
Keynote
"The Art of [cyber] War"
War is one of the oldest concepts known to humankind. As more of our world moves into cyberspace, we stand upon the edge of a new evolution many people think upends what we know about warfare and adversarial dynamics. This new evolution also brings layers of complexity and velocity we are still grappling to understand. It’s time to take a macro look at the foundations of warfare strategy, and how we can apply Sun Tzu’s timeless guidance to our own cyber defense programs.
Michael Meis
Associate Chief Information Security Officer The University of Kansas Health System
Presentation
Printers, Phones, and Cameras: A Story of Two Million Interrogated Devices
We have examined millions of IoT, OT and network devices in the Enterprise at Phosphorus Cybersecurity. This includes everything from desktop VoIP phones to BACnet devices such as power distribution and chillers, to cameras, thermostats, door lock controllers, fire control panels, and lots of printers. Phosphorus finds a 90% common corpus of vendors that have been deployed in the Enterprise, and almost all are uncompleted, unmanaged, and insecure. With our own data, we can positively confirm remarkable statistics of extended IoT in the enterprise; the state of xIoT security today is reminiscent of the 1990s. As we walk through a few million “Things,” we will examine key statistics, such as prevalence of CVEs, commonality of default credentials, the half-life of xIoT firmware, and what measures can be taken to stay ahead of the problem.
Sponsored by

Presentation
The Past, Present and Future of Strong Authentication
Authentication is a foundational element of every cybersecurity program. With more than 80% of data breaches and most ransomware incidents stemming from credential-based attacks (e.g., phishing, credential stuffing, RDP brute, etc.), it has become clear that passwords are a fatally flawed authentication method. Unfortunately, many common solutions are “band-aids” on top of passwords and are lacking from both a security and user experience perspective. Replacing passwords as an authentication factor is finally possible. While eliminating passwords is a critical step in stopping credential-based attacks, it is just a first step on the journey to advanced authentication and access control needed to achieve zero trust.In this talk, we will discuss:
- A brief history of authentication
- Changing requirements in the new work from home(or anywhere) business model and cloud-centric architectures
- Can we gain risk-reduction improvements by converging the traditionally disparate identity and security processes and technologies?
- A case for continuous user authentication
- What is device risk and why is the real-time assessment of endpoint security important
Sponsored by

Presentation
Open Source Developers Are Security’s New Front Line
Bad actors have recognized the power of open source and are now beginning to create their own attack opportunities. This new form of assault, where OSS project credentials are compromised and malicious code is intentionally injected into open source libraries, allows hackers to poison the well. In this session, Sonatype will explain how both security and developers must work together to stop this trend. Or, risk losing the entire open source ecosystem.
· Analyze, and detail, the events leading to today’s “all-out” attack on the OSS industry
· Define what the future of open source looks like in today’s new normal
· Outline how developers can step into the role of security, to protect themselves, and the millions of people depending on them
Sponsored by