Houston, TX (Western Region)
Thursday, October 21, 2021
Virtual
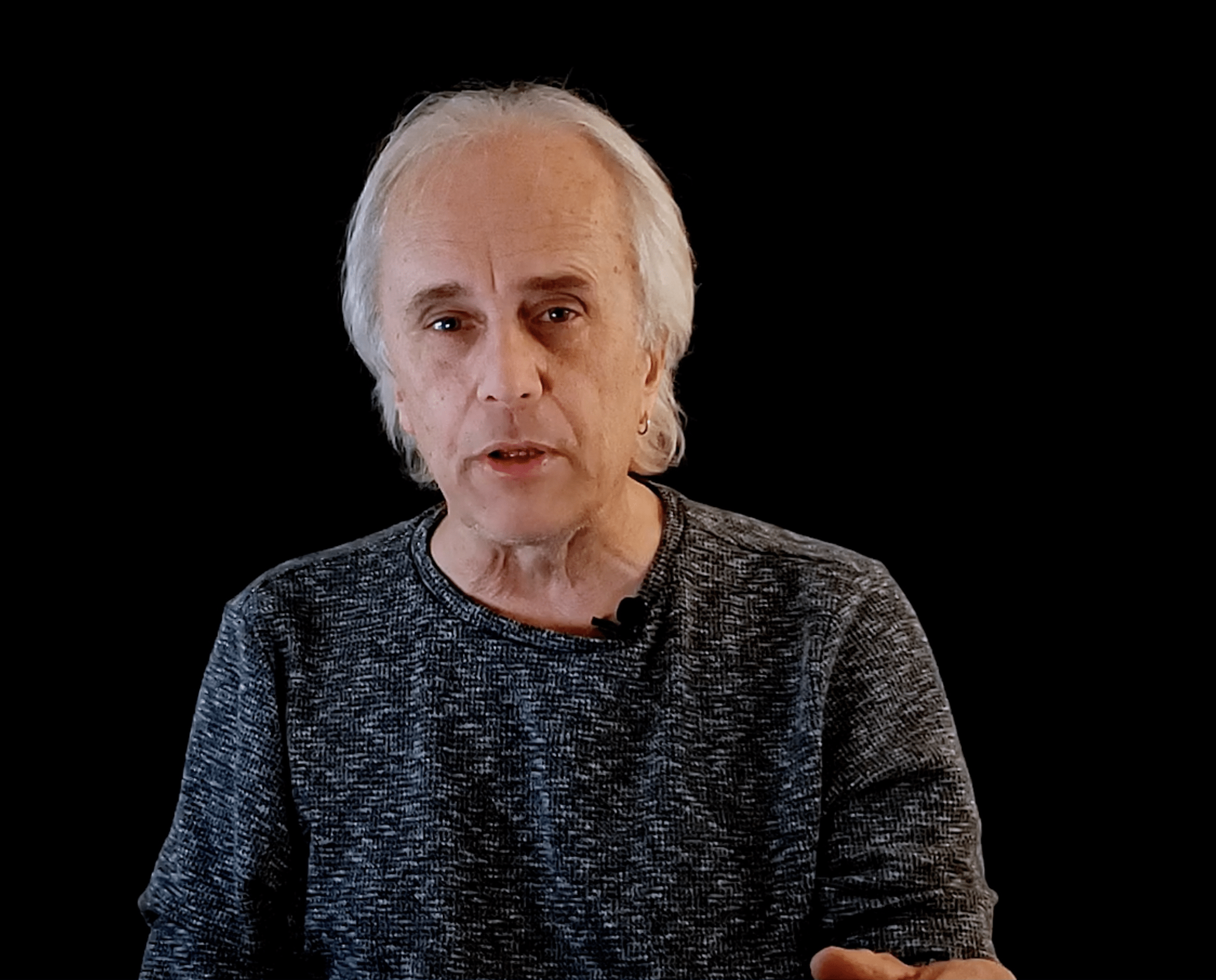
Keynote Speaker
“Cybersecurity & The Board: Choosing success over the Sarlacc Pit”
Brian Contos
Chief Security Officer Phosphorus Cybersecurity
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions
Presentation
Rise of Secure Access Service Edge (SASE)
Secure access service edge has quickly emerged as a hot topic in cybersecurity, but what exactly does it mean and why should organizations care? As cloud migration, BYOD adoption, and remote work have skyrocketed in prevalence, it has become increasingly apparent that organizations need to think differently about security. While legacy tools like firewalls are no longer equipped to handle the modern IT ecosystem, SASE platforms like Bitglass are built for this exact moment. In this presentation, you will learn:
- The core components of a SASE platform like Bitglass.
- The functionality you need to secure cloud, web, and remote access use cases.
- Architectural considerations you should keep in mind when comparing SASE vendors.
Sponsored by

Presentation
Insider Risk Management: The alternative to traditional data protection is here!
Sponsored by
Keynote
Cybersecurity & The Board: Choosing success over the Sarlacc Pit
Presentation
Death, Taxes, & Ransomware: Make the Inevitable, Avoidable
Sponsored by

Panel Discussion
"CISO roundtable with the Human API"
Jonathan Kimmitt
Chief Information Security Officer, Alias Cybersecurity Former CISO The University of Tulsa
Presentation
Building a Response Strategy to Advanced Threats
Sponsored by

Presentation
Crawl, Walk, Run Your Segmentation Approach
Sponsored by

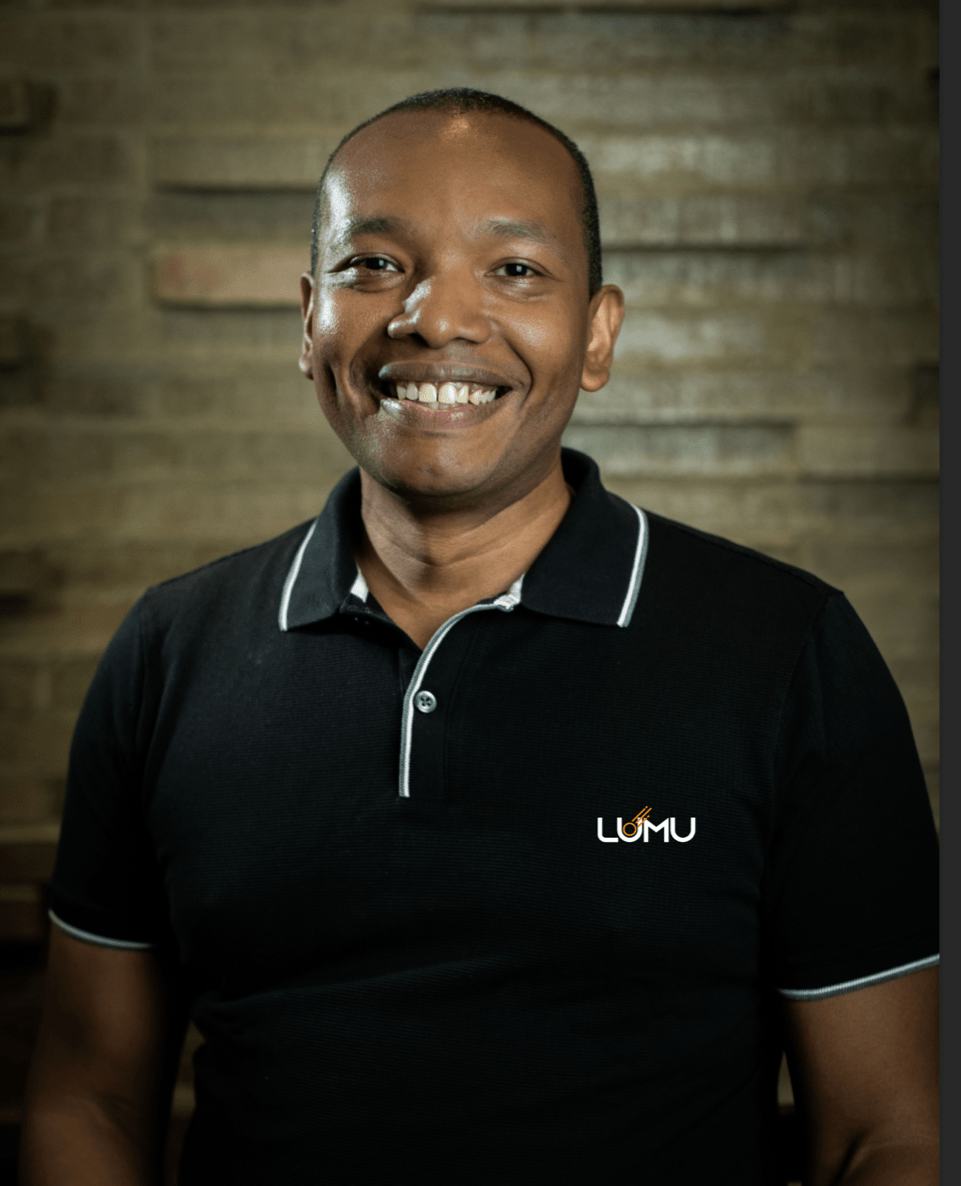
Detecting and Responding to Threats at the Speed of Business
- Reduce MTTD and MTTR with context-driven investigations.
- Proactively hunt for threats while overcoming the security skills shortage.
- Ensure your security tech stack is working for you, not against you.
- Take a “threat-centric” approach to decrease caseload by as much as 80%.
Sponsored by

Presentation
7 Habits of Highly Effective Cybersecurity Operations
Sponsored by

Presentation
Zero Trust and Access Management as a Service (AMaaS)
Organizations are moving to Zero Trust Security, and Identity and Access Management, IAM, is a key element of this new strategy. Modern Identity as a Service (IDaaS) platforms solve half of the IAM problem: Identity. Access Management as a Service (AMaaS), an emerging strategy, solves the other half: Access.
Sponsored by

Presentation
A Strategy For Securing Your Everything; How Non-Integrated Solutions Challenge Overall Enterprise Security
Security practitioners understand the need to implement new controls that help their organizations’ defend against the rising number of attacks and Fifth Generation threats like the SolarWinds Orion supply chain hack. But slowed economic growth and the push to secure systems from sophisticated new threats challenges many companies.
These global market conditions underscore the importance of employing a consolidation strategy with a unified security architecture at its center that protects cloud, networks, endpoints, and mobile devices.
Join Grant Asplund, Growth Technologies Evangelist for Check Point Software Technologies, as he shares the building blocks for putting in place a consolidation strategy that:
- Increases security efficiency with a unified security architecture
• Improves your organization’s overall threat prevention profile
• Eliminates complexity caused by managing disparate systems
• Reduces total cost of ownership
Sponsored by