Houston, TX (Western Region)
Wednesday, October 21, 2020
Virtual
















Join FutureCon CyberSecurity Events in Houston!
This event is the perfect opportunity to discover cutting-edge security approaches and learn how to manage risk in the ever-changing cybersecurity world.
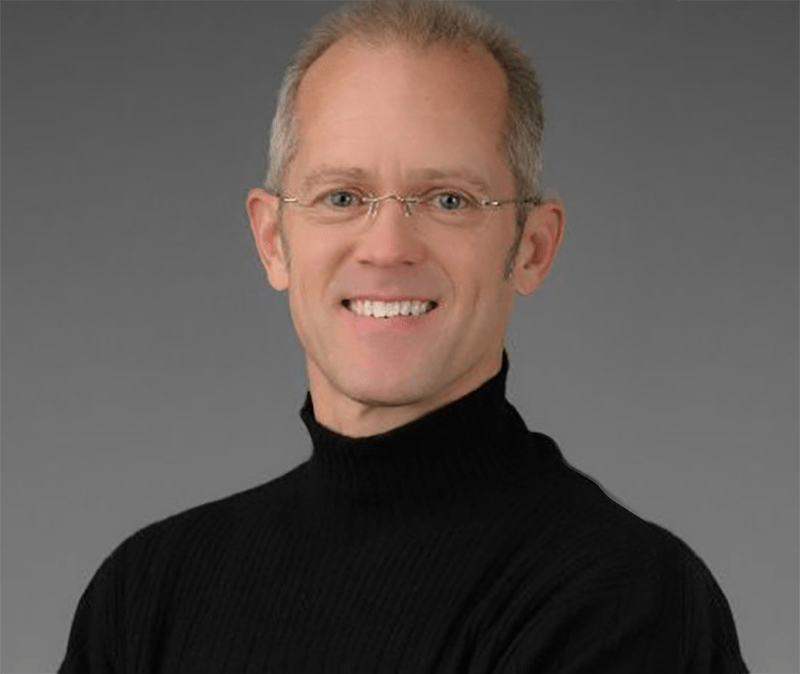
Keynote Speaker
“Lessons Learned from 2020 and what will 2021 Bring”
James Morrison
FBI Cyber (Ret), CISSP, MBA, Veteran National Security Specialist/Security Evangelist at Intelisys
Experienced Cybersecurity Expert with a demonstrated history of working in the IT industry. Talented speaker with the ability to synthesize data into easy to understand presentations. Skilled in Intelligence Analysis, Python, Analytical Skills, Government, and Computer Science. Strong engineering professional with a Master of Business Administration (MBA) focused in Technical Management from University of Phoenix.
CISO/Industry Leader Panel
CISO Panel: The Security Impact of The Coronavirus
Laureen Smith
Executive - Cybersecurity Advisory LJ Marketing & Communications
Josh Kuntz
Chief Information Security Officer Texas Workforce Commission
Jeff Lush
Chief Information Officer Air University at United States Air Force
Richard Rushing
Chief Information Security Officer Motorola Mobility
Sponsors
Premier Platinum Sponsors

Platinum Sponsors
Gold Sponsors




Silver Sponsors






Partner



About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Live
Opening Introductions
Networking
Sponsor Virtual Booth Networking Time
On-Demand Presentation
Cyber AI & Geopolitics: Managing Tomorrow's Cyber Risk
Against a backdrop of escalating geopolitical tensions and an ever-evolving threat landscape, the risk of cyber-attacks to governments and the private sector alike has never been higher.
Join Darktrace’s Director of Strategic Threat, Marcus Fowler, and CISO, Americas, JR Tietsort to discuss this new era of cyber-threat – and how Cyber AI can help defenders regain the upper hand.
This session will explore:
• How nation-state attacks are changing
• How organizations can respond to the classic balance of security and productivity
• How organizational maturity in risk management is maintained whilst ensuring cyber defense
Sponsored by
Live Presentation
Conquering Cyber Risk in 3rd Party Communications
Sponsored by

Networking
Break
Live Panel Discussion
CISO Panel: The Security Impact of The Coronavirus
Sponsored by

Networking
Break
On-Demand Presentation
Best Practices – PAM Security and Data Privacy
Sponsored by

On-Demand Presentation
Seeing the forest through the trees - A risked based approach to maturing your VMP
Sponsored by
On-Demand Presentation
Secure Shell Privileged Access: Risk & Compliance Challenges
Sponsored by

Break
Break
On-Demand Presentation
Making the Case for Authentication as a Platform
As organizations adopt advanced authentication practices, it’s critical to consider the varied modalities your organization requires. The “solution” should not be one that’s built from a collection of point solutions. For this reason, many businesses are turning to authentication solutions that are built as a platform. This holistic solution is accommodating to different modalities, applications and form factors. It can also control the authentication and credential management lifecycle. In this session, the experts from HID® Global will:
- Address the most common challenges and concerns for enterprise organizations attempting to streamline authentication
- Detail the intricacies of the authentication lifecycle
- Help you identify what to look for in an authentication platform that meets your organization’s needs
Sponsored by
Live Keynote
Lessons Learned from 2020 and what will 2021 Bring
James Morrison
FBI Cyber (Ret), CISSP, MBA, Veteran National Security Specialist/Security Evangelist at Intelisys
Networking
Break
On-Demand Presentation
The Growing Need for Identity & Access Management to Support Digital Business Initiatives
Sponsored by

On-Demand Presentation
Rational Approach to Zero Trust
Security vendors and analysts are pushing the “zero trust” message – but zero trust is not a product that can be bought. It is an approach to security policy and processes. This brief talk discusses the “low hanging fruit” in applying zero trust principles to an organization’s security program.
Sponsored by
On-Demand Presentation
Destructive Objects: The New Attack Vector
Files and destructive objects are emerging as a significant new attack vector, disrupting businesses’ efforts to bring products and services online via new web and mobile applications. These new digital processes rely on the creation, transfer, and sharing of rich content as files which transport this data to deliver the right experience to the recipient. However, these same files can be leveraged by attackers by inserting malware into these binary objects, which often go undetected thereby introducing significant risk to the business.
In this session, we’ll discuss:
• What are destructive objects and why are they a concern to your business, your digital ecosystem, and subsequently your employees, partners, and customers
• How are these files impacting organizations, including your digital experience, SOC performance, and software supply chains
• How is explainable threat intelligence improving detection rates, accelerating response times, and creating greater SOC and DevOps efficiencies
Sponsored by