Des Moines Cybersecurity Conference
Thursday, September 25, 2025
Hybrid



















Join Us in Des Moines for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
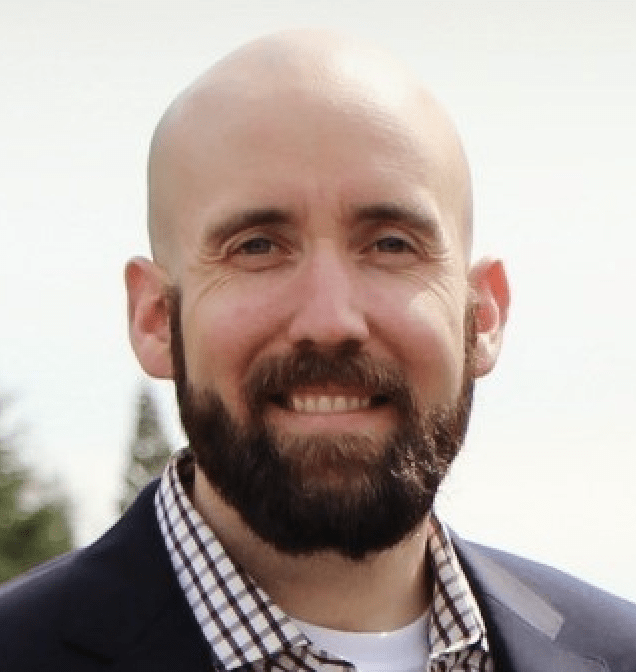
Keynote Speaker
“Recalibrate Your Thinking: Overcoming Bias to Build Proactive, Trust-Centered Security Programs”
Robert LaMagna-Reiter
Vice President, Chief Information Security Officer WoodmenLife
Robert LaMagna-Reiter is a leading, trusted Information Security & Risk Management professional. As CISO for WoodmenLife, Robert leads information security strategies and roadmaps; oversees cyber risk management; security architecture and engineering; and security operations. Leveraging more than 20 years of expertise, Robert helps others deliver value through proper security strategy aligned to zero-trust principles. Robert’s experience includes leadership roles in information security for transportation, government communications, retail, e-commerce, managed services, SaaS & insurance industries. Robert is a Team8 Villager, and serves as Advisory Board President for SOFTwarfare, Zero Trust Initiative Leader for the CyberTheory Institute, and Zero Trust Expert Committee Member for the Cloud Security Alliance.
CISO/Industry Leader Panel
Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices
Sponsors
Platinum Sponsors

Gold Sponsors








Silver Sponsors










Partner




“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
AI’s Influence on Cybersecurity and How to Prepare
We’ll explore how AI is reshaping cybersecurity—both as a threat and a defense tool. This isn’t just a technical issue; it’s a strategic governance challenge. Boards and executives must understand the risks, opportunities, and oversight responsibilities that come with AI’s growing influence.
Sponsored by

Presentation
The Current Threat Landscape Requires a Unique Approach
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
From Spam to Sophistication: How Email Threats Evolved with Phishing-as-a-Service
Since the mid-1990s, phishing has evolved into a foundational attack method and remains one of the most common cybersecurity threats organizations face today. It’s also become a key focus of employee training programs across industries. In this session, we’ll explore the history of email security, trace how phishing techniques have adapted over time, and take a closer look at the emerging threat of Phishing-as-a-Service (PhaaS) — a new, scalable model that’s lowering the barrier to entry for cybercriminals.
Sponsored by

Presentation
Shift Show: Why Our Best Intentions in AppSec Are Failing
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
Recalibrate Your Thinking: Overcoming Bias to Build Proactive, Trust-Centered Security Programs
Security decisions aren’t made in a vacuum — they’re often shaped by mental shortcuts, outdated assumptions, and pressure to act fast. Cognitive biases like anchoring, availability, and confirmation bias often sneak into risk assessments, leading to reactive strategies, overemphasis on headline threats, or clinging to legacy controls.
This session will dive into how we can break free from “we’ve always done it this way” thinking and steer their programs with greater clarity and impact. We’ll explore how common decision-making traps surface in the real world and how they quietly shape policy, control choices, and impact standard work. By taking a fresh lens on how bias affects your program’s security posture, we’ll discuss tactics to shift from a reactive to proactive strategy through practical methods that leverage data to build a trust-aligned program that scale.
Whether you’re maturing a SOC, leading cloud transformation, securely enabling artificial intelligence efforts, or maturing your zero-trust roadmap, this session will equip you with tools to spot hidden biases — and replace them with stronger, clearer judgment.
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
How to Get Away with Cybercrime
We often talk about threats in terms of dollars lost, data stolen, or headlines made. But the real threat lives deeper—in the structure, the strategy, and the growing ambition of the actors behind the screen. Today’s cybercriminals don’t just encrypt files; they build economies, launder, influence, and forge alliances that stretch across borders and industries. In this talk, we’ll peel back the layers of modern cybercrime and explore how loosely affiliated hackers have evolved into organized syndicates. These groups operate more like multinational corporations than rogue disruptors—complete with HR departments, recruitment pipelines, insider relationships, and state protections.
Sponsored by

Presentation
Identity Is Necessary—AI‑Native Defenses Are Next
From roles to real‑time policy, trust layers, and AI‑driven detection
AI and large language models are transforming how organizations operate—and how attackers exploit new gaps. Traditional identity and Zero Trust controls remain essential, but they’re not enough for AI‑driven workflows. This session introduces three emerging defense patterns designed for the AI era: adding a trust layer to monitor and govern model interactions, enabling security operations to detect and respond to AI‑specific threats, and securing the AI supply chain to maintain integrity and resilience. We’ll connect these patterns to leading risk frameworks and conclude with a practical decision aid and clear next steps for securing your organization.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Cyber Defense Strategies For Earlier Detection and Faster Response
Sponsored by

Presentation
Be Breach Ready
In today’s threat landscape, breaches are no longer rare events—they’re a reality. While preventing every intrusion is unrealistic, limiting its impact is achievable. This session explores how microsegmentation serves as a foundational control in implementing Zero Trust, helping organizations contain attacks and maintain business continuity.
Microsegmentation enables security teams to isolate workloads, users, and devices by creating fine-grained security zones across IT, IoT, and OT environments. When applied correctly, it prevents unauthorized lateral movement and reduces the blast radius of cyberattacks—especially crucial in hybrid and legacy infrastructures.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!