Dallas, TX
Thursday, January 20, 2022
Hybrid
Live Episode of “The Cyber Ranch Podcast”
““Running an Effective Pen Test Program””
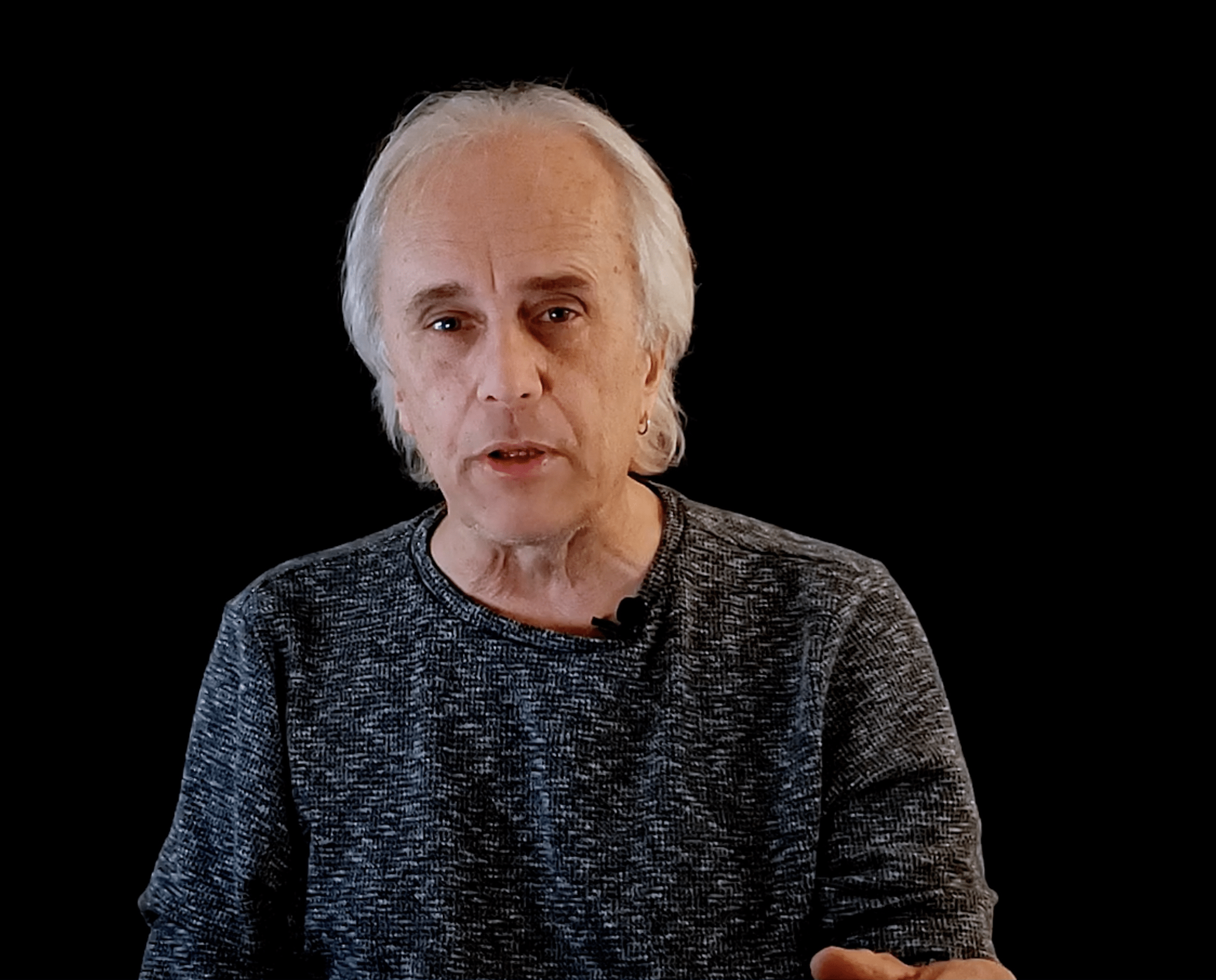
Phillip Wylie
Penetration Tester | Instructor | Keynote & International Speaker | Best Selling Author | Podcast Host Horizion3.ai
Live Episode of “The Cyber Ranch Podcast”
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
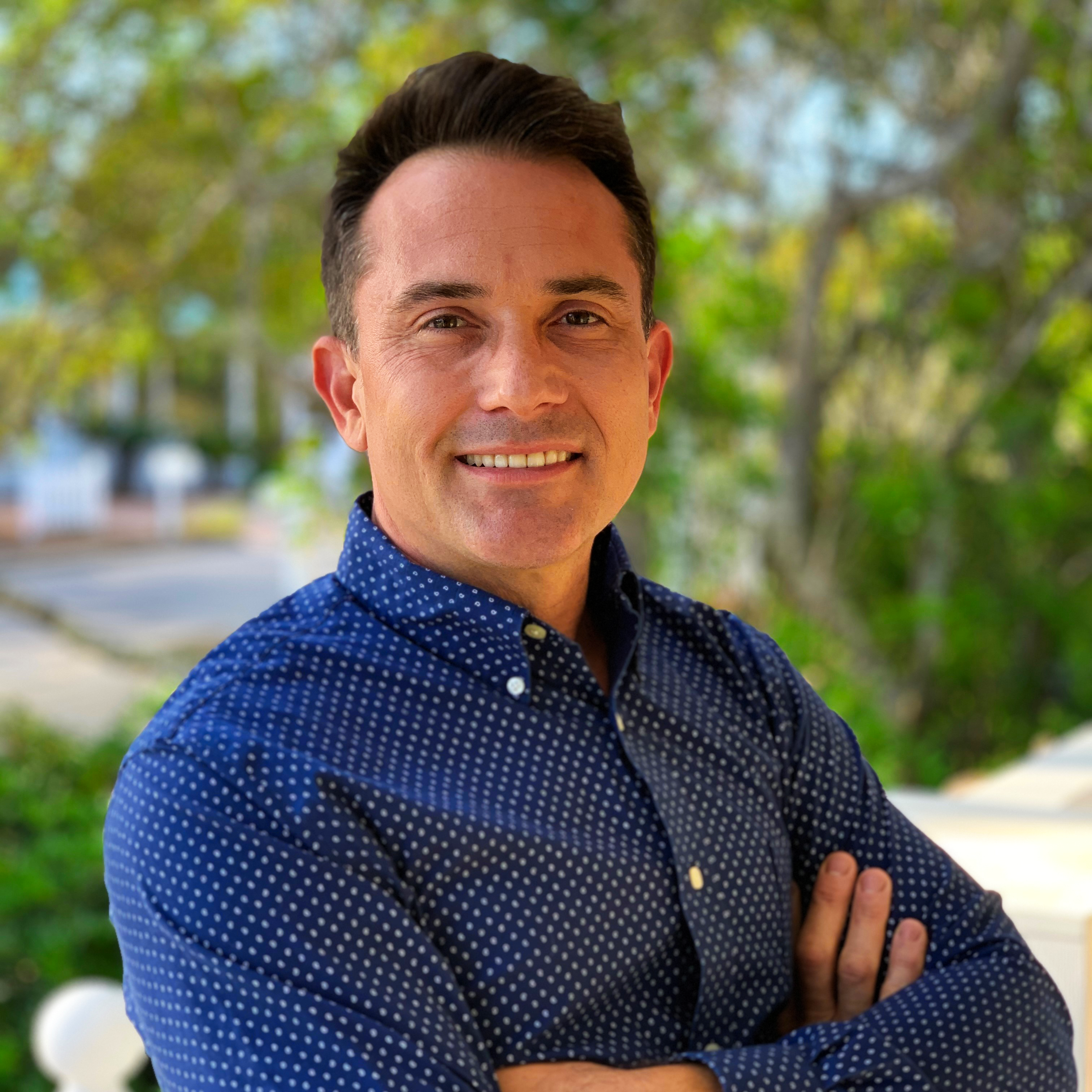
David Belanger
Chief Security Officer Bestow
Pat Benoit
Global Chief Information Security Officer Brink’s Inc
Jessica Nemmers
Chief Security Officer Elevate Credit
Jaimin Shah
VP & Chief Information Security Officer SRS Distribution
Randy Potts
Chief Information Security Officer Real Time Resolutions, Inc.
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
2022 Cyber Security Predictions and the Future of CSPM
As we enter the new year, this presentation will share several 2022 predictions from a number of Check Point cyber security experts as well as shed light on the future direction of cloud security posture.
Sponsored by

Presentation
Why Security Programs Fail: The Maturity Model Required for Cyber Resiliency
Billions of dollars are spent annually to set up Security program’s and operation centers across every industry and yet, according to Risk Based Security, 3,932 breaches were publicly reported in 2020 alone. Why are Security program’s failing? Learn how the current operating model contributes to that failure and how a simple maturity model based on outcomes and use cases can make your organization more cyber resilient.
Key Learnings:
- Why an outcome-based approach is the only way to offer effective coverage and protection for your organization
- How the most successful Security programs use a comprehensive, strategic and end-to-end focused approach to address 95% of all operational issues at scale
- Why it is critical that Security programs become more use case-driven and full lifecycle workflow orientated
Sponsored by

Presentation
Crawl, Walk, Run Your Segmentation Approach
Sponsored by

Presentation
Beyond the breach: A look at the modern security testing challenge
If security testing and validation is conducted, then why are breaches and attacks still successful? In this presentation Joe Vest, shares perception vs reality on security operations preventing, detecting, assessing, monitoring, and responding to cyber threats and incidents.
Sponsored by

Lunch
Keynote
“Running an Effective Pen Test Program”
Live Episode of “The Cyber Ranch Podcast”
Phillip Wylie
Penetration Tester | Instructor | Keynote & International Speaker | Best Selling Author | Podcast Host Horizion3.ai
The Next Class of Browser-Based Attacks
There are two distinct characteristics that all threat actors tend to share. First, they focus on avoiding detection by any means. Second, while some go after specific targets, many opt to aim their tactics on vectors that will reap the greatest rewards. After all, a big pond with many fish increases everyone’s chances at success.
Today, given that a majority of business users spend 75% of their working day in a web browser, it’s quickly become the prime target for cyber swindlers. While malware once had to be downloaded to pose a real risk, now, it’s a dynamically generated threat toolkit built in the web where employees are productive.
During this insightful discussion, prepare to learn about the next class of browser-based attacks, but most importantly, share how organizations can protect that productivity. Key takeaways include:
- The anatomy of recent browser-based attacks
- Exposing why network security today is broken
- The technology approach proven to eliminate these threats
Sponsored by

Presentation
Stopping Ransomware with Autonomous Response
New strains of ransomware are leaving organizations vulnerable – too often, security teams lack the ability to respond proportionately to an attack, leading to cyber disruption across the organization.
Join Brianna Leddy, Darktrace’s Director of Analysis, as she unpacks some of today’s most advanced ransomware threats. Learn how Self-Learning AI understands the organization to reveal every stage of a ransomware attack – and takes targeted, autonomous action to stop the threat in its tracks.
This presentation will discuss:
· Recent ransomware threat trends, including double extortion and RDP attacks
· How Autonomous Response takes action to contain an emerging attack, even when security teams are out of office
· Real-world examples of ransomware detected by Darktrace AI – including a zero-day and an attack initiated on Christmas Day
Sponsored by
Presentation
Delivering Zero Trust in the real world: A winning methodology that enabled 150,000 users to escape their legacy VPN’s
As we settle into life with COVID, the topic of zero trust security and a remote workforce is top of mind for all enterprise security teams. During this session you’ll hear from security practitioners who were responsible for the zero trust strategy and implementation at two Fortune 500 global enterprises – Adobe & Cisco. They will share their experiences and tips for rolling out zero trust methodologies at scale.
The audience will gain understanding in:
- How to get started: Selling the strategy, people, process and technology
- How to make real progress in months, not years. Demonstrating continued business value
- Real world examples. Highlighting improvements to user experience and security posture.
- Tips and tricks, lessons learned and what to avoid
Sponsored by

Presentation
Securing Trust - How The Security Leader Enables Business Outcomes
Sponsored by

Panel Discussion
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
WRAP-UP NETWORK RECEPTION
WRAP-UP NETWORK RECEPTION WITH LIVE MUSIC/COCKTAILS AND HORS D”OEUVRE’S
HOUSE OF BLUES FAVORITE MUSIC FROM “WHISKY PANTS”