Vice President (VP) with experience in Managing Full Information Security, Technology Portfolio and Risk Governance in the Financial, Investment Banking, Educational and International Institutions. I have managed multi million-dollar budget with the focus of delivering on time and on budget results providing the maximum (ROI) Return on the Investment on the Total Cost of Ownership (TCO). In addition, as a Certified Information Security Manager, I am a firm believer in developing a educational, security and risk programs that are aligned with the organizations strategic vision to Maximize Profitability and Minimize the Impact Risk, Including Cyber Related Events.
Chicago Cybersecurity Conference
Thursday, January 23, 2025
Hybrid

























Join Us in Chicago for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
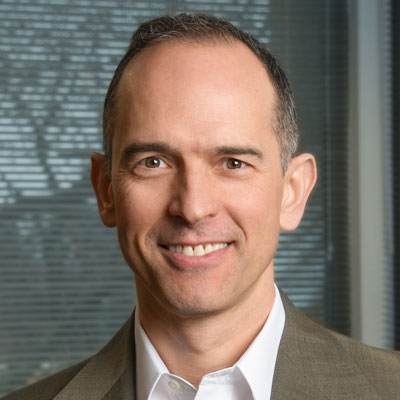
Keynote Speaker
“Strategic Security = Alignment to the Organization's Strategy”
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Ramona Ratiu
Cyber Security Operations | Head of Cyber Resilience Testing Program Zurich Insurance Company
LeRoy M Sims
Vice President Information Technology Vantedge Medical
Chris Carter
VP & Head of Security Blue Mountain Universal
M. Bukky DaSilva
Business Information Security Officer Blue Cross and Blue Shield
Terry Kurzynski
Founder HALOCK Security Labs
Sponsors
Premier Platinum Sponsors

Platinum Sponsors

Gold Sponsors







Silver Sponsors
















Partner




“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Chicago Marriott Oak Brook
Agenda
Times are subject to change
8:00 am
Opening Introductions | Check In | Networking
Presentation
8:45 am
A Complete Security Blueprint
Do you know what’s next in your security program? Join Brad Nigh, FRSecure’s Consulting Team Strategist, as he discusses a pragmatic approach to determining what security efforts will give you the most impact. By analyzing your existing program, work completed, and using our categorization—foundational, developing, and mature—you should be able to place yourself and get an idea of what’s next for your security program. This is a session you won’t want to miss and there will probably be some dad humor!
Sponsored by

Presentation
9:15 am
Data Security in a SaaS, Cloud and Gen AI Era: Lessons Learnt and Best Practices for CISOs and Security Practitioners
As SaaS applications like O365, Google workspace, Salesforce, Slack, Atlassian, cloud platforms like AWS, Azure, and Gen AI tools like ChatGPT, Copilot dominate modern workflows, they also introduce complex security challenges for CISOs, security leaders, engineers, and practitioners. These include expanding attack surfaces, misconfigured systems, and sensitive data exposures, all of which demand innovative solutions beyond traditional security tools.
In this session, we’ll dive into:
• Emerging risks in SaaS, cloud, and Gen AI environments, including real-world examples of breaches and misconfigurations.
• Actionable strategies to gain full visibility into sensitive data, enforce compliance, and protect against insider and external threats.
• Case studies highlighting successful approaches to securing sensitive data in Gen AI workflows and SaaS platforms.
• Future trends such as Zero Trust principles and AI-driven security automation that will reshape how we protect organizational data.
Designed for CISOs and security practitioners, this talk offers practical takeaways to enhance your data security posture while balancing productivity and compliance in a SaaS-first, AI-driven era.
Sponsored by

Presentation
9:45 am
Techniques to Evolve Risk Governance: How Executives Make Informed Cyber Decisions
Regulators and standards bodies are requiring us to evolve cybersecurity governance. This session will help you understand how to make this work in your favor:
- Understand what NIST and regulators mean by “governance.”
- Help non-technical executives make informed cybersecurity decisions.
- Use governance to your advantage.
- Define a “clear line of acceptable risk” that everyone agrees to.
- Justify your controls program, even after a breach.
Sponsored by

10:15 am
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
10:45 am
The Hidden Risks of GenAI: Challenges in Detecting Data Leaks in GenAI/LLM Transactions
The rise of Generative AI (GenAI) and Large Language Models (LLMs) has transformed how businesses operate, but it also introduces new security risks. Sensitive data can inadvertently leak during interactions with these tools, as seen in high-profile incidents like the Samsung data leak (https://mashable.com/article/samsung-chatgpt-leak-details)
Also, Traditional Data Loss Prevention (DLP) tools are ill-equipped to detect and prevent such leaks in LLM transactions, creating significant security blind spots.
In this session, we will examine few real-world examples of AI-related data exposure, explore why LLM transactions pose unique challenges for existing security frameworks, and discuss practical approaches to mitigating these risks. Attendees will gain insights into evolving their DLP strategies to address the dynamic threats posed by GenAI tools in enterprise environments.
Sponsored by

Presentation
11:15 am
Rethinking Cybersecurity for Covert Application Risks
Application and API security are stuck in a spin cycle that AI can’t save. The prevailing approach relies on developers to fix vulnerabilities while holding SecOps teams accountable for breaches, creating an unsustainable dynamic. It’s time to rethink the strategy: by detecting and responding to both attacks and vulnerabilities directly in production. Join us to see how you can evolve your security program with Application Detection and Response (ADR) to achieve more effective, efficient security.
Sponsored by

11:45 am
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
12:00 pm
Lunch
Keynote
12:15 pm
Strategic Security = Alignment to the Organization's Strategy
1:15 pm
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
1:45 pm
SOC Strategies to Detect Earlier and Respond Faster
Sponsored by

Presentation
2:15 pm
Using Threat-Informed Defense to Stop Boiling the Ocean
It’s a simple question at the root of what we do as security professionals: Can we defend our assets and infrastructure against a specific threat? Answering this question using traditional methods and without Threat-Informed Defense is time-consuming, expensive, and most likely just a guess.
Sponsored by

2:45 pm
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
3:00 pm
Global Threat Trends and Resilience Strategies
Sponsored by

Presentation
3:30 pm
Filling the Void in SecOps Tools with Cloud Context
As organizations migrate to the cloud, traditional security operations tools like EDR, SIEM, and XDR often fall short, as they are not designed to address the unique challenges and threats of cloud-native environments. Fragmented data, knowledge gaps, and tools designed for legacy and hybrid rather than cloud-native operations create weak points in threat detection and response. In this session, Stream.Security’s Samuel Galicia, Senior Solutions Architect, will discuss how to bridge these gaps by integrating cloud context into SecOps workflows. Learn how enriching existing tools with cloud context can equip your SOC to effectively combat today’s evolving threats – all while maintaining your security workflow, without the need for extensive retraining.
During this session, you will learn:
- How cloud threats have significantly shifted today’s threat landscape, impacting modern security defenses
- Practical methods to complement your existing security stack with cloud-native context, adapting to the cloud threats
- How to integrate Cloud Detection & Response (CDR) seamlessly into your security workflows
Sponsored by

4:00 pm
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Panel Discussion
4:15 pm
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Ramona Ratiu
Cyber Security Operations | Head of Cyber Resilience Testing Program Zurich Insurance Company
5:15 pm