Chicago, IL
Thursday, January 25, 2024
Hybrid
































Join FutureCon CyberSecurity Events in Chicago!
This event is the perfect opportunity to discover cutting-edge security approaches and learn how to manage risk in the ever-changing cybersecurity world.
Keynote Speaker
“"The Groundhog’s Revenge"”
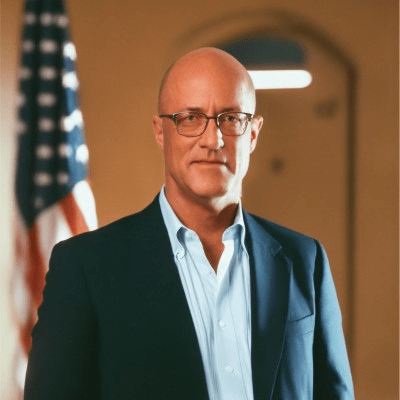
Robert LaMagna-Reiter
Vice President, Chief Information Security Officer WoodmenLife
Robert LaMagna-Reiter is a leading, trusted Information Security & Risk Management professional. As CISO for Hudl, Robert leads information security strategies and roadmaps; oversees risk management; strategy; architecture and engineering; regulatory compliance, privacy engineering and IT governance. Leveraging more than 18 years of expertise, Robert helps others deliver value through proper security strategy aligned to zero-trust principles. Robert’s experience includes leadership roles in information security for transportation, government communications, retail, e-commerce, managed services & SaaS industries. Robert also serves as Advisory Board President for SOFTwarfare, Zero Trust Initiative Leader for the CyberTheory Institute, and Zero Trust Expert Committee Member for the Cloud Security Alliance.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Robert LaMagna-Reiter
Vice President, Chief Information Security Officer WoodmenLife
Chris Cronin
Partner HALOCK Security Labs
MJ (Mark-John) McSheehy
Director of Information Security/CISO Addison Group
Katie Hanahan
Deputy CISO | Cybersecurity Strategist | Speaker | Board Member Ingredion Incorporated
Michael Myint
Senior Director Information Security COTA
Sponsors
Premier Platinum Sponsors

Platinum Sponsors


Gold Sponsors




Silver Sponsors
























Partner




About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Demonstrating Your Cybersecurity Program is Effective
Do your cybersecurity presentations leave Executives saying “Why do we need to do these projects” or “I don’t get it, do we need to spend this much”?
In this session, Dr. Glenn Stout, Ph.D. will provide a way to communicate to your Executives answering their questions of “Are we ok?”, and “If we are not ok, how do we get to ok?
Sponsored by

Presentation
Balancing Innovation and Risk in Today’s Ever-Expanding Technical Ecosystem
In today’s rapidly evolving business landscape, the expansion of our technical ecosystems pose both unprecedented opportunities and considerable challenges.
The proliferation of interconnected systems, emerging technologies, and the increasing interdependence among them have given rise to multifaceted system risks that organizations must navigate. These risks encompass cybersecurity threats, regulatory compliance (old and new), data privacy concerns, interoperability issues, and the potential for disruptive system failures.
Through collaborative insights and shared experiences, this discussion aims to equip the attendees with proven actionable strategies to include:
- Understanding the dynamic nature of these risks
- Aligning technological initiatives with overarching business objectives.
- Blending innovation with a comprehensive understanding of organizational goals and market demand
- Real world case studies highlighting successful alignment between business objectives and our InfoSec programs
Sponsored by

Sponsor Networking Time
Presentation
Today’s Threat Landscape Requires a Unique Capability
Specialized threats targeting OT environments have been around since at least 2010, with the reports of Stuxnet. Recognizing the criticality of these devices, Threat Actors have continued evolving, continuing to target OT devices, many of which are inherently insecure-by-design. Research, such as Vedere Labs’ OT:ICEFALL research project and Project Basecamp by Digital Bond from 10 years ago showed how significant the scope of vulnerable devices are that are pervasive in critical infrastructure systems. Today’s SOC needs to not only see those devices and the risks they pose while also ensuring accurate detection of the threats uniquely targeting those OT environments they’re deployed in. This session will explore this unique threat landscape and the capabilities required to combat the threats and automatically mitigate the risks specially targeting Operational Technology environments.
Sponsored by

Presentation
“Stack” Your Defenses Against Evolving TTPs
As more threats emerge and adversaries’ TTPs increasingly change, the ability to rapidly assess relevant coverage across the defensive stack becomes increasingly important.
As more threat reports & repositories now contain detections around recently observed indicators & behaviors (a positive trend), it’s tempting to think that deploying only those detections means successful implementation of “threat-informed defense”. However, our research suggests adversaries are evolving their tactics, techniques, & procedures with increasing frequency and in ways that specifically target parts of the attack surface that are especially challenging to defend.
Layering (and distributing) defensive capabilities against today’s threats is essential but making a quick assessment of coverage – that is both deep and wide – for each new threat is near-impossible if using traditional approaches. This talk will review recommendations for speeding up coverage assessments through threat & defensive prioritization, using two real examples as walkthroughs.
Sponsored by

Sponsor Networking Time
Lunch
Keynote
"The Groundhog’s Revenge"
Too many organizations have opted into the false narrative that with the right technology and outsourcing, sprinkled with a little artificial intelligence, they are buying down risk. Then it happens. The groundhog is back for revenge, and this time, artificial intelligence can’t help. We’ll dive into how adopting a strategy shift, known as zero trust, aligns with business’ strategic planning above all other methods. Leveraging the right mental accounting techniques and choice bracketing, we can embrace how to really make a difference.
Sponsor Networking Time
Presentation
Exploring the Ever Evolving E-crime Landscape
This presentation aims to tell the story of the dynamic landscape of cyber threats by delving into the Tactics, Techniques, and Procedures (TTPs) employed by cybercriminals, along with an exploration of the diverse file types used in these malicious activities. Some of these include:
- SVG files
- Use of WebDav
- Internet Shortcut (.URL) files
Based on Proofpoint’s telemetry of billions of messages per day, we show how Cybercriminals are are constantly trying old and new tricks in response to defenders. The presentation also illustrates how techniques are quickly identified by the security community to continue to keep our users safe from evolving threats.
Sponsored by

Presentation
Accelerate your identity and access security program in 2024
Sponsored by
Sponsor Networking TIme
Presentation
How ASPM Connects your AppSec Tools & Data to Manage Risk Holistically
With the increasing complexity of applications and rapid development, traditional approaches to AppSec struggle to keep up. Application Security Posture Management (ASPM) is the new future of managing risk holistically. With ASPM, organizations can efficiently manage their application risk posture, collaborate effectively between development and security teams, and enforce application security policies and controls. This talk will cover what ASPM is, what benefits it will bring to organizations, and how your security team can best prepare for it.
Sponsored by

Presentation
Moving Towards a ZeroTrust Mindset
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!