ShanShan is the Head of the AI & Data Governance practice at GlobalLogic, with a background in privacy, compliance, and risk. She has worked with clients across industries — including technology, healthcare, and financial services — to translate complex compliance requirements and regulations into tangible, workable governance strategies. She focuses on building practical guardrails that support innovation without losing sight of accountability. Before GL, she oversaw global privacy and compliance at Alibaba Cloud, where she managed the security and privacy compliance aspects of the cloud business.
Boston Cybersecurity Conference
Thursday, November 20, 2025
Hybrid
One Burlington Mall Road, Burlington, Massachusetts, USA, 01803




































Join Us in Boston for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
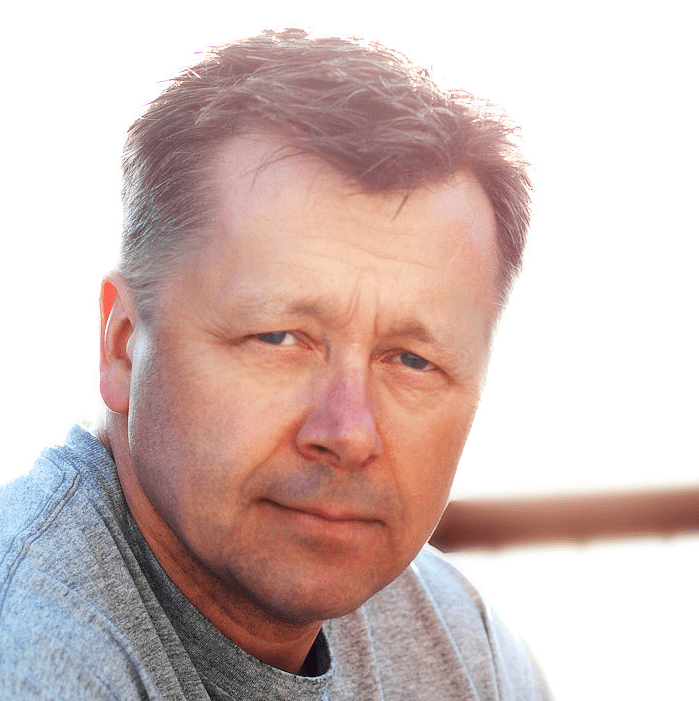
Keynote Speaker
“Rethink Intelligence: Building Smarter, Safer, and More Inclusive AI”
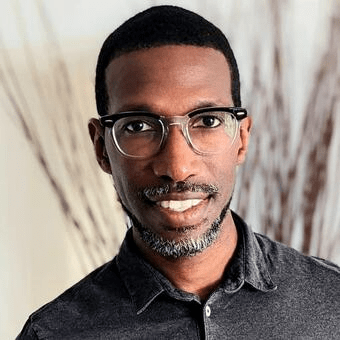
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Sponsors
Platinum Sponsors

Gold Sponsors






Silver Sponsors


























Partner





“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Cyber Defense Strategies For Earlier Detection and Faster Response
Sponsored by

Presentation
Rebuild Your Software Security Program from the Breach Up
Current security models are failing to keep up with the speed, complexity, and scale of modern software. Security professionals are doing their jobs—and yet, attacks still get through. In this session, hear the story of four people caught in the aftermath of a breach: a developer, a SecOps lead, an AppSec engineer, and a compliance officer. All working in good faith. All stuck in a broken system. This talk will introduce a new blueprint for modern software defense, modeled on the smartest of cities that have instrumented infrastructure to see, adapt, and respond in real time. Walk away with a prescriptive framework – based on context, coordination, and culture – that teams can use to stop guessing and start defending.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Securing the Future: Cyber Risk Insurance Essentials in an AI-Driven Digital Landscape
As AI reshapes the digital world, cyber threats are growing in scale and complexity. This session explores the essentials of cyber risk insurance—who’s at risk, why coverage matters, and how AI is transforming both the threat landscape and defense strategies. Learn how to leverage AI for proactive protection and how to safeguard your organization
Sponsored by

Presentation
The Great Vulnerability Boom: Outsmarting AI on Both Sides of the Keyboard
Organizations continue to struggle with the ever-growing influx of vulnerabilities introduced by developers each day. Despite years of investment, Application Security programs are still dominated by endless finding and triage, with far too little actual fixing—and almost no true prevention. The rise of AI-enhanced development has accelerated not only the speed of code delivery but also the frequency and complexity of vulnerabilities within that code. At the same time, attackers are arming themselves with AI to exploit weaknesses faster and inflict greater damage.
Unless we evolve our practices and build stronger partnerships with development teams, the gap between attackers and defenders will only widen, leading to even greater losses. This session will provide practical, actionable guidance to help security leaders stem the tide of vulnerabilities and empower developers to become their most effective defense against modern threats.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
Rethink Intelligence: Building Smarter, Safer, and More Inclusive AI
AI is everywhere, but clarity isn’t. In a time of hype and uncertainty, this keynote offers a new lens on what “intelligence” should mean for security and technology leaders. Instead of bigger models and bigger risks, we’ll explore quieter truths: how systems learn, how they reason, how they fail, and how people remain essential. This is a perspective-shifting session that challenges assumptions and leaves you rethinking not just AI—but what we expect from intelligence itself.
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Today’s Threat Landscape
The cybersecurity threat landscape has grown more sophisticated and relentless than ever, marked by surging ransomware volumes, widespread identity-centric attacks, supply-chain compromises, and the rapid integration of generative AI into attacker toolkits. Analysis of major incidents throughout the year, corroborated by leading industry reports, reveals a consistent pattern: once initial access is gained, threat actors exploit flat or poorly segmented environments to achieve lateral movement at unprecedented speed, often reaching critical assets in hours or minutes.
A defining factor in nearly every large-scale breach was the lack of granular, enforceable segmentation across hybrid IT, OT, IoT, and cloud environments. Real-world cases demonstrate that comprehensive asset visibility and policy enforcement—capabilities exemplified by platforms like Forescout—repeatedly proved decisive in detecting anomalous movement, blocking lateral traversal, and containing damage before encryption or exfiltration could occur.
This session combines 2025 threat landscape statistics, newly observed breach tactics, and concrete examples of segmentation done right to illustrate why modern, identity- and asset-aware segmentation has become the cornerstone control for limiting blast radius and maintaining resilience in today’s environment.
Sponsored by

Presentation
AD Security and Recovery: Questions That Need Answers
In today’s threat landscape, attackers prioritize identity and access management systems like Microsoft’s Active Directory (AD) because they hold the keys to the kingdom in most enterprises. In other words, compromise AD, and you control the organization. That’s why modern cyber resilience strategies must focus on AD hardening, monitoring, and recovery planning.
During this session, you’ll learn how organizations can better prepare, respond, and recover when disaster strikes. And we’ll discuss the questions that need answers to get you back online quickly and offer actionable guidance for building operational resilience.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
How to Get Away with Cybercrime
We often talk about threats in terms of dollars lost, data stolen, or headlines made. But the real threat lives deeper—in the structure, the strategy, and the growing ambition of the actors behind the screen. Today’s cybercriminals don’t just encrypt files; they build economies, launder, influence, and forge alliances that stretch across borders and industries. In this talk, we’ll peel back the layers of modern cybercrime and explore how loosely affiliated hackers have evolved into organized syndicates. These groups operate more like multinational corporations than rogue disruptors—complete with HR departments, recruitment pipelines, insider relationships, and state protections.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!