Boston, MA (Eastern Region)
Wednesday, March 31, 2021
Virtual
Keynote Speaker
“Practical Security in an Impractical World”
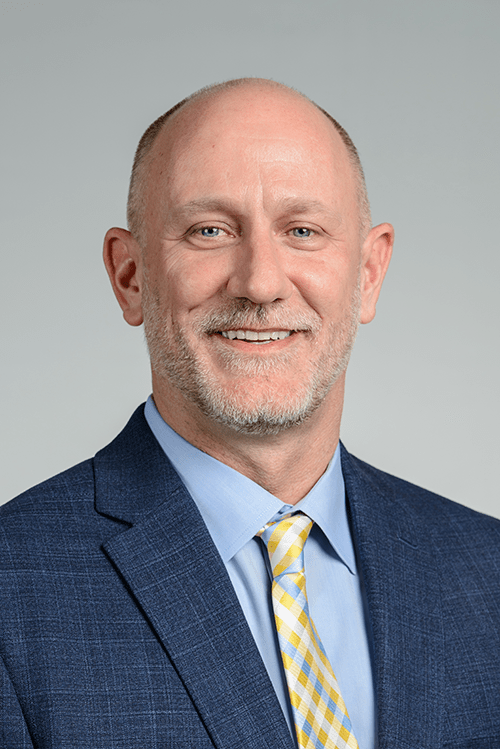
Rex Tolman
Chief Information Security Officer, VP Information Security Kforce
CISO/Industry Leader Panel
"Privacy and the future of compliance and other issues of the New digital workforce"
Rebecca Herold
The Privacy Professor CEO, Privacy & Security Brainiacs | Expert Witness & Author
George Viegas
Chief Information Security Officer (CISO) and Privacy Champion Chapman University
Jyotin Gambhir
CISO/CIO, Security/Privacy SecureFLO
Ken Dawson
Chief Information Officer & Chief Information Security Officer ClearStar
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Live
Opening Introductions
Networking
Sponsor Booth Networking Time
Presentation
Artificial Intelligence (AI) in Cybersecurity Present and Future Role
Have you ever wondered about Artificial Intelligence (AI) in Cybersecurity? Maybe you are curious to know how it is currently being applied or how it might be applied in the future? Better yet, how AI relates to the current threat landscape and even your environment. If so, join us! Where we will break it all down and more. This is a zero to hero session so you don’t need a PhD in math or data science to enjoy the topic and learn something new.
Sponsored by
Live Presentation
Zero Trust: Getting Least Privilege Right, Finally
The more the traditional perimeter blurs or dissolves, the more zero trust comes into focus. At its core, zero trust aspires to eliminate persistent trust, and enforce continuous authentication, least privilege, and microsegmentation. This approach reduces the threat surface and also minimizes the threat windows during which attackers can inflict damage, helping to protect against everything from simple malware to advanced persistent threats.
The reality is, for most organizations, achieving a 100% zero-trust state is a pipe dream. However, any implementation of zero trust controls should substantively help minimize your attack surface and cyber risk. Understanding your barriers to zero trust will also help you forge the best path to optimally securing your environment, including upgrading from legacy applications and architectures to ones that support zero trust.
In this session we’ll explore:
· What zero trust is and how NIST defines it
· The goals of zero trust
· Roadblocks to zero trust (legacy architectures and technologies)
· How Privileged Access Management aligns with and enables zero trust
If you’re ready to cut through zero trust myths and clearly grasp what it will take for you to improve zero trust security controls, and how your organization stands to benefit, don’t miss this session!
Sponsored by

Live Keynote
Practical Security in an Impractical World
Presentation
Your Ransomware Hostage Rescue Guide
Ransomware attacks are on the rise and are estimated to cost global organizations $20 billion. As ransomware attacks become more targeted and more damaging, your organization faces increased risk that can leave your networks down for days or even weeks. So, how can your organization avoid getting held hostage?
Join Erich Kron CISSP, Security Awareness Advocate at KnowBe4, as he looks at concerning features of new ransomware strains, provides actionable info that you need to prevent infections, and gives you tips on what to do when you are hit with ransomware.
In this webcast we will cover:
- What new scary ransomware strains are in the wild
- Am I infected?
- I’m infected, now what?
- Proven methods of protecting your organization
- How to create your human firewall
Don’t get held hostage by ransomware and become a statistic!
Sponsored by

Live Panel Discussion
"Privacy and the future of compliance and other issues of the New digital workforce"
Rebecca Herold
The Privacy Professor CEO, Privacy & Security Brainiacs | Expert Witness & Author
Presentation
Faking It: Stopping Impersonation Attacks with Cyber AI
Today, 94% of cyber-threats still originate in the inbox. ‘Impersonation attacks’ are on the rise, as artificial intelligence is increasingly being used to automatically generate spear-phishing emails, or ‘digital fakes’, that expertly mimic the writing style of trusted contacts and colleagues.
Humans can no longer distinguish real from fake on their own – businesses are increasingly turning to AI to distinguish friend from foe and fight back with autonomous response.
In an era when thousands of documents can be encrypted in minutes, ‘immune system’ technology takes action in seconds – stopping cyber-threats before damage is done.
Find out how in this session.
Sponsored by
Presentation
Making the Case for Authentication as a Platform
As organizations adopt advanced authentication practices, it’s critical to consider the varied modalities your organization requires. The “solution” should not be one that’s built from a collection of point solutions. For this reason, many businesses are turning to authentication solutions that are built as a platform. This holistic solution is accommodating to different modalities, applications and form factors. It can also control the authentication and credential management lifecycle. In this session, the experts from HID® Global will:
- Address the most common challenges and concerns for enterprise organizations attempting to streamline authentication
- Detail the intricacies of the authentication lifecycle
- Help you identify what to look for in an authentication platform that meets your organization’s needs
Sponsored by
Presentation
Making Zero Trust Real
Sponsored by
Presentation
Extortionware: Your Privacy Problems Made Public
Sponsored by

Presentation
Stay Ahead of the Hacker with Continuous Security Testing
Join Sion Retzkin, CISO & Head of Knowledge & Practice, Pcysys to learn how to:
-
Build up your cyber resilience with continuous risk validation
-
Prioritize remediation efforts with a threat-facing perspective
-
Increase the productivity of your security teams
Sponsored by

Presentation
Identity Cloud Checklist
Sponsored by

Presentation
Making the SOC more effective by enabling automation with better data
SOAR has been pitched to the industry as a way to resolve alert fatigue by automating common analyst workflows. Experience shows, however, that automation is only as good as the data that underlies it – so many people avoid SOAR, because of the complexity of getting “ready” for it. This talk will discuss open source Zeek as an approach for simplifying the acquisition of network data that’s directly applicable to SOAR, and the application of it through open source playbooks being released by Corelight.
Sponsored by