Baltimore Cybersecurity Conference
Thursday, February 12, 2026
Hybrid
1743 West Nursery Road, Linthicum Heights, Maryland, USA, 21090






















Join Us in Baltimore for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
Keynote Speaker
“The Dual-Use Dilemma: AI as Defender and Adversary”
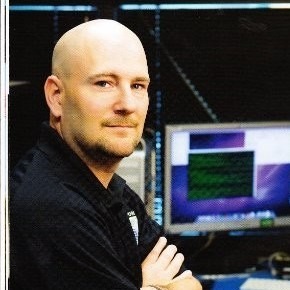
Roy Luongo
Chief Information Security Officer U.S. Secret Service
I help organizations turn cybersecurity into a strategic business capability—one that protects enterprise value, enables growth, and earns the confidence of boards, regulators, and customers.
I’m a senior cybersecurity executive with nearly three decades of experience leading cyber operations and enterprise security programs across national security, financial services, and highly regulated environments. My background includes the NSA, U.S. Cyber Command, JPMorgan Chase, and service as Chief Information Security Officer for the United States Secret Service. I’ve led both large-scale defensive security programs and offensive red team operations, bringing an adversary-informed perspective to enterprise risk.
I translate cyber risk into decision-ready business terms for boards and C-suite leaders, aligning security with enterprise risk, resilience, and regulatory compliance. I build and scale cybersecurity programs that protect complex organizations while enabling digital transformation and cloud adoption. My experience in maturing SOC operations, incident response capabilities, and threat intelligence programs has proven essential in detecting and disrupting nation-state and financially motivated adversaries.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Nish Majmudar
Head of Cybersecurity Architecture and Engineering BlueCross BlueShield Association
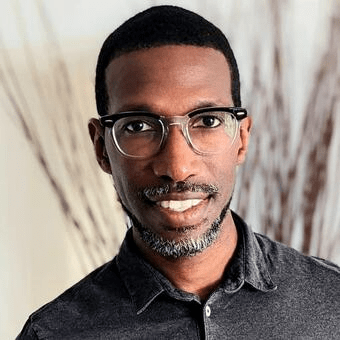
Abiola Olamoyegun
VP, Information Technology IA PHEAA
Christopher Carter
Chief Information Security Officer V2X Inc
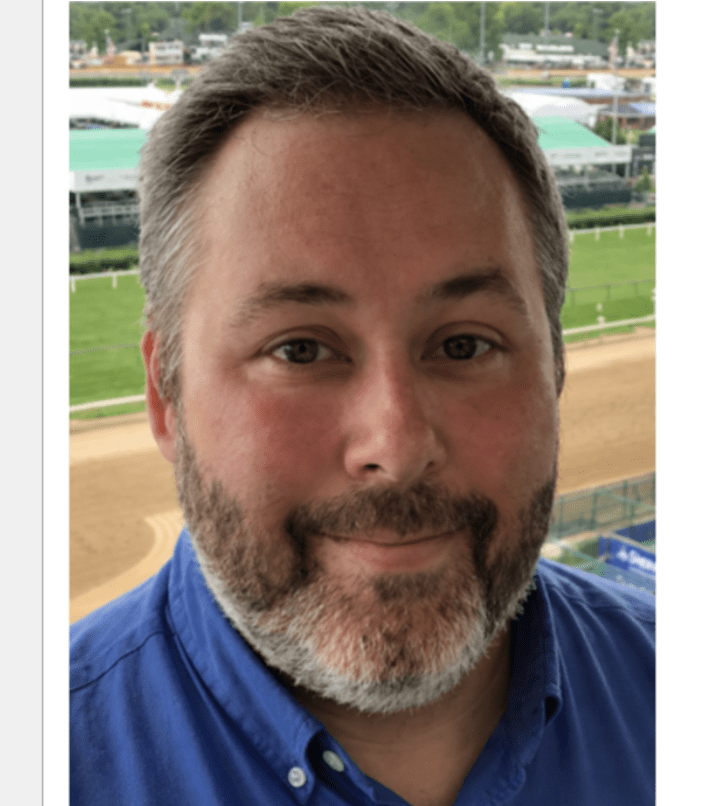
Rich Schnell
Deputy CIO Maryland Department of Transportation
Chris Houseknecht
Chief Information Security Officer Comptroller of Maryland
Sponsors
Gold Sponsors









Silver Sponsors











Partner




“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
Rebuild Your Software Security Program from the Breach Up
Sponsored by

Presentation
The 2026 Attackers Playbook: Hacking Trust
Attackers aren’t breaking in anymore — they’re logging in. Join Varonis security experts as they break down the 2026 Attacker’s Playbook and reveal how modern adversaries use AI, trusted tools, and misconfigurations to move through your environment undetected. In this fast‑paced session, you’ll walk away with clear insights into how attackers actually operate today — the tools they abuse, the trust relationships they exploit, and the misconfigurations that quietly open the door for them. You’ll leave with practical guidance you can bring back to your team to strengthen defenses and stay ahead of the 2026 threat landscape.
Sponsored by

Presentation
AI-generated code: Maximize gains, minimize risks
AI coding assistants promise massive productivity gains, but recent academic research shows they also introduce instability, security weaknesses, and developer overconfidence. In this talk, I present data from large-scale studies demonstrating how AI-generated code affects delivery performance, vulnerability rates, and developer decision-making. I then outline a practical, end-to-end approach for reducing AI-induced risk while preserving the benefits of AI-assisted development.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
But Our Identity Lives in the Cloud: Understanding Why Cloud Identity Is Easy to Run — and Hard to Recover
Cloud identity platforms make authentication and access seamless, but recovery is far more complex than most organizations realize. This session explores why AD, Entra ID, and cloud IDPs cannot fully restore identity state, relationships, and cloud-native objects after incidents. Attendees will learn what actually breaks—and what must be rebuilt—across tenants, SaaS integrations, and MFA during identity recovery.
Sponsored by

Presentation
The End of Legacy Network Security
The End of Legacy Network Security, by Todd Ellison, argues for replacing layered, box‑centric designs with outcome‑driven networks where security is native. It champions “security built‑in, not bolted on” via native Zero Trust at the access layer, per‑device isolation to stop lateral movement, and an integrated, cloud‑driven architecture that operates at “cloud speed,” replacing brittle VLAN/ACL/NAC stacks with an identity‑aware fabric that’s continuously current, observable, and assured.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
The Dual-Use Dilemma: AI as Defender and Adversary
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Guarding Tomorrow: AI’s Edge in Security Ops
This presentation dives into how AI’s transforming security operations today and shaping cybersecurity’s future. We’ll explore real-world roles like threat detection, automated responses, and predictive analytics, plus insights on booming AI stocks driving these innovations—like key players in the sector and their impact on the market.
Sponsored by

Presentation
Beyond the Dashboard: Translating 2026 Cyber Risks into Boardroom ROI
In 2026, the gap between technical security metrics and executive business value is wider than ever. Security leaders must move beyond the fatigue of “threat-based” reporting toward a strategy of Proactive Value. This session introduces a Business Value Assessment (BVA) framework that quantifies the financial impact of solving security issues, reduces organizational liability, and amplifies the performance of infrastructure teams without increasing technical debt. Learn how to translate complex AI-driven threat data into a narrative of operational excellence and Board-ready ROI.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Generative and Agentic AI: How They’re Reshaping Data Risk
Generative and agentic AI are reshaping how data is created, accessed, and distributed across modern environments. As autonomous agents interact with systems and collaborate with users, they introduce new pathways for sensitive-data exposure, privilege expansion, and uncontrolled data propagation.
In this session, we’ll cover:
- How these AI capabilities alter data-risk models and challenge existing governance frameworks
- Key security considerations, including prompt-based data leakage, agent autonomy, monitoring AI-driven workflows, and protecting data used as model inputs
- Practical guidance to support the secure, responsible adoption of generative and agentic AI
Sponsored by

Presentation
How to Get Away with Cybercrime
We often talk about threats in terms of dollars lost, data stolen, or headlines made. But the real threat lives deeper—in the structure, the strategy, and the growing ambition of the actors behind the screen. Today’s cybercriminals don’t just encrypt files; they build economies, launder, influence, and forge alliances that stretch across borders and industries. In this talk, we’ll peel back the layers of modern cybercrime and explore how loosely affiliated hackers have evolved into organized syndicates. These groups operate more like multinational corporations than rogue disruptors—complete with HR departments, recruitment pipelines, insider relationships, and state protections.
Sponsored by

Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!