Atlanta (Eastern Region)
Wednesday, December 15, 2021
Hybrid
Keynote Speaker
“"The Modern CISO"”
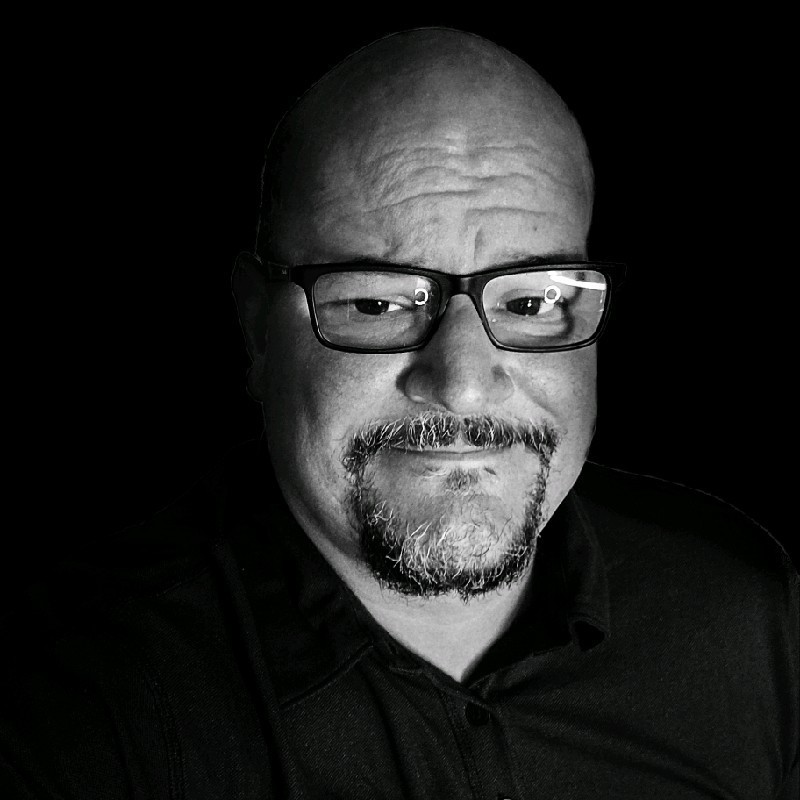
James Azar
CISO, Artera Host of The CyberHub Podcast, CISO Talk
CISO/Industry Leader Panel
"Diving into LOG 4J Hack"
James Azar
CISO, Artera Host of The CyberHub Podcast, CISO Talk
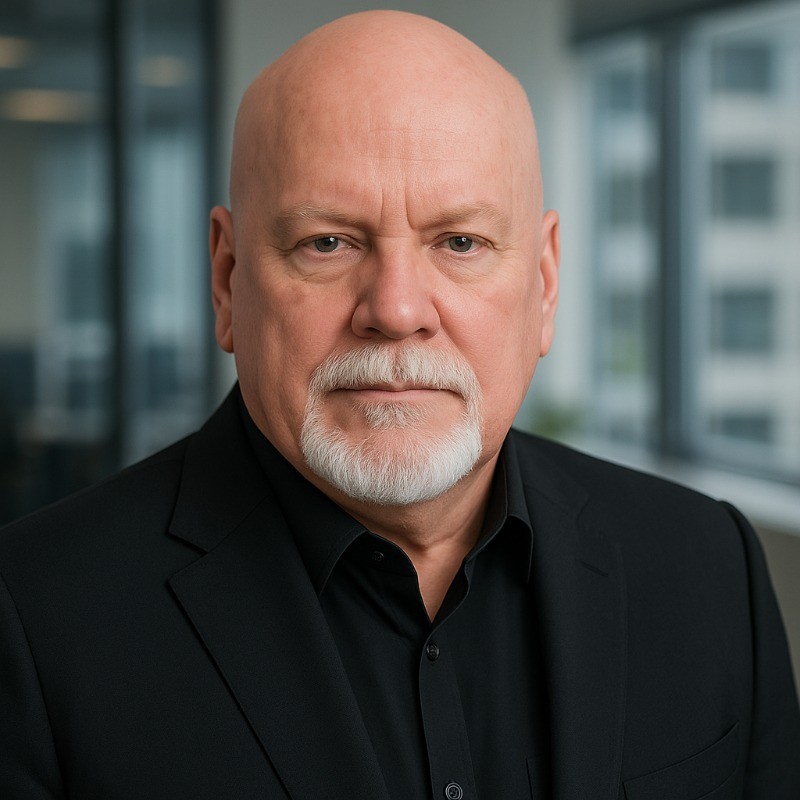
Derek Johnson
Atlanta Infragard Board Member Cybersecurity and Technology Transformative Leader | CISO | CIO | Susan G. Komen
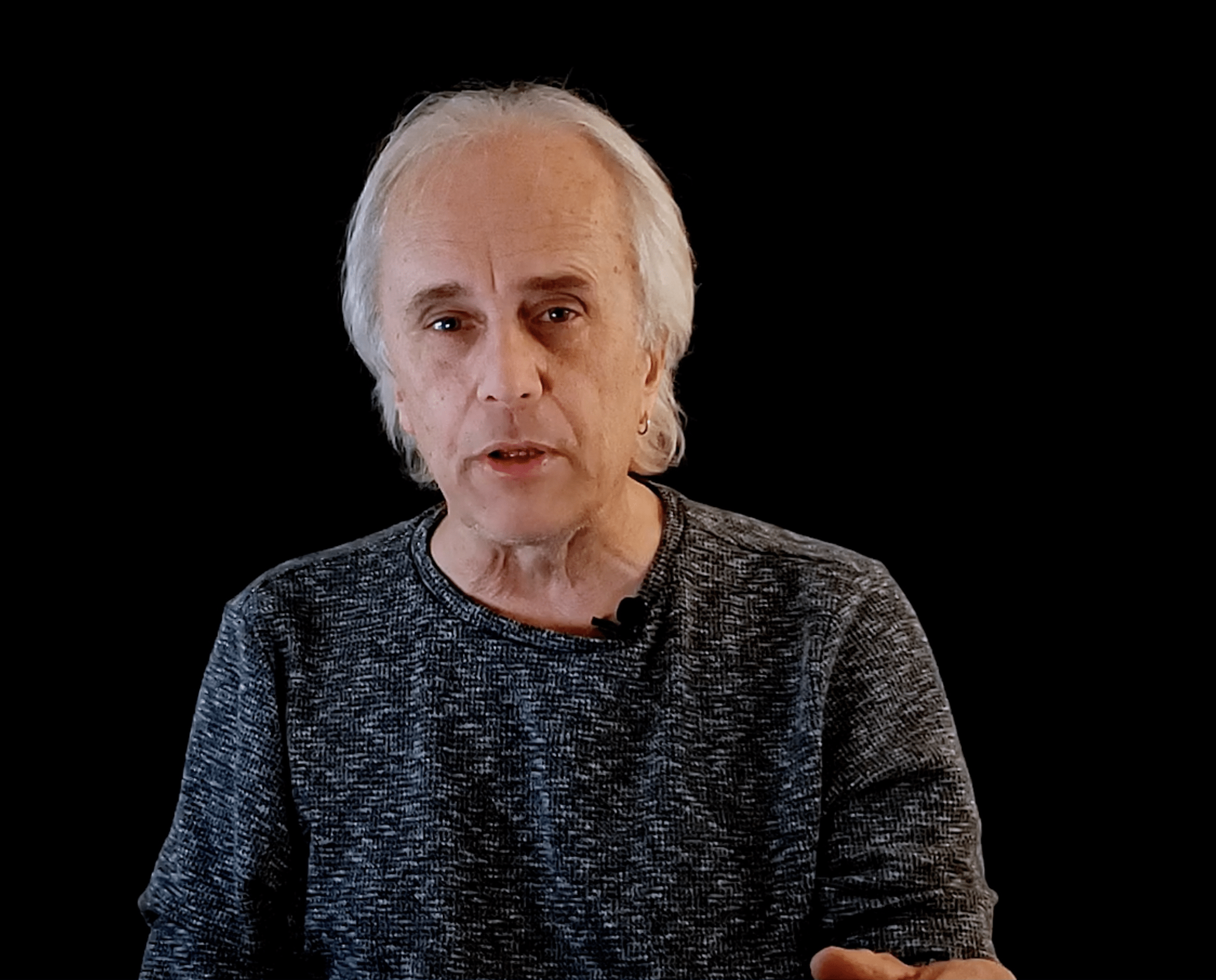
Daniel Sergile
CISO | vCISO Unit 42 by Palo Alto Networks
Wes Knight
Chief Information Security Officer Needling Worldwide
Klint Walker
Cyber Security Advisor U.S. Department of Homeland Security
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Opening Introductions | Check In
Presentation
Securing Trust - How The Security Leader Enables Business Outcomes
Sponsored by

Presentation
CIS Controls in the Real World
As a vendor, we witness first-hand the tangible effect that best practices like the CIS Controls have on our customers’ network security. From our perspective, it’s easy to see who is on top of their security game … and who could really benefit from the guidance these controls provide. In this discussion, we’ll walk through several of the CIS Controls, review the changes to the new V8, and provide real-world case studies to illustrate how different security tools and services can work together – sometimes in not-so-obvious ways – to reduce risk, and keep your network safe and secure.
Sponsored by

Rise of Secure Access Service Edge (SASE)
Secure access service edge has quickly emerged as a hot topic in cybersecurity, but what exactly does it mean and why should organizations care? As cloud migration, BYOD adoption, and remote work have skyrocketed in prevalence, it has become increasingly apparent that organizations need to think differently about security. While legacy tools like firewalls are no longer equipped to handle the modern IT ecosystem, SASE platforms like Bitglass are built for this exact moment. In this presentation, you will learn:
- The core components of a SASE platform like Bitglass.
- The functionality you need to secure cloud, web, and remote access use cases. Architectural considerations you should keep in mind when comparing SASE vendors.
Sponsored by

Presentation
Stopping Ransomware with Autonomous Response
New strains of ransomware are leaving organizations vulnerable – too often, security teams lack the ability to respond proportionately to an attack, leading to cyber disruption across the organization. Join this session to unpack some of today’s most advanced ransomware threats. Learn how Self-Learning AI understands the organization to reveal every stage of a ransomware attack – and takes targeted, autonomous action to stop the threat in its tracks.
This presentation will discuss:
- Recent ransomware threat trends, including double extortion and RDP attacks
- How Autonomous Response takes action to contain an emerging attack, even when security teams are out of office
- Real-world examples of ransomware detected by Darktrace AI – including a zero-day and an attack initiated on Christmas Day
Sponsored by
Presentation
Crawl, Walk, Run Your Segmentation Approach
Sponsored by

Lunch
Presentation
2022 Cybersecurity Predictions: The New Tools, Dynamic Attacks, and Talent Challenges that Await
Sponsored by

Presentation
Winning Against Ransomware
Sponsored by

Keynote
"The Modern CISO"
Hiding IT security in the basement is so 2018, in 2021 and beyond the role of the CISO has been elevated changing the entire job description of CISO. We are no longer firewall experts…
The modern CISO has to have a lot more skills than security, in this talk we review the skills, knowledge and thinking of the CISO and what is it going to take to be a CISO in 2022 and beyond.
Key Takeaways:
Industry trends for CISO
The board’s view of the CISO
Knowledge gaps for the CISO in 2022.
Presentation
Is your defensive stack ready for a targeted attack?
Sponsored by

Presentation
Preventing Cyber Catastrophe: How Security Leaders Can Craft Stronger Roadmaps to Secure Budget, Resources, and Executive Buy-In
The spread of ransomware is an existential threat to public and private sector organizations and security and risk leaders face an often-impossible task of securing limited resources, executive buy-in, and organizational support for cyber programs and initiatives. In this session, we will explore how you can better craft your cybersecurity roadmap, quantify your cyber risk in dollars, and gain a better understanding of what cyber controls – and vendors – you should be prioritizing.
Sponsored by

Detecting and Responding to Threats at the Speed of Business
- Reduce MTTD and MTTR with context-driven investigations.
- Proactively hunt for threats while overcoming the security skills shortage.
- Ensure your security tech stack is working for you, not against you.
- Take a “threat-centric” approach to decrease caseload by as much as 80%.
Sponsored by