Atlanta Cybersecurity Conference
Wednesday, December 11, 2024
Atlanta Marriott Buckhead Hotel & Conference Center
Hybrid




































Join Us in Atlanta for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Don’t miss our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
Join us live for breakfast, lunch, and a wrap up cocktail happy hour!
![]()
![]()
Keynote Speaker
“Challenges and Successes: Building an AI Governance Program”
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
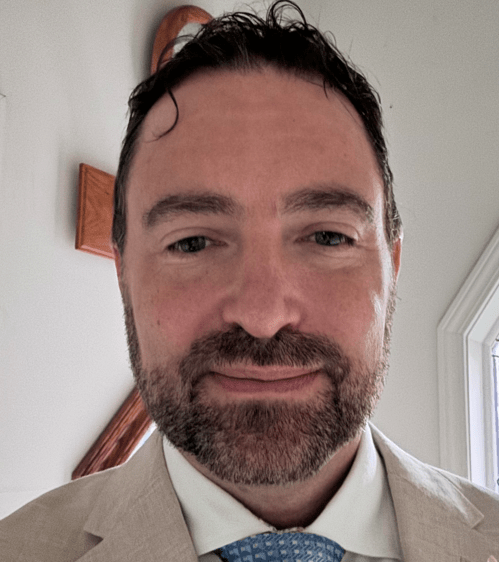
Marc Johnson
CISO / Director / vCISO / vCIO Impact Advisors
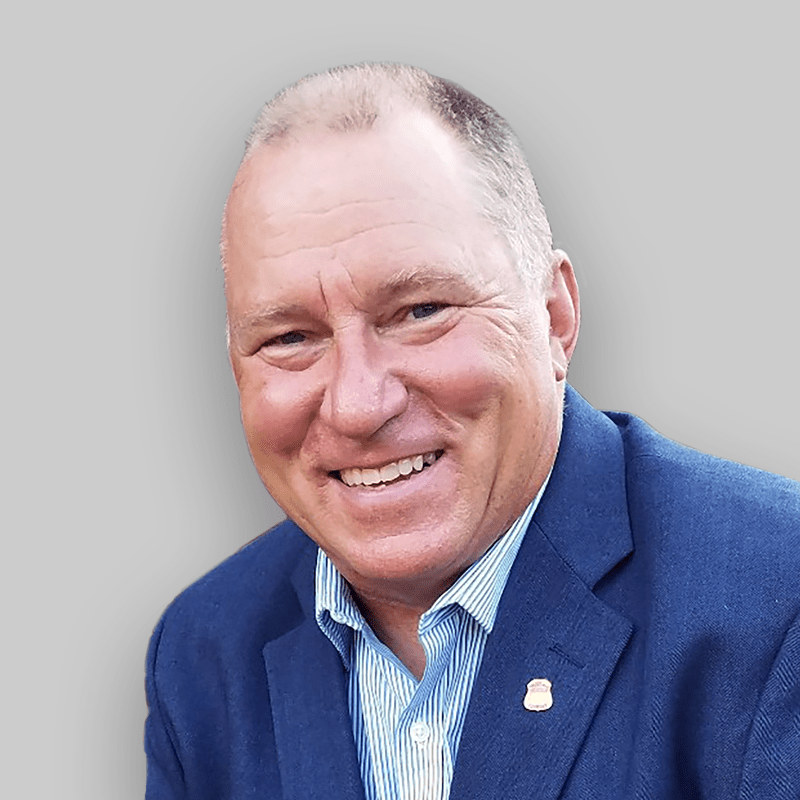
Kenneth Foster
CISO, Cybersecurity, Architecture, and Compliance Expert
Tera Ladner
Deputy Global CISO Aflac
Luis Valenzuela
Director, Data Governance and Data Loss Prevention InComm Payments
Tamika Bass
Cybersecurity Director at Gannett Fleming CISA, Network Security
Sponsors
Premier Platinum Sponsors

Platinum Sponsors

Gold Sponsors





Silver Sponsors





























Partner





“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
Atlanta Marriott Buckhead Hotel & Conference Center
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
2024 Ransomware Impact, Protection, and Recovery
In 2024, ransomware attacks have evolved, presenting new challenges for IT security engineers and professionals. This presentation delves into the latest trends and developments in ransomware, exploring sophisticated attack vectors, the rise of double extortion tactics, and the increasing targeting of critical infrastructure and cloud environments. We will also discuss the importance of proactive threat hunting, incident response planning, and cross-industry collaboration to stay ahead of these ever-evolving threats.
Sponsored by

Presentation
Securing Your Revenue Stream: Protecting Applications and APIs from Bot Threats
With automation changing the landscape, global cyber losses attributable to bot attacks now average between $68-$116B annually. We will examine data from the Imperva Threat Research team to investigate the scope of the challenge, review real-world examples and provide practical steps you can take to prepare for the inevitable security incident.
Sponsored by
Sponsor Networking Time
Presentation
Ransomware: A Security Reference Architecture
We will dive into the increasing threat posed by ransomware and why it’s critical to address this challenge head-on. Myriad360 will explain the value of a Reference Architecture in building a strong defense against these attacks. They will also explore how ransomware tactics are continuously evolving, requiring organizations to stay agile in their security approach. Lastly, they touch on other key factors that should be considered when planning a comprehensive cybersecurity strategy to protect against ransomware and other threats.
Sponsored by

Extortion and Exfiltration: The New Age of Ransomware
- Ransomware trends and insights
- The rise of exfiltration and extortion
- The importance of integrating new technologies into cybersecurity stacks including anti data exfiltration technology
- How to build comprehensive cybersecurity defenses
Sponsored by

Sponsor Networking Time
Lunch
Keynote
Challenges and Successes: Building an AI Governance Program
Sponsor Networking Time
Presentation
Beyond SIEMs, TIPs, and Feeds: Threat Intelligence as a Strategic Tool
Threat intelligence has become the latest requirement for organizations looking to bolster their security practices. Buy a feed or three, suck them into your SIEM, automate blocking IOCs, and check the box. And in many ways, that addresses a sizable chunk of the tactical and operational value of threat intel. However, a growing number of organizations are realizing that threat intel can also inform strategy: how and why we train our users, where we should be investing our security resources, and what kinds of conversations executive leadership should actually be having to avoid becoming the latest cautionary tale used to sell more feeds. Join Proofpoint to learn about the increasingly strategic role of threat intelligence modern businesses.
Sponsored by

Presentation
The State of Application Security & Protecting against Automated threats
Sponsored by

Sponsor Networking Time
Presentation
Accelerate AI innovation Securely
As organizations increasingly migrate to the cloud, the landscape of cybersecurity is evolving at a rapid pace. The advent of Artificial Intelligence (AI) brings both unprecedented opportunities and challenges, making it imperative for cloud security strategies to advance accordingly. Join this session to hear from Wiz why organizations are adopting AI-SPM (AI- Security Posture Management) into their CNAPP strategy and how you can effectively secure AI workloads in the cloud while accelerating AI innovation securely.
Sponsored by

Presentation
Sponsored by