Kansas City Cybersecurity Conference
Thursday, June 6, 2024
Live
























Join Us in Kansas City for the Futurecon Cybersecurity Event!
Hear from our esteemed speakers while gaining up to 10 CPE credits. Immerse yourself in the latest cybersecurity developments to gain valuable insights in today’s dynamic threat landscape. Learn how to effectively manage risk, demo the newest technologies from an array of different sponsors, and network with your local community.
Join us live for breakfast, lunch, and a wrap up cocktail happy hour! Stay until the end for our special ceremony recognizing our honorary attendees receiving an Award of Excellence!
![]()
![]()
Keynote Speaker
“Shadows of the Digital Realm: The Dark Side of Information”
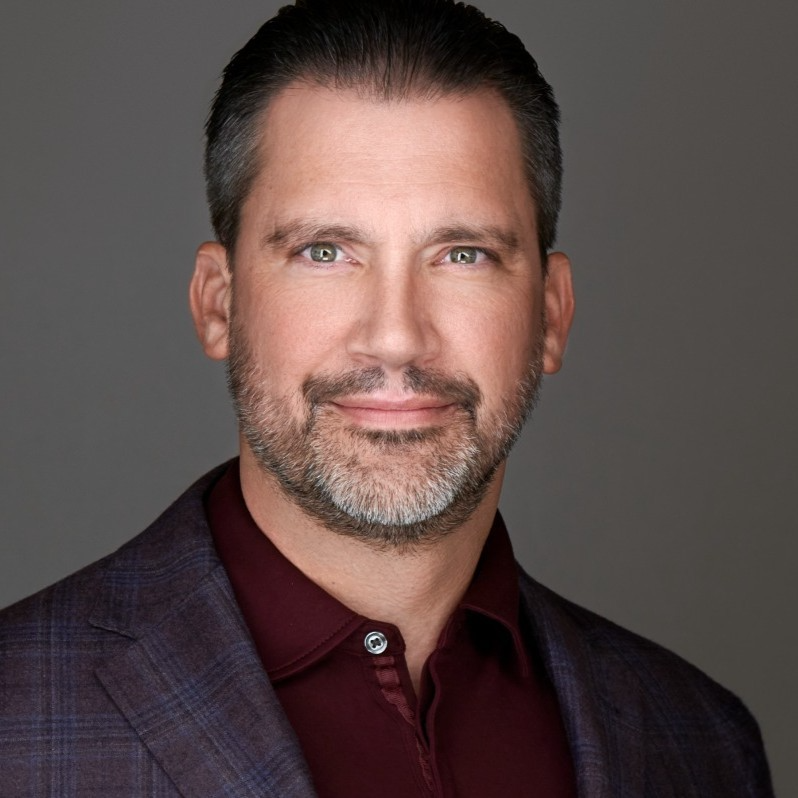
John Godfrey
Chief Information Security Officer Kansas Information Security Office
A seasoned cybersecurity executive and entrepreneurial dynamo with 18 years of rich experience, I excel in delivering cutting-edge technology and information security strategies. I have a knack for transforming organizations through modern digital solutions, spurring business enablement, and fostering talent elevation. My unique blend of action-oriented leadership and influential communication has consistently steered executives and boards through periods of organizational metamorphosis.
My ability to demystify complex technology and make it comprehensible is one of my key strengths. Known for my fervor and transformative leadership, I’ve graced numerous local and national conferences as a speaker, moderated sessions, featured as a podcast guest, and contributed articles to various magazines and publications.
Presently, I hold a pivotal role as a board member and advisor to boards of directors. I am actively engaged with the information security community, holding memberships in premier organizations like ISC2, ISSA, ISACA, InfraGard, and more. My academic arsenal boasts of several industry certifications, and I am currently pursuing my Doctorate in Cybersecurity with a focus on executive leadership.
Outside of work, I relish time with my family and friends, love touring vineyards, and traveling. I am passionate about giving back to the community and also run my own real estate investment business.
CISO/Industry Leader Panel
"Securing the Future: CISO Insights and Industry Leaders Discussing Current Cyber Threats and Strategic Defense Practices"
Kurt Manske
Partner, Information Assurance and Cybersecurity Cherry Bekaert
Alexandra Munk
Senior Product Manager Microsoft
John Godfrey
Chief Information Security Officer Kansas Information Security Office
Nick Gicinto
Chief Information Security Officer William Jewell College
Britney Kennedy
Global BISO & Business Partnership Cardinal Health
Sponsors
Premier Platinum Sponsors


Gold Sponsors







Silver Sponsors












Partner




“Cybersecurity is no longer just an IT problem”

FutureCon Events brings high-level Cyber Security Training to C-suite executives and CISOs (chief information security officers).
Join us for a day with multiple illuminating presentations and a panel discussion featuring C-level executives who have effectively mitigated the risk of Cyber Attacks, demo the newest technology, and discover the cutting-edge security approaches to prepare you for the future of the Cyber World.
You will gain the latest knowledge you need to enable applications while keeping your computing environment secure from even the most advanced Cyber Threats. Interact with the world’s security leaders and your peers to gather details on other pressing topics of interest to the information security community.

Have questions? Check out the FAQ.
The Venue in Leawood
Agenda
Times are subject to change
Opening Introductions | Check In | Networking
Presentation
State of Security and Compliance 2024
Tenax Solutions will be discussing the key security drivers that are expected to be prevalent in 2024, highlighting their commonalities as well as the significant challenges that prevent organizations from being compliant and secure. The session will also cover how to improve your compliance and security programs. Additionally, we will delve into the most common technical security issues and provide insights on how to remediate them.
Sponsored by

Presentation
AI-Infused MXDR and the Autonomous SOC
MXDR helps organizations detect and respond to cyber-attacks before the attacker’s objective is completed. This presentation will cover:
- What is ‘getting left of bang’?
- Why is it so hard? •
- How MXDR makes it easy
- Customer use cases
- 2023: Findings from 35,000 Customer SitReps
- How AI will drive the “Autonomous SOC”
Our presentation will show how MXDR compresses mean-time-to-detect and mean-time-to-respond at the lowest possible cost, and how AI will soon collapse all three.
Sponsored by
Networking
Sponsor Networking Time
Presentation
Not Your Father’s Firewall: Open Source Security Layers for Kubernetes, Using Zero Trust
Sponsored by


Presentation
The Executive Guide to Red Team Testing
Red teaming is a proven methodology for identifying vulnerabilities and improving organizational resilience. However, organizations often misunderstand red teaming, resulting in suboptimal outcomes. This talk will provide an executive guide to red teaming to demystify this powerful technique and equip leaders with the knowledge and tools to leverage it effectively.
We will begin by clarifying the meaning of red teaming and outlining what it involves and doesn’t. We will delve into the various components that make up red teaming, encompassing activities such as penetration testing, physical security testing, and adversarial simulations, and analyze the circumstances in which each is most suitable. Also, we will underscore the importance of setting up defined goals, properly scoping the project, and choosing the best team members.
Last but not least, we will tackle the cultural and organizational factors that can influence the outcome of red teaming. We will focus on fostering a culture of ongoing enhancement and employing red teaming to stimulate innovation and strategic planning. Furthermore, we will emphasize the significance of creating an environment of confidence and openness with relevant parties while ensuring seamless integration of red teaming into broader risk management applications.
Sponsored by

Sponsor Networking Time
Lunch
Keynote
Shadows of the Digital Realm: The Dark Side of Information
Journey into the shadows of the digital realm to uncover the dangers of deepfakes and disinformation. This session will highlight real-world examples, delve into the technology behind these threats, and discuss the measures needed to defend against them
Sponsor Networking Time
Presentation
Beyond SIEMs, TIPs, and Feeds: Threat Intelligence as a Strategic Tool
Threat intelligence has become the latest requirement for organizations looking to bolster their security practices. Buy a feed or three, suck them into your SIEM, automate blocking IOCs, and check the box. And in many ways, that addresses a sizable chunk of the tactical and operational value of threat intel. However, a growing number of organizations are realizing that threat intel can also inform strategy: how and why we train our users, where we should be investing our security resources, and what kinds of conversations executive leadership should actually be having to avoid becoming the latest cautionary tale used to sell more feeds. Join Proofpoint to learn about the increasingly strategic role of threat intelligence modern businesses.
Sponsored by

Presentation
Accelerate AI innovation Securely
As organizations increasingly migrate to the cloud, the landscape of cybersecurity is evolving at a rapid pace. The advent of Artificial Intelligence (AI) brings both unprecedented opportunities and challenges, making it imperative for cloud security strategies to advance accordingly. Join this session to hear from Wiz why organizations are adopting AI-SPM (AI- Security Posture Management) into their CNAPP strategy and how you can effectively secure AI workloads in the cloud while accelerating AI innovation securely.
Sponsored by

Sponsor Networking Time
Presentation
AI is shaping our future
Sponsored by

Operationalizing Cyber Threat Intelligence To Optimize Your Defenses
Operationalizing threat intelligence, aligning an organization’s security posture to the threats that are most likely to target them, is often easier said than done. It is a manual and tedious process to take information from a threat intelligence source and convert it into actionable, realized defenses. This talk will focus on the difficulty security teams face in using Commercial Threat Intelligence and making it actionable.
Sponsored by