Baltimore | Washington D.C.
Wednesday, March 30, 2022
Hybrid
Keynote Speaker
“"Securing APIs: Best Practices and Check Lists"”
Nish Majmudar
Head of Cybersecurity Architecture and Engineering BlueCross BlueShield Association
Keynote Speaker and Visionary leader with over 25 years of experience in Information Technology specializing in Cyber Security Engineering and Operations, Security Management, Risk Management, Privacy and Data Protection, Identity and Access Management, Application Security, Network Security and Endpoint Security.
CISO/Industry Leader Panel
“Cybersecurity Leaders and Experts on Current Cyberthreats and Practices”
Rohit Rajpara
CISO RIA Custody Division Goldman Sachs
Nish Majmudar
Head of Cybersecurity Architecture and Engineering BlueCross BlueShield Association
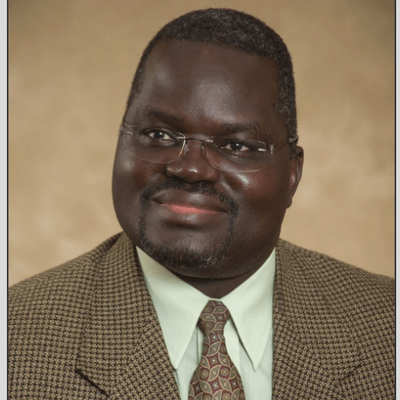
John Opala, PhD
Vice President of IT Security McCormick & Company
Jitendra Chandna
Chief Information Security Officer Maryland Department of Human Services
Whitney Palacios
Director of Security Operations SBPASC CareFirst Blue Cross Blue Shield.
About the Event
FutureCon Events brings high-level Cyber Security Training discovering cutting-edge security approaches, managing risk in the ever-changing threat of the cybersecurity workforce.
Join us as we talk with a panel of C-level executives who have effectively mitigated the risk of Cyber Attacks.
Educating C-suite executives and CISOs (chief information security officers) on the global cybercrime epidemic, and how to build Cyber Resilient organizations.
“Cybersecurity is no longer just an IT problem”
Gain the latest knowledge you need to enable applications while keeping your computing environment secure from advanced Cyber Threats. Demo the newest technology, and interact with the world’s security leaders and gain other pressing topics of interest to the information security community.
The FutureCon community will keep you updated on the future of the Cyberworld and allow you to interact with your peers and the world’s security leaders.
For sponsorship opportunities email sales@futureconevents.com
Agenda
Times are subject to change
Networking
Opening Introductions | Check In | Networking
Presentation
Conducting forensic investigations in a zero-trust environment.
and agencies. Within the United State government agencies, and those doing business with government agencies have been mandated to adopt a zero-trust level of security by 2024. This presentation will cover what Zero-Trust is, how it may impact the legitimate security work being carried out by you, and how investigations may be carried out in a Zero-Trust environment.
Sponsored by

Presentation
Seize The Breach: Why breaches still occur and how to mitigate them
Breaches happen and 2021 was a record-breaking year for them. According to Identity Theft Resource Center (ITRC) research, there were 1,291 breaches publicly reported in 2021 as of Sept. 2021 compared to 1,108 breaches in 2020; that’s a 17% year-over-year increase. Meanwhile, millions are spent on security operations centers that aren’t stopping the breaches from happening. Join us for a presentation on:
- Why breaches are usually occurring
- How machine learning-driven analytics and automation technologies provide unmatched threat detection, investigation, and response (TDIR) capabilities so security teams can respond more quickly and accurately to seize the breach and mitigate damage
- A simple maturity model based on outcomes and use cases that can vastly improve Security Operations
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Zero Trust for Applications
The Zero Trust framework is based on the principle of “never trust, always verify.” Join us to learn about Zero Trust, how to adopt it for applications, and the technologies you need to take control of your environment in the fight against ransomware.
Sponsored by

Presentation
Zero Trust and Microsegmentation – Easier Than You Think
Zero Trust has got to be one of the most talked about themes in cyber security. While the term means different things to different people, there are two things that can be agreed on: it’s a journey worth taking and microsegmentation is a key pillar of that journey. The next question always is how do you get started?
Regardless of the sophistication of ransomware, the end goal is always the same: get in through a vulnerability and move laterally through your network. Join this presentation as we help peel back the layers to provide you simple steps to protect yourself from these threats that include:
- Gaining visibility to where you are the most vulnerable
- Closing risky ports
- Leveraging tools you already have in place without adding layers of complexity
While the journey can seem intimidating, we’ll help you realize that it doesn’t take a team of 100 or a PhD to deploy zero trust microsegmentation that will protect your organization and keep ransomware at bay.
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Lunch
Keynote
"Securing APIs: Best Practices and Check Lists"
Nish Majmudar
Head of Cybersecurity Architecture and Engineering BlueCross BlueShield Association
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Thank You VPN –But Times Have Changed
Remote workforces are now the norm rather than the exception. And access to applications must be seamless and secure for employees, contractors, and partners. VPNs were originally designed for a small number of trusted employees to access applications in an on-premises data center. But times have changed – workers now need access to applications in the cloud and data center from their device of choice, regardless of their location.
Join Zentry Security for an informative session about Zero Trust Network Access. You’ll learn
- What’s driving the adoption of ZTNA
- The top 10 selection criteria for a ZTNA solution
- What are some of the limitations of traditional VPNs
Sponsored by

Presentation
Optimizing the Human Element of Cybersecurity
Human error is the most common portal for cybersecurity breaches. So it stands to reason that human talent is the most valuable defense against attacks. How can organizations reduce risk by making humans the strongest link in the cyber defense line? In this session, we will be taking a deeper look at:
-
How approaches to cyber defense are changing to keep pace with the ever-evolving threats of hackers
-
What motivates cyber professionals
-
How to make humans the strongest link in the cyber defense line
Sponsored by
Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!
Presentation
Take Control of Email Security with Human Layer Security Protection
Email is every bit as crucial an environment to protect as the network and databases because, once compromised, there can be lasting, costly, and damaging effects. Leaning on built in security controls of email platforms or legacy technology are insufficient in providing comprehensive protection against human-related threats over email. Over 75% of firms report that 20% or more of email security incidents get past their existing security controls and they spend on average 600 hours a month in investigation and remediation. However, organizations that deploy Human Layer Security technology feel more prepared to face email security threats and data loss incidents (accidental, negligent, or malicious) with their current tool setup than those who don’t, demonstrating a higher level of maturity when it comes to their readiness to prevent these damaging threats. Human Layer Security is the missing link for today’s enterprise email security stacks. Forrester recommends that organizations consider human layer security to be used.
Sponsored by

Presentation
The Boulevard of Broken Buckets
Sponsored by

Networking
Sponsor Networking Time
Visit Sponsor Booths – find amazing people, information, and prizes! Get updated on the latest technologies!